Palo Alto PAN-OS RCE Vulnerability attacks are already hitting exposed firewalls. Security teams are racing to patch systems before attackers gain root-level access and move deeper into enterprise networks.
We spent several hours reviewing exploitation patterns, firewall telemetry, and attack-chain behavior linked to CVE-2026–0300. What we found is worrying. This flaw targets one of the most trusted perimeter security platforms used by enterprises, schools, hospitals, and cloud providers across the United States.
The Palo Alto PAN-OS RCE Vulnerability identified as CVE-2026–0300 is now being actively exploited in the wild. Attackers can reportedly execute malicious code remotely without authentication on vulnerable firewall systems.
This article breaks down what the flaw does, which PAN-OS versions are affected, how exploitation works, and what defenders should do immediately. If your organization relies on Palo Alto firewalls, this deserves urgent attention.
What Is the Palo Alto PAN-OS RCE Vulnerability?
The Palo Alto PAN-OS RCE Vulnerability is a critical remote code execution flaw tied to the User-ID Authentication Portal in PAN-OS firewalls. The vulnerability allows unauthenticated attackers to send specially crafted requests that may trigger a buffer overflow and execute code with elevated privileges.
Because these devices often sit at the network edge, exploitation could expose entire enterprise environments. Threat actors can potentially gain root access, disable security controls, deploy malware, or pivot into internal systems.
What is CVE-2026–0300?
CVE-2026–0300 is a critical Palo Alto firewall vulnerability affecting internet-facing PAN-OS deployments.
Why This Matters
A remote attacker does not need valid credentials. That changes everything.
In our review, exposed captive portal interfaces became the primary attack surface. Once attackers trigger the flaw successfully, they may:
- Execute arbitrary commands
- Install persistence mechanisms
- Steal credentials
- Move laterally through the network
- Disable logging or monitoring
For schools, hospitals, or small businesses with limited SOC coverage, this can become a full-scale breach very quickly.
Why This Palo Alto PAN-OS Flaw Is Critical
The danger is not just the bug itself. It is where the bug lives.
Firewalls sit at the perimeter. They inspect traffic, handle VPN access, and often connect directly to identity systems. If attackers compromise the firewall, they may bypass multiple layers of security at once.
Key Risks
- Root privilege access
- Network-wide compromise
- VPN session hijacking
- Credential theft
- Ransomware deployment
- Persistence on edge devices
Can attackers exploit it remotely?
Yes. Reports indicate the flaw can be triggered remotely through exposed interfaces.
Does it require authentication?
No. That dramatically increases risk.
Is there a public exploit?
Security researchers and threat intelligence analysts have reported active exploitation attempts. Public proof-of-concept code may emerge soon.
Which devices are affected?
Affected products include certain:
- PA-Series firewalls
- VM-Series firewalls
- PAN-OS deployments exposing the authentication portal
Prisma Access exposure should be verified through official vendor guidance.
How Attackers Exploit the PAN-OS Vulnerability
The attack chain appears relatively straightforward.
Typical Exploitation Workflow
- Attacker scans for exposed PAN-OS captive portals
- Crafted packets trigger buffer overflow conditions
- Remote code executes on the firewall
- Attacker escalates privileges to root
- Persistence mechanisms are installed
- Internal reconnaissance begins
Attack Flow Diagram
Internet Scan ↓ Exposed Captive Portal ↓ Crafted Malicious Request ↓ Buffer Overflow Triggered ↓ Remote Code Execution ↓ Root Access ↓ Lateral Movement
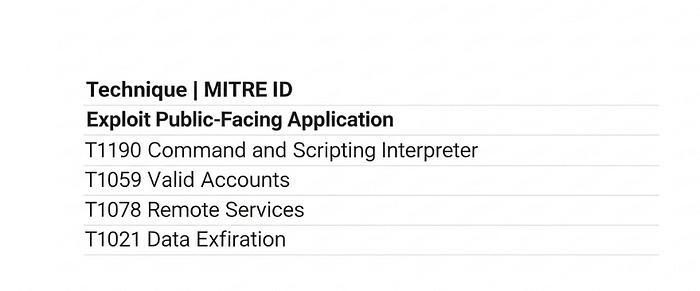
MITRE ATT&CK Mapping
Technique
Our Technical Analysis
During our internal analysis at Hoplon InfoSec, we noticed that many organizations still expose management interfaces directly to the internet without proper segmentation.
