I'm Kanishka Khandelwal, an Application Security Engineer and security researcher focused on web & API security testing, bug bounty hunting, and vulnerability research. In this OWASP Top 10 series, I'll be sharing practical real-world attack techniques, exploitation methods, and mitigation strategies to help understand modern web security deeply.
Introduction
Modern web applications are built around trust boundaries.
Applications trust: users, sessions, roles, APIs, frontend restrictions, object identifiers, backend authorization logic, and internal services.
Broken Access Control occurs when these trust assumptions fail.
According to OWASP, Broken Access Control is one of the most dangerous vulnerabilities in modern applications because it directly affects authorization — the mechanism responsible for deciding who can access what.
Unlike vulnerabilities that rely heavily on payloads or memory corruption, Broken Access Control vulnerabilities often arise from:
- missing authorization checks,
- hidden functionality exposed through APIs
- weak tenant isolation,
- business logic mistakes,
- insecure workflows,
- role inheritance issues,
- and inconsistent backend validation.
The dangerous part is:
attackers often do not need to "hack" the application.
Sometimes they simply request resources or functionality they were never supposed to access.
And if the backend fails to validate permissions correctly, the application becomes vulnerable.
Understanding Access Control
Access control defines permissions and restrictions inside an application.
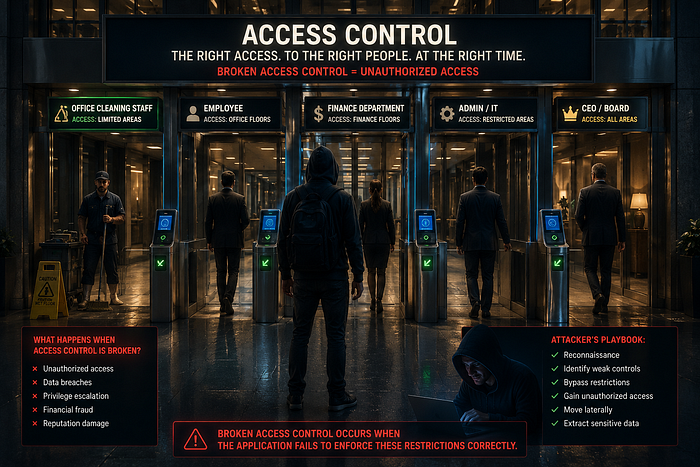
Think about a corporate office building.
Different people have different access cards:
- Cleaning staff can access maintenance areas.
- Employees can access office floors.
- Finance teams can access financial departments.
- Admins can access restricted infrastructure rooms.
- CEOs may have unrestricted access.
Now imagine:
- a cleaning staff card suddenly opens the finance department,
- an employee accesses the CEO office,
- or visitors can directly enter internal server rooms.
That is essentially what Broken Access Control looks like in web applications.
Applications constantly answer questions like:
- Can this user access admin functionality?
- Can this user modify another user's data?
- Can internal APIs be accessed externally?
- Can support staff perform admin actions?
- Can premium-only features be accessed for free?
- Can users bypass workflow restrictions?
Broken Access Control occurs when the application fails to enforce these restrictions properly.
Types of Access Control
1. Vertical Access Control
Vertical access control restricts access based on privilege levels.
Example roles:
- normal user
- moderator
- admin
- super admin
Example:
GET /admin/audit-logsIf a standard user successfully accesses this endpoint: vertical access control is broken.
2. Horizontal Access Control
Horizontal access control restricts access between users with the same privilege level.
Example: User A accesses:
GET /api/profile/9281Attacker changes:
GET /api/profile/9282If another user's profile is returned: the application suffers from IDOR (Insecure Direct Object Reference).
3. Context-Dependent Access Control
Access depends on application state or workflow.
Examples:
- skipping payment flows,
- downloading premium content without subscription,
- bypassing KYC verification,
- canceling orders after shipment,
- abusing refund workflows.
Example:
POST /api/order/cancelAn application may allow cancellation only before shipping.
But if attackers manipulate the workflow state: shipped products may still get refunded.
Why Broken Access Control Is So Dangerous
Broken Access Control vulnerabilities frequently lead to:
- account takeover,
- sensitive data exposure,
- admin access,
- internal API compromise,
- cloud resource exposure,
- tenant isolation failure,
- financial abuse,
- and business logic exploitation.
Unlike reflected vulnerabilities, authorization flaws often expose:
- real customer records,
- invoices,
- payroll data,
- internal dashboards,
- cloud infrastructure,
- private support systems.
