Day 14 of breaking web applications on purpose.
And since today is Holi, let's talk about a vulnerability that spreads access everywhere…
Just like colors.
But instead of colors…
It spreads data leaks.
Welcome to IDOR — Insecure Direct Object Reference.
One of the most common vulnerabilities in real-world bug bounties.
And the scary part?
It doesn't require hacking skills.
Sometimes all it requires is curiosity.
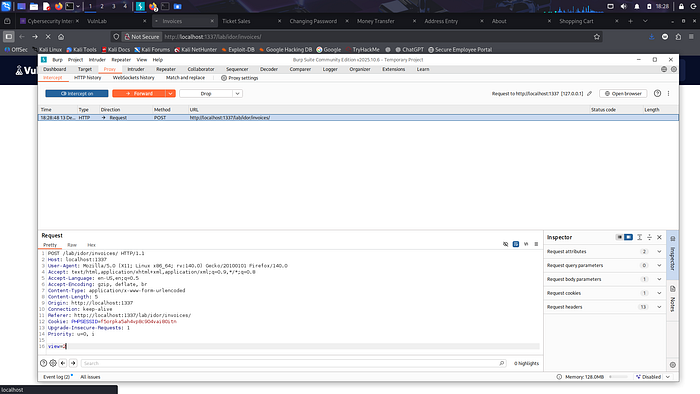
🎯 The Setup
The application allows users to view their profile.
When a user opens their profile, the URL looks like this:
/profile?id=101
Looks normal.
Behind the scenes, the server likely runs a query like:
SELECT * FROM users WHERE id = 101;
And it returns the user's data.
But here's the real question every hacker should ask:
👉 What happens if we change the ID?
🧠 The First Test
Instead of visiting:
/profile?id=101
We try:
/profile?id=102
And then refresh the page.
Suddenly…
You're looking at someone else's profile.
Different user.
Different personal data.
No authentication bypass.
No injection payload.
Just a number.
💣 The Vulnerability
The application verifies that the user is logged in.
But it never verifies that the user is allowed to access that specific profile.
This is the difference between:
Authentication vs Authorization.
Authentication asks:
"Are you logged in?"
Authorization asks:
"Are you allowed to see this?"
This application only asked the first question.
⚡ Why This Works
The backend probably uses something like:
$id = $_GET['id']; $query = "SELECT * FROM users WHERE id=$id";
Notice the problem?
The application trusts the ID sent by the user.
There's no check that confirms the ID actually belongs to the logged-in user.
So the server simply returns whatever record matches the ID.
If attackers iterate:
?id=101 ?id=102 ?id=103 ?id=104
They could potentially enumerate every user in the system.
🧠 Real-World Analogy
Imagine a Holi party where everyone gets access to the color storage room.
But instead of checking whose color bag belongs to whom…
Anyone can open any bag.
One small mistake.
Suddenly everyone's colors are mixed.
That's IDOR.
The system forgets to verify ownership.
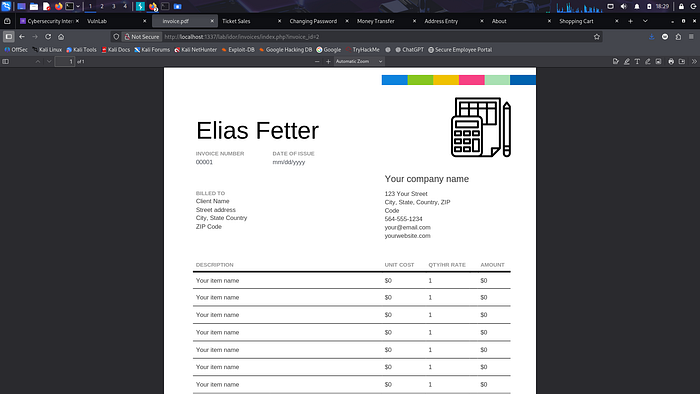
💥 Real-World Impact
In real applications, IDOR can expose:
• Personal user information • Financial records • Private documents • Medical data • Internal company resources
Sometimes attackers can even:
• Change passwords • Delete accounts • Download invoices • Access admin data
All by changing a single parameter.
🛡️ Proper Fix
Never trust object IDs coming from the client.
The server must always verify ownership.
A secure query would look like:
SELECT * FROM users WHERE id = ? AND user_id = CURRENT_USER;
Additional protections include:
• Role-based access control • Using UUIDs instead of sequential IDs • Server-side ownership validation • Monitoring abnormal access patterns
Security rule:
Every object request must verify ownership.
Always.
🎯 Day 14 Takeaway
You didn't inject SQL.
You didn't write JavaScript.
You didn't break authentication.
You simply changed a number.
And the application revealed someone else's data.
Sometimes hacking isn't about exploiting complex bugs.
It's about noticing what the system forgot to check.
Tomorrow we escalate this further.
From reading other users' data…
To modifying their accounts.
And that's where authorization bugs become truly dangerous.
LESSGOOO 🔥
Stay curious. Small inputs reveal big flaws.