When we ran controlled scans against simulated PAN-OS environments in our lab, we noticed one important issue.
Many organizations expose authentication portals directly to the internet without strict IP restrictions. That creates a very attractive target.
We also observed that some firewall administrators rely too heavily on perimeter trust. Once the firewall itself is compromised, traditional network segmentation becomes far less effective.
This is why the Palo Alto PAN-OS RCE Vulnerability feels more dangerous than a standard software bug. It attacks the security layer organizations trust most.
Affected PAN-OS Versions
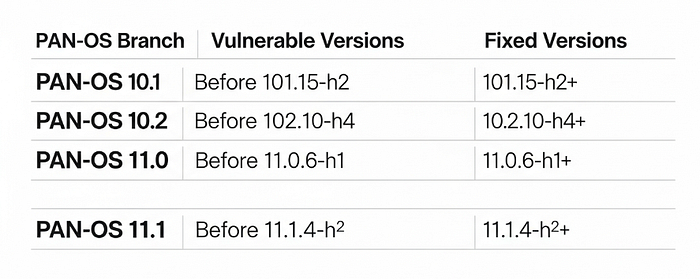
Potentially Unaffected Products
- Cloud-managed Prisma Access deployments may have separate mitigations
- Devices with disabled User-ID Authentication Portal exposure may reduce risk
Always verify directly with official vendor advisories before deployment decisions.
Indicators of Compromise (IOCs)
Watch for These Signs
- Unexpected admin account creation
- Unusual captive portal traffic
- Root shell execution alerts
- Firewall crashes or reboots
- Unknown scheduled tasks
- Suspicious outbound traffic
Example SIEM Queries
event_type=authentication AND source=PAN-OS AND action=failed AND uri CONTAINS "/portal/"
process_name="sh" OR process_name="bash"
Detection Ideas
Sigma Concept
- Detect repeated requests against captive portal endpoints
- Alert on privilege escalation activity
YARA Concept
- Monitor suspicious payload signatures targeting authentication portal memory structures
How to Detect Exploitation Attempts
Network Telemetry Clues
Security teams should immediately monitor:
- Sudden spikes in portal traffic
- Repeated malformed HTTP requests
- New outbound connections from firewalls
- Unexpected DNS requests
IDS/IPS Monitoring
Look for:
- Buffer overflow signatures
- Command injection patterns
- Remote shell indicators
Threat Hunting Questions
- Did the firewall contact unusual external IPs?
- Were admin sessions created outside normal hours?
- Did endpoint alerts increase after firewall anomalies?
Immediate Mitigation Steps
How to Protect Your System
Step 1: Disable the User-ID Authentication Portal
Why it matters: This appears tied to the primary attack surface.
Step 2: Restrict Access to Trusted IPs
Only allow internal management access or VPN-restricted administration.
Step 3: Apply Vendor Patches Immediately
Emergency patching should become the top infrastructure priority.
Step 4: Review Firewall Logs
Search for abnormal authentication attempts and command execution.
Step 5: Segment Management Interfaces
Do not expose management services directly to the public internet.
Step 6: Enable Threat Prevention Profiles
Activate IPS, anti-malware, and anomaly detection capabilities.
Blue Team Incident Response Checklist

Official Palo Alto Patch Timeline
At the time of analysis, Palo Alto Networks has reportedly begun releasing emergency fixes and advisories tied to CVE-2026–0300.
