Learning Objectives:
- Understand various types of IDOR Vulnerabilities
- Learn how to secure the system from an IDOR attack
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
This room consists of 7 tasks: 1. What is an IDOR? 2. An IDOR Example 3. Finding IDORs in Encoded IDs 4. Finding IDORs in Hashed IDs 5. Finding IDORs in Unpredictable IDs 6. Where are IDORs located 7. A Practical IDOR Example
I will walkthrough each room with my own answer method
===============================================================
- Task 1: What is an IDOR?
IDOR basically stands for Insecure Direct Object Reference, and can be considered as one of the type of access control vulnerability.
This vulnerability can occur when a web server puts too much trust on the input data, instead of still validating them one by one on the server-side whether the requested object actually belongs to the user requesting it.
Q1) What does IDOR stand for?
Answer: Insecure Direct Object Reference
===============================================================
- Task 2: An IDOR Example
In this task, we will be given the static web by THM to know the more detail of IDOR
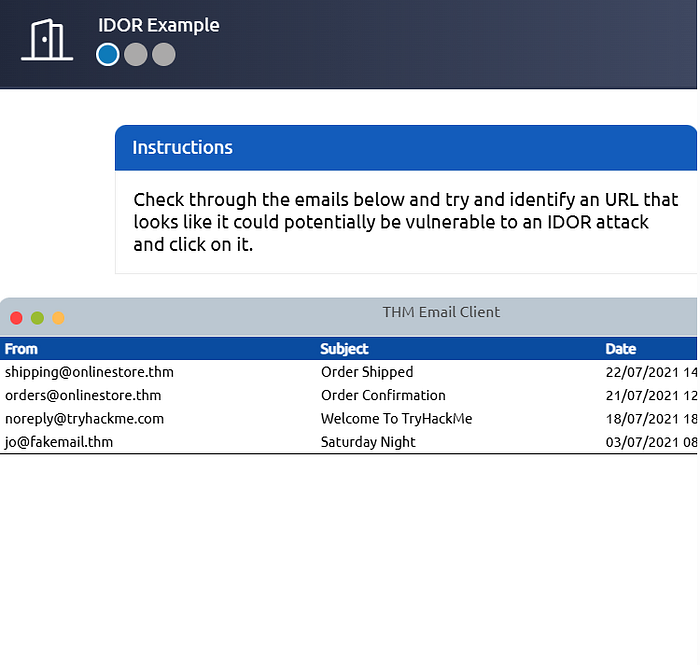
And when we click the second email of orders, we will see this interface
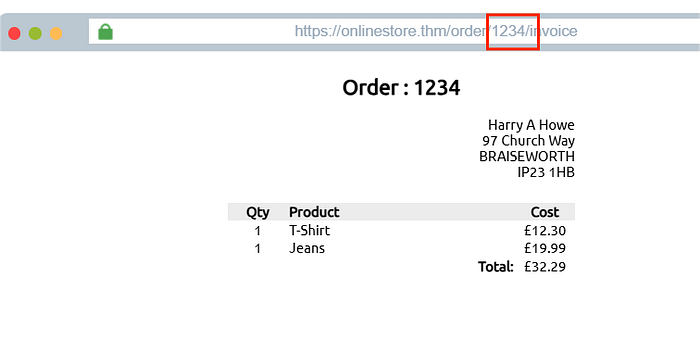
By following the instruction, we need to change the "1234" ID to "1000" on the link, then click refresh
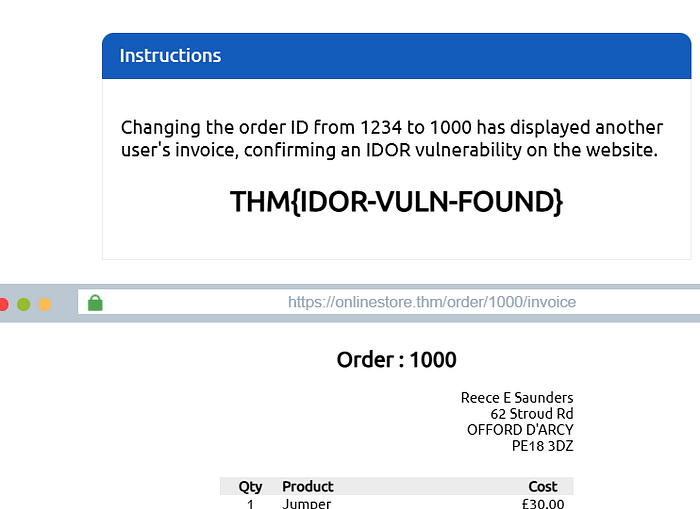
And yep, we can successfully request the OBJECT that actually doesn't belong to us. This occurs because of the lack of further verification on the requested object (or called IDOR). And we successfully got the flag!
Q1) What is the Flag from the IDOR example website?
Answer: THM{IDOR-VULN-FOUND}
===============================================================
- Task 3: Finding IDORs in Encoded IDs
When passing data from page to page either by post data, query strings, or cookies, web developers will often first take the raw data and encode it, usually by base64 technique. This is quite dangerous because the attacker could easily spot it, for example by firstly decode the encoded value, then change the value, then encode it back. This illustration could be seen like the image below.

