In today's digital world, cybersecurity threats are increasing rapidly. Organizations store large amounts of sensitive information online, including customer data, financial records, and confidential documents. Because of this, companies must constantly evaluate their systems for vulnerabilities.
One of the most effective ways to test system security is penetration testing. Penetration testing simulates real cyberattacks to identify weaknesses before malicious hackers can exploit them.
A critical stage of penetration testing is Information Gathering, also known as Reconnaissance. This phase involves collecting as much information as possible about a target system, network, or organization.
In this article, we will explore:
- What penetration testing is
- Penetration testing methodology
- What information gathering means
- Passive vs Active information gathering
- Steps of information gathering
- Types of information that can be collected
- Tools used for information gathering
This guide is written in simple language with practical examples so beginners can easily understand the concepts.
What is Penetration Testing?
Penetration testing, commonly called pentesting, is a cybersecurity process where ethical hackers attempt to exploit vulnerabilities in a system to evaluate its security.
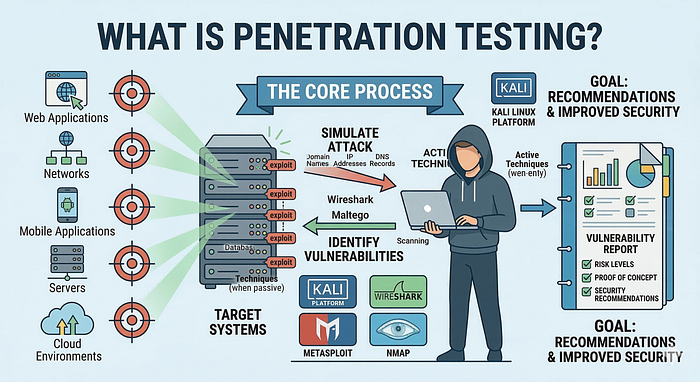
Instead of waiting for attackers to find weaknesses, organizations hire security professionals to simulate attacks and identify vulnerabilities early.
Penetration testing can target different systems, such as:
- Web applications
- Networks
- Mobile applications
- Servers
- Cloud environments
Security professionals often use specialized platforms like Kali Linux and tools such as Metasploit, Nmap, and Wireshark.
The ultimate goal of penetration testing is to identify vulnerabilities and provide recommendations to improve security.
Penetration Testing Methodology
Penetration testing follows a structured process known as penetration testing methodology. This methodology ensures that security testing is systematic, repeatable, and effective.
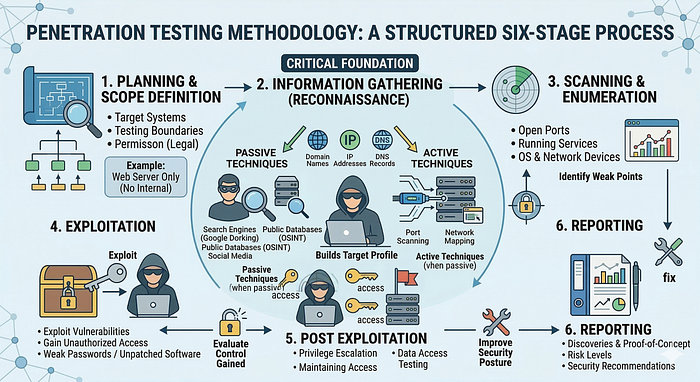
Most cybersecurity frameworks divide penetration testing into several stages.
1. Planning and Scope Definition
This stage defines the objectives of the penetration test.
Important elements include:
- Target systems
- Testing boundaries
- Permission from the organization
- Legal considerations
Example:
A company may request testing only on its web server while excluding internal networks.
2. Information Gathering (Reconnaissance)
Information gathering is the process of collecting data about the target system.
This phase helps penetration testers understand:
- Network infrastructure
- Server technologies
- Domain information
- Potential attack surfaces
This stage forms the foundation for the entire penetration testing process.
3. Scanning and Enumeration
In this phase, testers identify:
- Open ports
- Running services
- Operating systems
- Network devices
Scanning tools help detect possible vulnerabilities in the target system.
4. Exploitation
Exploitation involves attempting to exploit identified vulnerabilities.
For example:
- Weak passwords
- Unpatched software
- Misconfigured services
Attackers use vulnerabilities to gain unauthorized access.
5. Post Exploitation
Once access is obtained, testers determine how much control they can gain.
Activities may include:
- Privilege escalation
- Data access testing
- Maintaining access
6. Reporting
The final stage involves documenting all findings.
The penetration testing report usually includes:
- Vulnerabilities discovered
- Risk levels
- Proof of concept
- Security recommendations
What is Information Gathering?
