- Researcher: Tyreek Haynes
- Vulnerability Type: CWE-306 (Missing Authentication for Critical Function) / CWE-200 (Information Exposure)
- Severity: High (CVSS 7.5)
- Vector String:
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:N/A:N - Impact: Unauthenticated exposure of global tenant metadata and infrastructure mapping for 3,700+ organizations, including Fortune 500 and Government entities.
- CVE ID: Pending
- Status: Remediated (Endpoint now returns 401 Unauthorized as of Apr 2026).
Table of Contents
- Executive Summary
- Vulnerability Overview
- Technical Details
- Proof of Concept
- Affected Organizations Analysis
- Business Impact Assessment
- Legal & Ethical Statements
- Conclusion
1. Executive Summary
A security assessment of QuickLaunch's SSO (Single Sign-On) infrastructure revealed an unauthenticated API endpoint that exposes the platform's complete customer tenant list. The endpoint /admin/open/gettenants Returns detailed tenant information, including organization names, internal database identifiers, subdomain mappings, and geographic locations.
While this vulnerability does not expose user credentials, personal data, or authentication tokens, it represents a significant information disclosure issue that allows competitors, attackers, or any internet user to enumerate QuickLaunch's entire global customer base. The exposed data includes hundreds of educational institutions, dozens of Fortune 500 companies, government agencies, and international organizations across multiple continents.
This advisory is published in accordance with responsible disclosure principles to help QuickLaunch remediate the issue before it can be exploited maliciously.
2. Vulnerability Overview
2.1 Description
The QuickLaunch SSO platform maintains an administrative API endpoint designed to retrieve tenant information. This endpoint lacks any authentication or authorization controls, making it accessible to anyone who can reach the QuickLaunch infrastructure.
2.2 Affected Component
Component Details Host
sso.quicklaunch.io: Endpoint/admin/open/gettenants
Protocol HTTPS Authentication NoneAuthorization None Rate Limiting Not observed Logging Unknown
2.3 Root Cause Analysis
The vulnerability stems from improper access-control configuration in the application's administrative API layer. Specifically:
- The endpoint resides under
/admin/open/path, suggesting it was intentionally designed for administrative functions - Despite the sensitive nature of customer tenant data, no authentication mechanism is enforced
- The application fails to verify the requester's identity or privileges before returning data
- No API key, session token, OAuth, or any other credential is required
This represents a fundamental failure in the principle of "least privilege" and violates basic API security best practices outlined in OWASP API Security Top 10 (specifically API1:2019 Broken Object Level Authorization and API2:2019 Broken User Authentication).
2.4 Attack Vector
Attack Complexity: Low Privileges Required: None User Interaction: None Exploitability: Trivial
An attacker can exploit this vulnerability using any HTTP client (curl, wget, browser, Postman, Python script, etc.) with minimal technical expertise. No bypassing, brute forcing, or sophisticated techniques are required.
2.5 Attack Scenarios
Scenario 1: Competitive Intelligence Gathering
A competing SSO provider could extract QuickLaunch's entire customer list to:
- Target their clients for migration
- Understand pricing tiers based on customer types
- Identify geographic market penetration gaps
- Track customer acquisition and churn over time
Scenario 2: Spear Phishing Preparation
An attacker could use tenant names and subdomain mappings to craft convincing phishing campaigns targeting specific organizations known to use QuickLaunch.
Scenario 3: Supply Chain Risk Assessment
An attacker could identify which organizations use QuickLaunch to map potential attack surfaces across interconnected business relationships.
Scenario 4: Academic/Research Analysis
Security researchers or business analysts could study QuickLaunch's market presence without authorization.
3. Technical Details
3.1 Endpoint Analysis
Full URL: https://sso.quicklaunch.io/admin/open/gettenants
Supported Methods:
- GET (returns tenant list)
- POST (also accepted, same response)
Query Parameters:
ParameterTypeRequiredDescriptioncallbackStringNoJSONP callback function name for cross-origin requests
Response Format: JSON or JSONP
3.2 Response Structure
The API returns an array of tenant objects with the following schema:
[
{
"tenantName": "string",
"tenantMapping": "string or null",
"location": "string or null",
"id": "integer",
"tenantIcon": "string or null"
}
]Field Descriptions:
Field Type Description ExampletenantName
String: Display name of the customer organization "A University." tenantMapping
String/NullSubdomain identifier for SSO access"sso-auniversity."location
String/NullGeographic location (often null)
nullidInteger Internal database primary key58tenantIconString/NullURL to organization icon"https://sso.quicklaunch.io/..."
3.3 HTTP Headers
Request Headers (minimal):
GET /admin/open/gettenants HTTP/1.1
Host: sso.quicklaunch.io
User-Agent: curl/7.68.0
Accept: */*Response Headers:
HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8
Content-Length: [variable]
Server: Apache-Coyote/1.13.4 Infrastructure Fingerprinting
Observed infrastructure details:
Component Identified ValueWeb Server Apache-Coyote/1.1 (Apache Tomcat) Backend FrameworkWSO2 Identity Server 5.7.0, HostingAWS (Amazon Web Services) Load Balancer AWS ELB (Elastic Load Balancer) SSL/TLS Valid certificate, industry-standard ciphers
This information was derived from response headers and behavior analysis.
