Note: This article was written with the assistance of AI tools for drafting and research. The final content was reviewed, edited, and fact-checked by the author.
Open a modern security operations center (SOC), and you'll probably see something that looks straight out of a movie.
Multiple monitors. Dashboards full of numbers. Streams of strange-looking text.
To an outsider, it might look like cybersecurity analysts spend their day staring at screens filled with random data.
In reality, those screens are telling a story.
Every login attempt, file download, network connection, and system event leaves behind a small digital record called a log.
Security analysts study these logs to answer a very important question:
"Is something suspicious happening in this system?"
Organizations rely on Security Operations Center (SOC) analysts to monitor networks, detect threats, and respond to cyber incidents before they become disasters.
SOC teams continuously monitor system activity to detect malicious behavior and coordinate responses to cybersecurity incidents.
So what exactly are security analysts looking at all day?
Let's take a look behind the scenes.
1. What a SOC Analyst Actually Does
A SOC analyst is essentially the digital equivalent of a security guard.
But instead of watching doors and surveillance cameras, they monitor networks, servers, and user activity.
Their main responsibilities include:
- Monitoring security alerts
- Analyzing logs and events
- Investigating suspicious behavior
- Responding to incidents
- Escalating threats to senior analysts
SOC analysts usually work in shifts because cyber threats don't follow office hours.
Hackers operate 24/7.
Which means defenders must do the same.
In simple terms:
They are the first people who notice when something strange is happening in a network.
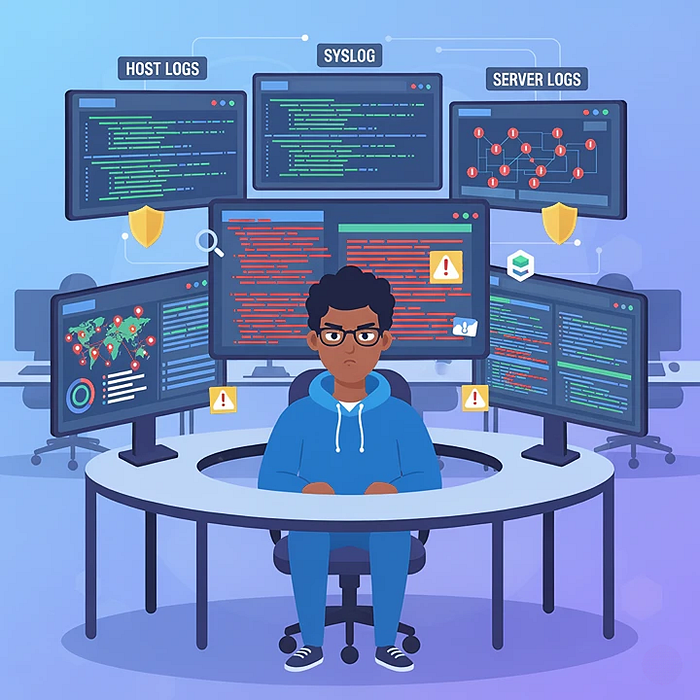
2. Understanding the Different Types of Logs

Logs are the raw material of cybersecurity monitoring.
A log is simply a record of events generated by systems, applications, or devices.
Security analysts typically monitor several types of logs, including:
- Host Logs: These logs come from individual devices such as laptops or servers. They record activities like user logins, file access, and system changes.
- Syslog: Syslog is a widely used logging standard that collects messages from network devices such as routers, firewalls, and switches.
- Server Logs: Web servers, application servers, and databases generate logs that record user requests, errors, and system operations.
For a security analyst, these logs are like security camera footage for a computer system.
They show exactly what happened.
3. How Logs Reveal Suspicious Behavior
At first glance, logs may look like random technical text.
But to trained analysts, they can reveal important clues.
For example, suspicious patterns might include:
- Hundreds of failed login attempts
- Logins from unusual geographic locations
- Large file transfers at strange hours
- Unexpected administrator activity
These patterns may indicate:
- Brute-force attacks
- Compromised accounts
- Malware activity
- Insider threats
The MITRE ATT&CK framework documents many attacker techniques that can be detected through log analysis.
Security analysts essentially act as detectives.
They look for behavior that doesn't match normal activity.
4. Security Monitoring with SIEM Tools

Monitoring thousands of systems manually would be impossible.
This is where SIEM tools come in.
SIEM stands for Security Information and Event Management.
These platforms collect logs from across an organization and analyze them in real time.
Popular SIEM platforms include:
- Splunk
- IBM QRadar
- Microsoft Sentinel
- Elastic Security
According to IBM Security, SIEM systems aggregate security data from multiple sources and analyze it to detect suspicious activity.
Instead of reading logs individually, analysts use dashboards that automatically highlight potential threats.
Think of SIEM as a radar system for cybersecurity.
It scans the environment and alerts analysts when something unusual appears.
5. Detecting Anomalies in Massive Data Logs

Large organizations generate enormous amounts of logs every day.
We're talking about millions — sometimes billions — of events daily.
No human could read all of them.
Instead, SIEM platforms and analytics tools help identify anomalies — activities that deviate from normal behavior.
Examples include:
- A user downloading unusually large amounts of data
- An employee logging in from two countries within minutes
- A server communicating with suspicious IP addresses
According to the NIST Cybersecurity Framework, continuous monitoring and anomaly detection are essential components of modern cybersecurity defense.
The analyst's job is to determine:
Is this activity legitimate?
Or is it an attack?
Sometimes it's just a misconfigured system.
Sometimes it's the beginning of a breach.
6. How Incidents Are Escalated Inside SOC Teams

Not every alert is a real attack.
SOC analysts must constantly decide which alerts deserve deeper investigation.
This process is called triage.
A typical SOC escalation process looks like this:
- Tier 1 Analysts: Monitor alerts and investigate basic incidents.
- Tier 2 Analysts: Perform deeper analysis and threat investigation.
- Tier 3 Analysts: Handle advanced threats, malware analysis, and sophisticated attacks.
According to guidance from SANS Institute, effective SOC operations rely on structured escalation workflows to ensure threats are handled by the appropriate expertise level.
If a real incident is confirmed, the SOC team coordinates with:
- Incident response teams
- IT administrators
- Management
Because once a threat is verified, the goal becomes simple:
Stop the attack before damage spreads.
Final Thoughts
Security analysts don't spend their day "just staring at logs."
They are constantly monitoring signals hidden inside massive streams of system data.
Every login, file access, and network connection creates a small clue.
Most of the time, those clues mean nothing.
But occasionally, they reveal the first sign of a cyberattack.
And when that happens, the SOC analyst is often the first line of defense protecting an organization's systems and data.
So the next time you hear the term log monitoring or SIEM analysis, remember:
Behind those dashboards are analysts quietly watching the digital world for threats most people never notice.
If you enjoyed this article, follow me for more insights about:
- Cybersecurity threats
- Social engineering techniques
- Data breaches and hacking methods
- Online privacy and digital security