These vulnerabilities are especially dangerous because:
the application itself performs the unauthorized action.
Common Causes
1. Frontend-Only Restrictions
Applications hide sensitive functionality in the frontend but fail to secure the backend.
Example:
if(user.role !== "admin"){
hideAdminMenu()
}Attackers directly request:
GET /api/admin/export-usersbecause the backend never validates authorization.2. Hidden Mobile APIs
Developers often assume users cannot inspect mobile applications.
But attackers reverse engineer APKs and discover hidden APIs like:
/api/mobile/internal/debug/usersIf backend authorization is weak:
- attackers access internal mobile functionality.3. Business Logic Access Control Failure
An e-commerce application hides employee discount coupons from regular users.
Frontend restriction:
hideEmployeeCoupons()But attackers manually submit:
POST /api/coupon/apply
{
"coupon":"EMPLOYEE100"
}If the backend never validates employee status: unauthorized discounts become possible.
4. JWT Authorization Misconfigurations
Applications trust JWT claims without verifying:
- signatures,
- token integrity,
- role validation.
Example:
{
"role":"admin"
}If unsigned tokens are accepted:
- attackers escalate privileges.
5. Weak Tenant Isolation
Multi-tenant SaaS applications often rely on:
- tenant IDs,
- workspace IDs,
- organization identifiers.
Example:
GET /api/tenant/alpha-company/reportsIf attackers replace:
alpha-company → victim-companyand data becomes accessible: tenant isolation is broken.
Modern Attack Surface
Broken Access Control is no longer limited to web pages. Modern targets include:
- REST APIs,
- GraphQL APIs,
- mobile applications,
- cloud dashboards,
- WebSocket servers,
- microservices,
- internal APIs,
- object storage systems,
- CDN resources.
Many modern applications secure frontend interfaces while exposing weakly protected backend APIs.
Recon Methodology Used by Attackers
1. Endpoint Enumeration
Attackers search for: undocumented APIs, admin routes, hidden dashboards, beta features, staging endpoints.
Tools:
Example:
ffuf -u https://target.com/FUZZ -w wordlist.txt2. JavaScript Recon
Modern applications expose hidden functionality inside JavaScript bundles.
Attackers search for:
- admin APIs,
- internal endpoints,
- feature flags,
- role names,
- hidden parameters.
Example:
/api/internal/export-financial-report3. Feature Flag Abuse
Applications often deploy hidden beta features.
Frontend disables access:
feature_enabled = falseBut backend endpoints remain accessible:
GET /api/beta/admin/reportsAttackers directly abuse hidden functionality.
4. WebSocket Authorization Testing
Modern applications use WebSockets for:
- chats,
- dashboards,
- support systems,
- notifications.
Example:
{
"action":"join_room",
"room":"executive-board"
}If authorization checks are missing: attackers join restricted communication channels.
Real-World Exploitation Workflow
A common exploitation flow looks like:
- Register low-privilege account
- Enumerate APIs
- Analyze JavaScript files
- Discover hidden functionality
- Manipulate identifiers
- Test role boundaries
- Abuse workflow logic
- Escalate privileges
- Access sensitive resources
IDOR — One Form of Broken Access Control
IDOR occurs when applications expose internal object references without validating ownership.
Example:
GET /api/document/8821If attackers can access another user's confidential document: authorization validation is broken.
But modern Broken Access Control vulnerabilities extend far beyond simple IDORs.
Advanced Broken Access Control Scenarios
1. Support Staff Privilege Escalation
A support employee can normally:
- reset passwords,
- manage tickets,
- verify accounts.
But backend APIs accidentally allow:
POST /api/admin/promote-userbecause support roles inherited admin permissions internally.
Result:
- support staff becomes administrator.
2. Cloud Storage Authorization Failure
Applications generate predictable cloud storage URLs:
https://storage.example.com/reports/q1-finance.pdfIf storage buckets lack proper access control:
- attackers enumerate confidential reports directly.
3. Premium Feature Bypass
Streaming platform:
- hides premium videos from free users.
Attackers directly access:
/cdn/premium/masterclass.mp4because CDN authorization is missing.
4. Race Condition Authorization Bypass
Banking application allows one withdrawal request at a time:
POST /api/withdrawAttackers send 20 simultaneous requests.
Due to race conditions:
- balance validation fails,
- multiple withdrawals succeed.
5. OAuth Scope Misconfiguration
Application validates only token presence:
Authorization: Bearer tokenbut fails to validate scopes properly.
