In the morden digital world the web application plays a major role and they have both positive and negative pace . One of the most widely dangerous attack is Injection and mainly of SQL Injection.
What is Injection?
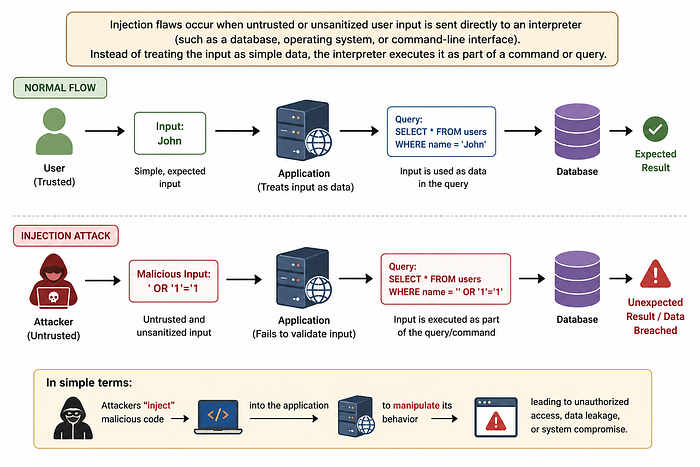
Injection attacks occur when attackers exploit vulnerabilities in an application to send malicious code into a system. This type of exploit may allow them to execute unauthorized commands, access data, or manipulate the system's operations. Because injection attacks can be very dangerous — and because they're widespread in use — they present a critical threat to cybersecurity today.
What is SQL injection?
SQL injection testing checks if it is possible to inject data into an application/site so that it executes a user-controlled SQL query in the database. Testers find a SQL injection vulnerability if the application uses user input to create SQL queries without proper input validation. Successful exploitation of this class of vulnerability allows an unauthorized user to access or manipulate data in the database, which if you didn't know already is quite bad.
Example Scenario:
Imagine a login system that uses the following SQL query:
SELECT * FROM users WHERE username = 'input' AND password = 'input'
If the application does not validate inputs, an attacker can enter:
username: admin
password: ' OR Ƈ'=Ƈ
This changes the query logic and may allow the attacker to log in without valid credentials.
Dangers of SQL Injection:
1)Data Theft and Leaks
2)Data Modification
3)Data Loss or Destruction
4)Infrastructure Compromise
At some cases the attacker can have the control over the entire system and it's infrastructure.
Real World Example:Yahoo Data Breach(2013–2014)
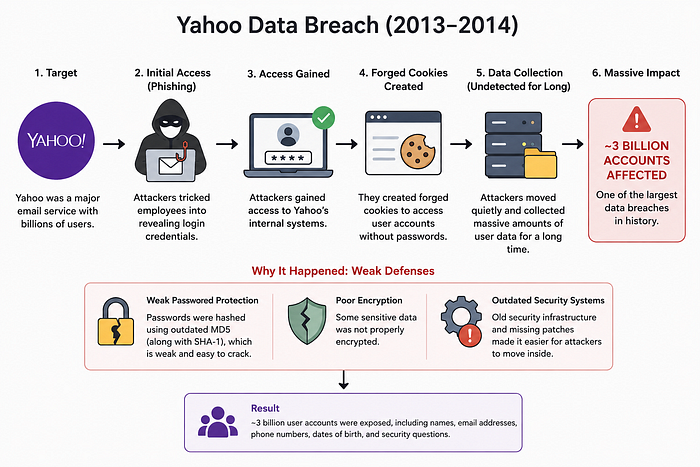
Yahoo data breach is a huge level of attack happened at that time in which every single users data were getting affected probably 3 billion accounts were affected.
The Yahoo data breach of 2013–2014 is often remembered as one of the biggest wake-up calls in cybersecurity. At the time, Yahoo was one of the most widely used email services in the world, which made it a huge target for attackers. What made this incident even more shocking wasn't just the scale — it was how long it went unnoticed.
The Yahoo breach didn't happen because of just one mistake — it was a combination of smart attackers and weak defenses. Investigations later suggested that the 2014 attack was likely carried out by state-sponsored hackers, with the U.S. charging Russian agents for their involvement.
The attackers first gained access using techniques like phishing, where they tricked employees into revealing credentials. Once inside, they didn't rely only on passwords. They created forged cookies, which allowed them to log into user accounts without needing the actual password — making the attack harder to detect.
What made things worse was Yahoo's outdated security setup. Passwords were protected using weak hashing methods like MD5, and some sensitive data wasn't properly encrypted. These gaps made it much easier for attackers to move through the system and collect massive amounts of user data without being noticed for a long time.
Remediation for SQL Injection Vulnerabilities
Preventing SQL Injection requires secure coding practices and proper security controls. Below are some effective remediation techniques used in real-world applications.
1. Use Parameterized Queries (Prepared Statements)
Parameterized queries separate user input from SQL commands, ensuring the database treats input only as data and not as executable code.
SELECT * FROM users WHERE username = ? AND password = ?;This is one of the most effective ways to prevent SQL Injection.
2. Validate and Sanitize User Input
Applications should never trust user input directly.
Developers should:
- Restrict special characters
- Validate input length and format
- Reject unexpected data types
For example, a phone number field should only accept numeric values.
Conclusion:
SQL injection has been a common attack and they are being happened till the date and they are not just common because they are advance they need a very tiny loop hole to enter
At many cases the these attack happen with a simple mistake of trusting user input and proper security checck during the time of data storing.Even a single small mistake can be a easy way for the attacker to enter into the data.
At its core, the lesson is pretty straightforward: treat all user input with caution. Taking a little extra care — validating inputs, using safer query methods, and testing properly — can make a huge difference. It's a reminder that even the oldest attack methods can still work if the basics are ignored.