Q1) What is a common type of encoding used by websites?
Answer: base64
===============================================================
- Task 4: Finding IDORs in Hashed IDs
Hashed IDs are a little bit more complicated than the encoded one. First, because it is one way(irreversible), and the second thing, there are many different methods of hashing. The weakest one is md5, as we could crack it easily by using https://crackstation.net .
Q1) What is a common algorithm used for hashing IDs?
Answer: md5
===============================================================
- Task 5: Finding IDORs in Unpredictable IDs
If the two methods above are not working, we could try this way, where we could create 2 accounts and swap the ID among them. If we end up be able to see the other account's content using its ID number while still logged in with a different account, it means we have found the IDOR vulnerability.
Q1) What is the minimum number of accounts you need to create to check for IDORs between accounts?
Answer: 2
===============================================================
- Task 6: Where are IDORs located
As we have learnt so far, the vulnerable endpoint that we are targetting is not always located in the address bar.
For example, we may notice a call to /user/details which is displaying our user information. But through an attack known called parameter mining, we discover a parameter called user_id that we can use to display other users' information (e.g. /user/details?user_id=123)
Q1) Read the above.
Answer: no answer needed
===============================================================
- Task 7: A Practical IDOR Example
In this task, we are given the VM to test our knowledge about what we have learnt so far
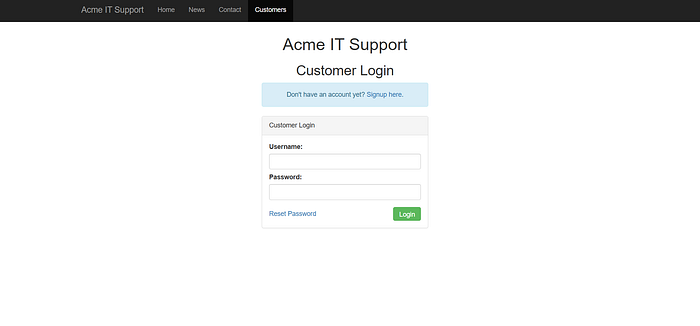
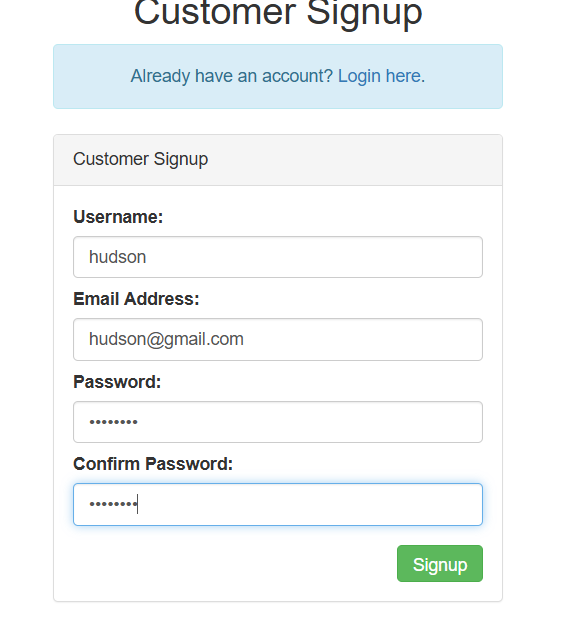
First, we need to create a new account and log in first
Afterwards, let's navigate to the Your Account tab, which can be seen on the image below
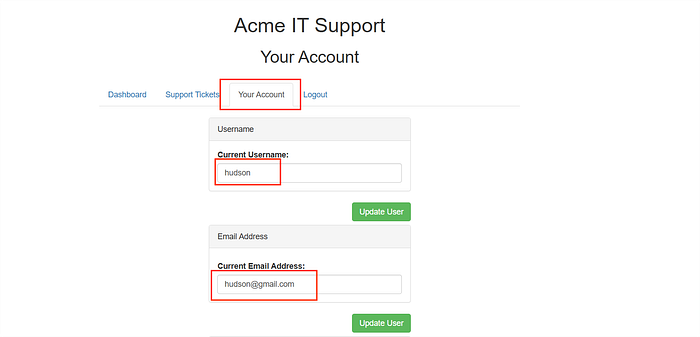
As we can see, the forms above are prefilled with our usn and email addr right? We could explore further codes behind this.
By navigating to Inspect -> Network tab, we could see the JS code that did this
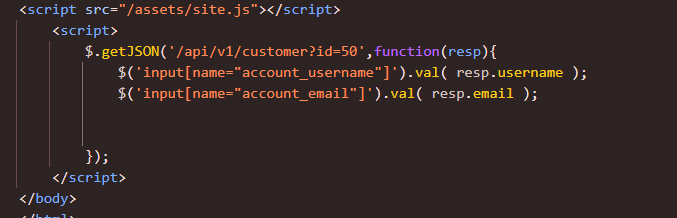
You can see the path of /api/v1/customer?id=50, and we could type it onto the URL address bar, as we can see on the image below

Q1) What is the username for user id 1?
now, we need to change the id value to 1, utilizing this IDOR vulnerability

Answer: adam84
Q2) What is the email address for user id 3?
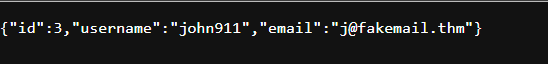
Answer: j@fakemail.thm
===============================================================