How to Find Open Redirect Vulnerabilities (And Make $100–$500+ From Them)
🔥 Introduction
Most people use Google to explore websites.
But cybersecurity professionals use tools like Shodan to discover exposed systems, misconfigurations, and hidden attack surfaces.
Here's the truth:
👉 If a system is exposed, it's a potential target. 👉 And one of the most overlooked vulnerabilities hiding in plain sight is — Open Redirect.
It may look simple… but when combined with phishing, OAuth bypass, or token stealing, it becomes highly impactful.
💰 And yes — bug bounty platforms pay $100 to $500+ for valid reports.
⚠️ What is an Open Redirect Vulnerability?
An Open Redirect occurs when a website allows users to redirect to any external URL without proper validation.
Example:
https://example.com/redirect?url=https://evil.comIf the website redirects users to evil.com without validation — it's vulnerable.
💡 Why Open Redirects Matter

Many beginners ignore this vulnerability. That's a mistake.
Because Open Redirects can be used for:
- 🎣 Phishing attacks (trusted domain → malicious site)
- 🔐 OAuth token theft
- 📩 Email bypass in password reset flows
- 🕵️ Bypassing security filters
- 📈 Chaining with other vulnerabilities
👉 Companies pay not just for the bug — but for the impact you demonstrate.
🔍 Step-by-Step: How to Find Open Redirect Vulnerabilities

1️⃣ Find Targets (Google + Shodan Method)
Use Google Dorks:
inurl=redirect
inurl=redirect?url=
inurl=next=
inurl=return=
inurl=continue=Use Shodan to find exposed apps:
- Look for login panels
- Admin dashboards
- API endpoints
👉 Combine both to find less secure or misconfigured systems
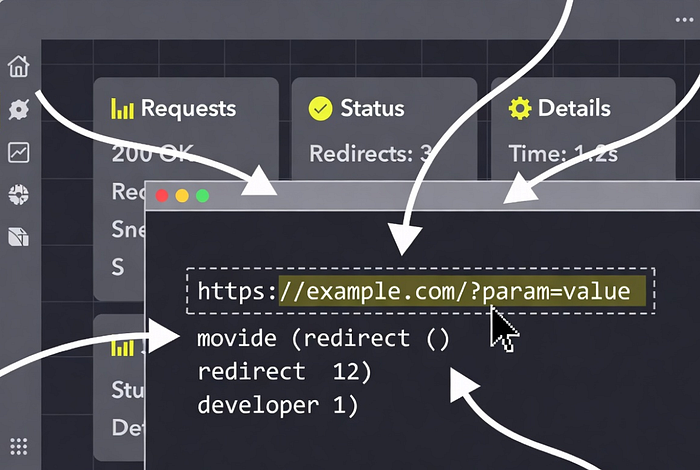
2️⃣ Identify Redirect Parameters
Common parameters:
redirect=
url=
next=
return=
continue=
dest=
target=Example:
https://target.com/login?next=/dashboard3️⃣ Test for Open Redirect
Replace parameter value with your own domain:
https://target.com/login?next=https://evil.com✅ If it redirects → Vulnerable
4️⃣ Bypass Filters (Advanced Practical Tricks)
Some sites block direct URLs. Try bypassing:
🔹 Using // (protocol-relative)
https://target.com?redirect=//evil.com🔹 Encoding
https://target.com?redirect=https%3A%2F%2Fevil.com🔹 Adding @
https://target.com?redirect=https://target.com@evil.com🔹 Using subdomains
https://evil.com.target.com👉 These tricks help bypass weak validation filters.
5️⃣ Increase Impact (This is where MONEY comes)
A simple redirect = low severity A real attack scenario = higher payout
🔥 Example Attack Chain:
- Victim clicks trusted link:
https://trusted.com/redirect?url=https://evil.com- Redirects to fake login page
- User enters credentials
- Attacker steals data
💰 This turns a low bug into a high-value report
💸 How to Make $100–$500+ from Open Redirect

To earn money:
✅ Don't just report:
"Open redirect exists"
✅ Instead show:
- Real exploitation scenario
- Phishing demo
- OAuth abuse (if possible)
- Impact explanation
Example Report Line:
"This open redirect can be used to craft phishing links on a trusted domain, increasing user trust and leading to credential theft."
👉 This is what bounty hunters do differently.
🧠 Pro Tips (From Real Bug Hunters)
- Always test login & signup flows
- Check email verification links
- Test password reset redirects
- Combine with XSS or OAuth
- Look in mobile APIs & hidden endpoints
🚀 Final Thoughts
Google helps you find websites But tools like Shodan help you find opportunities
And vulnerabilities like Open Redirect are:
✔ Easy to find ✔ Beginner-friendly ✔ Highly practical ✔ Monetizable with the right approach
👉 The difference between beginners and professionals is simple:
Beginners find bugs Professionals show impact
📢 Call to Action
If you want more real-world cybersecurity techniques, bug bounty tips, and earning strategies:
👉 Join my Telegram for daily practical content 👉 Visit my website for step-by-step hacking guides
💡 Start practicing today — because in cybersecurity, skills = income