Low-privileged OAuth tokens access:
/api/admin/export-usersresulting in privilege escalation.
GraphQL Access Control Issues
GraphQL APIs frequently suffer from:
- excessive data exposure,
- resolver-level authorization flaws,
- field-level access control failures.
Example:
query{
employee(id:"17"){
name
salary
performance_notes
termination_reason
}
}Employees may be authorized to view:
- names,
- departments.
But not:
- salaries,
- HR notes,
- termination records.
If field-level authorization is missing:
- sensitive internal information leaks.
Cloud & Microservice Risks
Modern architectures rely heavily on internal trust.
Common issues include:
- trusted internal headers,
- insecure API gateways,
- exposed Kubernetes dashboards,
- weak service-to-service authentication,
- misconfigured RBAC systems.
Example:
X-Internal-User: adminIf internal headers are trusted externally:
- attackers impersonate privileged services.
Tools Used by Security Researchers
Burp Suite
Used for: authorization testing, request replay, parameter manipulation, session analysis.
ffuf
Used for: endpoint discovery, hidden route enumeration, forced browsing.
Caido
Useful for: API testing, workflow analysis, replay attacks.
jwt_tool
Used for: JWT testing, signature validation, role manipulation checks.
Famous Real-World Cases
Facebook Business Logic & Access Control Bugs
Researchers discovered multiple authorization flaws involving:
- page management,
- business manager permissions,
- asset ownership validation.
These vulnerabilities enabled:
- unauthorized business actions,
- privilege escalation,
- restricted asset access.
Microsoft Power Apps Data Exposure
Improper backend authorization exposed millions of records publicly.
Exposed information included:
- vaccination data,
- employee records,
- government datasets.
Root cause:
- weak access control enforcement.
Mitigation Strategies
1. Enforce Authorization Server-Side
Never trust:
- frontend restrictions,
- hidden buttons,
- client-side checks,
- disabled UI elements.
Always validate authorization on the backend:
if current_user.id != resource.owner:
deny_access()2. Implement Proper RBAC
Use centralized authorization systems.
Avoid:
- scattered permission checks,
- inconsistent access logic,
- inherited role confusion.
3. Deny By Default
Applications should reject access unless explicitly allowed.
4. Validate Every Request
Every request should validate:
- user identity,
- ownership,
- roles,
- tenant boundaries,
- workflow state.
5. Secure Internal APIs
Never assume:
- internal APIs are unreachable,
- mobile endpoints remain hidden,
- internal headers cannot be spoofed.
Detection & Blue Team Perspective
Security teams should monitor:
- abnormal object enumeration,
- unusual role changes,
- tenant switching behavior,
- API traversal patterns,
- excessive 403 responses,
- hidden endpoint access attempts.
SIEM detections may include:
- unauthorized admin API access,
- sequential identifier requests,
- suspicious WebSocket subscriptions,
- repeated workflow bypass attempts.
Bug Bounty Researcher Notes
Broken Access Control remains one of the highest-value vulnerability categories in bug bounty programs.
Researchers actively hunt for:
- IDOR,
- hidden APIs,
- GraphQL authorization flaws,
- tenant escapes,
- support privilege escalation,
- feature flag abuse,
- OAuth misconfigurations,
- cloud storage exposure.
Strong reports usually contain:
- clear privilege boundaries,
- real business impact,
- reproducible exploitation,
- proof of unauthorized actions.
Labs & Practice Resources
PortSwigger Web Security Academy
Excellent labs covering: IDOR, privilege escalation, access control bypass, business logic abuse.
OWASP Juice Shop
Modern vulnerable application for practicing security testing.
DVWA
Good environment for learning authorization flaws and web vulnerabilities.
Final Thoughts
Broken Access Control is dangerous because applications frequently assume:
authenticated users are trustworthy users.
But authentication alone does not guarantee authorization.
Modern attackers abuse: hidden APIs, workflow flaws, cloud trust assumptions, internal services, weak tenant isolation, feature flags, business logic mistakes, and inconsistent backend validation.
As applications become increasingly API-driven and cloud-native, Broken Access Control continues to remain one of the most impactful vulnerabilities in modern security testing.
Thank You for Reading
I'll be covering the entire OWASP Top 10 deeply with: advanced exploitation techniques, real-world attack methodology, bug bounty insights, mitigation strategies, practical case studies, and modern application security concepts.
If you enjoyed this article, enable notifications to follow the upcoming OWASP Top 10 series.
Connect with me on LinkedIn:
Kanishka Khandelwal on LinkedIn
Don't forget to clap 👏