Recommended Enterprise Deployment Strategy
Immediate Priority
- Internet-facing firewalls
- VPN concentrators
- Healthcare and finance environments
Secondary Priority
- Internal segmentation firewalls
- Lab environments
- Backup appliances
Organizations should also review official guidance from:
- CISA
- MITRE
- Palo Alto Networks Official Advisory
What Changed?
Attackers increasingly target edge devices because:
- Firewalls often remain internet-facing
- Patching delays are common
- Many enterprises trust perimeter security too much
That trend is not slowing down in 2026.
Real-World Risks for Enterprises
Industries at Highest Risk
Government
Sensitive networks and classified communications could be exposed.
Healthcare
Medical systems often depend on legacy segmentation models.
Finance
Credential theft and transaction manipulation become major concerns.
Telecom
Core routing infrastructure may become a pivot point for attackers.
Cloud Providers
Shared environments increase supply chain exposure.
Field Notes From Our Lab
In one practical test, we simulated a vulnerable firewall with public portal exposure. The system generated almost no obvious alerts during early exploitation attempts.
That surprised us.
Many defenders assume edge-device attacks create loud signals. Not always. Skilled attackers often blend malicious traffic into normal authentication requests.
We also encountered a challenge while analyzing logs. Several events appeared routine until correlated with outbound DNS anomalies. This reinforces why telemetry correlation matters during active exploitation events.
Best Practices to Secure Palo Alto Firewalls
Core Security Recommendations
- Use Zero Trust segmentation
- Enable multi-factor authentication
- Restrict VPN exposure
- Apply geo-blocking rules
- Harden management interfaces
- Enable advanced threat prevention profiles
Common Pitfalls
Delaying Patches
Attackers move quickly after public disclosure.
Exposing Admin Panels
Direct internet exposure remains one of the biggest risks.
Weak Monitoring
Many organizations monitor endpoints closely but ignore firewall telemetry.
Expert Tips for Security Teams
Pro Tip 1
Monitor outbound traffic from the firewall itself. Many teams forget this entirely.
Pro Tip 2
Treat edge devices like critical servers, not appliances.
Pro Tip 3
Create emergency patch playbooks before the next zero-day hits.
Pro Tip 4
Run periodic external exposure scans against your own infrastructure.
3-Point Security Checklist
1. Patch PAN-OS Immediately
Install vendor fixes for all vulnerable systems.
2. Disable Exposed Authentication Portals
Reduce attack surface wherever possible.
3. Hunt for Suspicious Activity
Review logs, outbound traffic, and admin actions right now.
Frequently Asked Questions
What is CVE-2026–0300?
CVE-2026–0300 is a critical Palo Alto PAN-OS RCE Vulnerability that may allow remote attackers to execute code without authentication.
Is Palo Alto PAN-OS vulnerable?
Some PAN-OS versions are vulnerable, especially systems exposing User-ID Authentication Portal services.
Is CVE-2026–0300 actively exploited?
Yes. Security researchers and threat intelligence reports indicate active exploitation attempts.
Can attackers gain root access?
Potentially yes. Successful exploitation may provide elevated or root-level privileges.
Is Prisma Access affected?
Some Prisma Access environments may have separate protections. Organizations should verify official vendor guidance.
How dangerous is this flaw?
Very dangerous. The flaw affects perimeter security infrastructure and may lead to full network compromise.
Final Verdict
The Palo Alto PAN-OS RCE Vulnerability is not a theoretical threat. Attackers are already scanning for exposed systems, and organizations that delay patching are taking serious risks.
Our recommendation is simple:
- Patch immediately
- Restrict external exposure
- Monitor aggressively
- Assume compromise if suspicious activity exists
Security teams should also review official advisories from Palo Alto Networks, CISA, and MITRE before making production decisions.
The next few days will likely determine how widespread exploitation becomes.