Information gathering, also known as reconnaissance, is the first technical stage of penetration testing.

In this phase, the tester collects information about the target organization.
The goal is to understand the structure and technology of the target system.
Information gathered may include:
- Domain names
- IP addresses
- DNS records
- Network infrastructure
- Server technologies
- Employee information
- Email addresses
Example scenario:
Suppose a penetration tester is testing the security of:
examplecompany.comBefore attempting any attack, the tester collects information such as:
- The hosting provider
- Server location
- Technologies used
- Subdomains
- Open ports
This intelligence helps testers identify potential attack points.
Types of Information Gathering
Information gathering is generally divided into two main categories:
- Passive Information Gathering
- Active Information Gathering
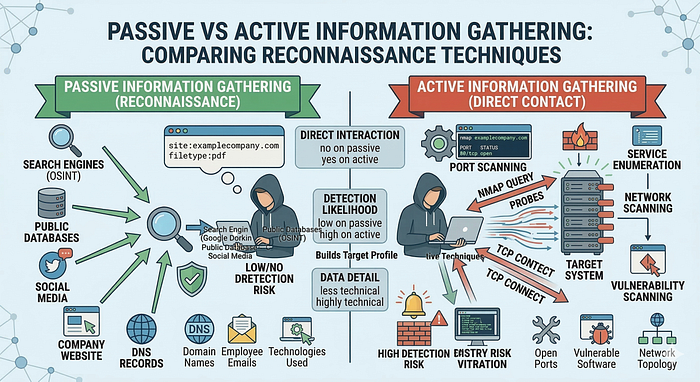
Understanding the difference between these two techniques is important for ethical hackers and cybersecurity professionals.
Passive Information Gathering
Passive information gathering involves collecting information without directly interacting with the target system.
This means the target organization typically cannot detect the activity.
Instead of contacting the target server, testers gather data from public sources.
Examples include:
- Search engines
- Public databases
- Social media
- Company websites
- DNS records
Passive reconnaissance is often referred to as OSINT (Open Source Intelligence).
Example of Passive Information Gathering
A penetration tester might use search engines to find sensitive data about a company.
Example search query:
site:examplecompany.com filetype:pdfThis search may reveal:
- Internal documents
- Reports
- Technical manuals
These documents may contain valuable information for attackers.
Advantages of Passive Information Gathering
Passive reconnaissance offers several advantages:
- No interaction with the target system
- Minimal risk of detection
- Completely legal when using public information
Limitations of Passive Information Gathering
However, passive techniques also have limitations:
- Limited technical information
- Cannot identify open ports
- Cannot detect vulnerabilities directly
For deeper analysis, testers must use active information gathering.
Active Information Gathering
Active information gathering involves direct interaction with the target system.
This includes sending requests to the target network or server.
Because the tester interacts directly with the system, the activity may be detected by security monitoring tools.
Active reconnaissance techniques include:
- Port scanning
- Network scanning
- Service enumeration
- Vulnerability scanning
Example of Active Information Gathering
A penetration tester may scan the target system using Nmap.
Example command:
nmap examplecompany.comThis command identifies:
- Open ports
- Running services
- Operating system information
Advantages of Active Information Gathering
Active techniques provide:
- Detailed technical information
- Discovery of vulnerabilities
- Insight into network structure
Disadvantages of Active Information Gathering
However, active scanning has some risks:
- Activity may be logged by security systems
- Intrusion detection systems may trigger alerts
- Requires permission before testing
Steps of Information Gathering
Information gathering usually follows a structured sequence.
Below are the most common steps used by penetration testers.
Step 1: Identify the Target Domain
The first step is identifying the organization's domain name.
Example:
examplecompany.comUsing domain lookup services, testers can discover:
- Domain ownership
- Registration information
- Hosting provider
- Name servers
Step 2: Discover Subdomains
Organizations often operate multiple subdomains.
Examples include:
mail.examplecompany.com
shop.examplecompany.com
blog.examplecompany.comEach subdomain may run different applications or services.
Discovering subdomains expands the potential attack surface.
Tools like Amass help automate this process.
Step 3: Collect IP Addresses
Every online system is associated with an IP address.
Example:
192.168.1.10Identifying IP addresses allows testers to perform network analysis and scanning.
IP discovery also reveals:
- Server locations
- Hosting infrastructure
- Related domains
Step 4: DNS Enumeration
DNS (Domain Name System) translates domain names into IP addresses.
Analyzing DNS records may reveal:
- Mail servers
- Subdomains
- Backup servers
DNS misconfigurations can also expose sensitive information.
Step 5: Identify Open Ports
Ports allow communication between devices and services.