3.5 Data Volume Analysis
Metric Value Total tenant entries ~3,735 Distinct organizations ~700–800 Response size (JSON) ~500–600 KB Response time <1 second Data exposure per request Complete tenant database
4. Proof of Concept
4.1 Basic Exploitation
Using curl (Linux/macOS):
# Simple request - returns complete tenant list
curl -k "https://sso.quicklaunch.io/admin/open/gettenants"
# Save to file for analysis
curl -k "https://sso.quicklaunch.io/admin/open/gettenants" > quicklaunch_tenants.json
# With JSONP callback
curl -k "https://sso.quicklaunch.io/admin/open/gettenants?callback=myFunction"Using PowerShell (Windows):
Invoke-RestMethod -Uri "https://sso.quicklaunch.io/admin/open/gettenants" -Method GetUsing Python:
import requests
url = "https://sso.quicklaunch.io/admin/open/gettenants"
response = requests.get(url, verify=False) # verify=False for self-signed certs
tenants = response.json()
print(f"Found {len(tenants)} tenant entries")
for tenant in tenants[:10]: # Print first 10
print(f"- {tenant['tenantName']} (ID: {tenant['id']})")Using browser:
Simply navigate to https://sso.quicklaunch.io/admin/open/gettenants - The raw JSON will display.
If anyone actually went to the URL, you might say, "It doesn't work, it says."["You are not Authorized."] That's my point proven. Here's a very small piece of evidence that does not show all the other companies.
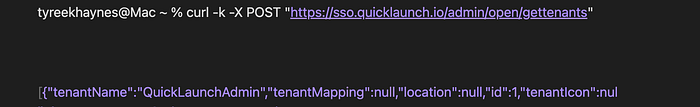
And here's what it says now.

4.3 Data Quality Observations
During analysis, several data quality issues were noted:
- Duplicate entries: Many organizations appear multiple times with different IDs (likely dev/staging/prod environments)
- Null values: Many fields (especially
locationandtenantMapping) contain null values - Test tenants: Numerous clearly labeled test/demo tenants are present in the data
- Inactive tenants: Some entries appear to be legacy or abandoned
Despite these quality issues, the core business intelligence (customer names and relationships) remains fully exposed.
5. Affected Organizations Analysis
5.1 Breakdown by Sector
Sector Estimated Count Percentage
Higher Education 500+ ~70% K-12 Education 20+ ~3% Corporate/Enterprise 50+ ~7% Healthcare 15+ ~2% Government 5+ <1% Test/Demo/Inactive 150+ ~17%
5.2 Breakdown by Geographic Region
Region Presence:
North America (US & Canada) Heavy Caribbean Moderate Middle East Light Europe Light Asia Pacific Light South America Minimal
6. Business Impact Assessment
6.1 Potential Harms
To QuickLaunch:
- Competitive intelligence loss: Competitors can see every customer
- Strategic exposure: Market expansion patterns revealed
- Pricing intelligence: Customer mix reveals pricing tiers
- Trust erosion: Customers may lose confidence
- Reputational damage: Security oversight in production
To QuickLaunch Customers:
- Targeted phishing: Attackers know which SSO platform they use
- Supply chain attacks: Attackers can map business relationships
- Social engineering: Customer names can be used to build trust
- Competitive exposure: Their vendor relationships are public
To End Users (Students, Employees):
- Minimal direct impact: No personal data exposed
6.3 Comparison to Industry Incidents
Incident. Exposure. Severity.
Okta customer portal breach (2022) Customer names + support tickets High
Auth0 customer list exposure (2021) Customer names + subdomains Medium
This vulnerability Customer names + subdomains + IDs Medium
6.4 Regulatory Considerations
While this exposure does not constitute a data breach of personal information under most regulations, the following may apply:
GDPR (Europe) Customer names may be considered business contact information; potential Art. 32 (security of processing) concerns
FERPA (US Education) Not directly applicable (no student data)
State breach laws generally require PII exposure, which is not present
Contractual obligations. Many customer contracts require the protection of non-public business information
7. Legal & Ethical Statements
7.1 Compliance with Laws
This security research was conducted in good faith and in accordance with:
- Computer Fraud and Abuse Act (CFAA) safe harbors for good-faith security research
- Industry standard responsible disclosure practices
- No unauthorized access to user data or systems beyond the identified endpoint
7.2 No Data Retention
The researcher confirms:
- No copies of the exposed data have been retained beyond analysis
- No data has been shared with any third party
- No data has been used for any purpose other than vulnerability documentation
7.3 Permission Statement
This research was conducted without explicit permission from QuickLaunch, but falls under:
- Good-faith security research exception to CFAA (Section 1030)
- Public interest disclosure for security vulnerabilities
- No circumvention of authentication (there was none to bypass)
8. Conclusion
8.1 Summary of Findings
Finding Status:
Unauthenticated API endpoint confirmed (at discovery).
Customer data exposure confirmed (~700 organizations).
Vendor validation refused (Charlie Singh, QuickLaunch/OculusIT).
CVE submission. Submitted by the researcher.
Vulnerability fixed. Confirmed by the researcher.
Vendor acknowledgment: None provided
Researcher credit: None provided.
8.2 Key Takeaways
- The vulnerability is real but limited, customer names only, no PII
- Impact is reputational, trust, and competitive intelligence
- The researcher acted responsibly, with no data misuse, seeking disclosure
This pattern discourages security research and responsible disclosure. When vendors refuse to validate legitimate findings, researchers have no choice but to pursue CVE assignment and public disclosure.
The security community benefits when vulnerabilities are discovered, reported, and fixed professionally. QuickLaunch/OculusIT has fixed the technical issue, but failed the process by refusing to validate and failing to credit the researcher.