Common ports include:
PortService80HTTP443HTTPS22SSH21FTP
Attackers often exploit vulnerable services running on open ports.
Port scanning tools such as Nmap are commonly used.
Example:
nmap -p- examplecompany.comStep 6: Identify Technologies Used
Understanding the technologies used by a website is essential.
Websites often use platforms such as:
- WordPress
- PHP
- Apache
- Nginx
Tools like Wappalyzer help identify these technologies.
If a website uses outdated software, attackers may exploit known vulnerabilities.
Step 7: Gather Employee Information
Attackers sometimes collect employee information from public sources.
Common sources include:
- Company websites
This information can be used in social engineering attacks.
Example:
john@examplecompany.comAttackers may send phishing emails pretending to be internal staff.
Information That Can Be Collected
During the information gathering phase, penetration testers may collect various types of data.
Examples include:
Network Information
- IP addresses
- Network topology
- Server locations
Domain Information
- Domain ownership
- DNS records
- Name servers
Website Technologies
- Web frameworks
- CMS platforms
- Plugins
Employee Information
- Names
- Job roles
- Email addresses
Security Information
- Firewall presence
- Open ports
- Running services
All this information helps testers build a detailed profile of the target system.
Tools for Information Gathering
Penetration testers rely on various tools to collect information efficiently.
Below are some widely used tools.
Nmap
Nmap is one of the most popular network scanning tools.
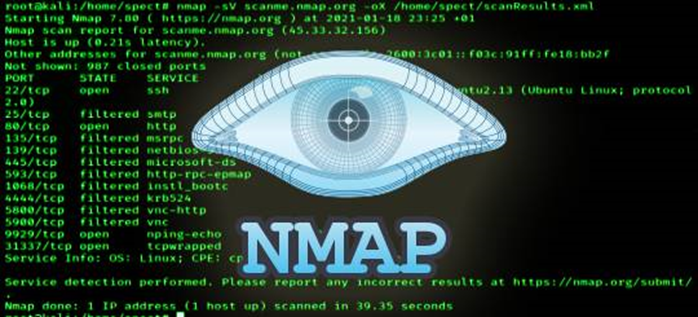
Key features include:
- Port scanning
- Service detection
- Operating system detection
Example command:
nmap -A target.comWireshark
Wireshark is a powerful network traffic analysis tool.
It captures network packets and allows detailed inspection.
Security analysts use it to:
- Detect suspicious traffic
- Analyze communication protocols
- Identify security weaknesses
Maltego
Maltego is a data mining and OSINT tool.
It helps visualize relationships between:
- Domains
- Email addresses
- IP addresses
- Organizations
Maltego is widely used in cyber investigations.
TheHarvester
TheHarvester collects emails and subdomains from public sources.
Example command:
theHarvester -d example.com -b googleThis command searches Google for information related to the domain.
Shodan
Shodan is known as the search engine for internet-connected devices.
It can identify:
- Servers
- Cameras
- IoT devices
- Databases
Security researchers often use Shodan to detect exposed systems.
Real World Example of Information Gathering
Consider a scenario where a penetration tester is assigned to evaluate the security of a company website.
Target:
examplecompany.comThe tester performs the following steps:
- Perform Google searches for public information
- Identify domain ownership
- Discover subdomains
- Collect IP addresses
- Scan ports and services
- Identify technologies used
After analysis, the tester may discover:
- The website runs WordPress
- Port 22 (SSH) is open
- Employee emails are publicly visible
These findings may lead to potential vulnerabilities.
Why Information Gathering is Critical
Information gathering is crucial for several reasons.
First, it helps testers understand the target environment.
Second, it identifies potential vulnerabilities before exploitation.
Third, it improves the efficiency of penetration testing.
Experienced ethical hackers often spend 40–60% of their time in the reconnaissance phase.
The more information collected, the easier it becomes to identify weaknesses.
Best Practices for Secure Organizations
Organizations should also understand how attackers gather information.
To reduce exposure, companies should:
- Limit public exposure of sensitive data
- Secure DNS records
- Hide unnecessary server details
- Monitor network scanning activities
- Train employees against social engineering
By implementing these measures, organizations can significantly reduce attack risks.
Conclusion
Penetration testing plays a critical role in modern cybersecurity strategies.
Among all testing phases, information gathering is the most important foundation. Without proper reconnaissance, identifying vulnerabilities becomes extremely difficult.
By using passive and active information gathering techniques, security professionals can collect valuable intelligence about target systems.
Tools such as Nmap, Wireshark, Maltego, and Shodan help automate and enhance the reconnaissance process.
Organizations must also understand these techniques so they can protect their systems from potential attackers.
Cybersecurity is not only about defending systems but also about understanding how attacks work and preparing against them.