In Part 1 of this cybersecurity roadmap series, we discussed the foundational prerequisites and entry-level courses required to enter the field of cybersecurity and penetration testing in 2026 — based on both my personal experience and consultations with professionals active in the industry.
Before continuing, I want to sincerely apologize for the delay in publishing this second part. Unfortunately, due to a nationwide internet shutdown in Iran that lasted approximately 20 days, access was unavailable — which significantly delayed this article.
In this part, we will dive deeper into the structured learning path for:
- Web Penetration Testing - Mobile Penetration Testing (to be covered in Part 3) - Practical labs - Essential learning platforms - Real-world vulnerability reporting platforms

Web Penetration Testing Courses (OWASP Top 10)
Almost every country offers courses centered around the OWASP Top 10, whether in-person, online, or bootcamp-style.
The official list is published by OWASP, and you can always check the latest version on the official website of the OWASP Foundation.
Why Is OWASP Top 10 an Excellent Starting Point?
Because it introduces you to the most critical and frequently exploited web vulnerabilities observed in real-world environments.
A Quick Overview of Key Vulnerabilities:
Broken Access Control — Unauthorized access to restricted resources Security Misconfiguration — Improper or insecure configurations Software Supply Chain Failures— Vulnerabilities in third-party libraries and dependencies Cryptographic Failures — Weak or improper cryptographic implementations Injection — SQL Injection, Command Injection, and similar attacks Insecure Design— Architectural design flaws Authentication Failures — Weak authentication and session management Software or Data Integrity Failures** — Integrity violations in code or data Security Logging & Monitoring Failures — Lack of proper logging and alerting Improper Error Handling — Unsafe handling of exceptions and system errors
Once you gain solid understanding of these concepts, the real journey begins: structured, hands-on practice.
The Most Critical Stage: Deliberate Practice
PortSwigger Academy
One of the best platforms globally for practical web penetration testing is:
This company is also the creator of the industry-standard web testing tool:

Why Is PortSwigger So Important?
High-quality, categorized vulnerability articles Structured labs (Beginner → Practitioner → Expert) Realistic attack scenarios based on real-world cases Practical exposure to Burp Suite features
Golden Rule: Always attempt to solve labs on your own before reviewing the solution.
Even More Important: Take structured notes after completing each lab. This habit differentiates professionals from beginners.
For many successful penetration testers and bug hunters, consistent and targeted lab-solving on PortSwigger has been a major turning point in their careers.
Additional Essential Practice Labs
An intentionally vulnerable modern e-commerce application containing more than 170 challenges, covering:
OWASP Top 10 OWASP API Top 10 Business Logic vulnerabilities
You can run it:
Online Locally using Docker On your own VPS
Major advantage: Beyond vulnerability testing, you'll gain hands-on exposure to Docker, web servers, reverse proxies, and DevOps-related configurations.
DVWA (Damn Vulnerable Web Application)
Damn Vulnerable Web Application
A classic vulnerable web application designed specifically for security training.
It covers most OWASP Top 10 vulnerabilities and provides three difficulty levels:
Easy Medium Hard
It can be deployed via:
Online Website — username: admin pass: password
VPS Docker
Additionally, in some practical modules of the EC-Council certification — specifically the Certified Ethical Hacker — DVWA-style environments are often used for web-related exercises.
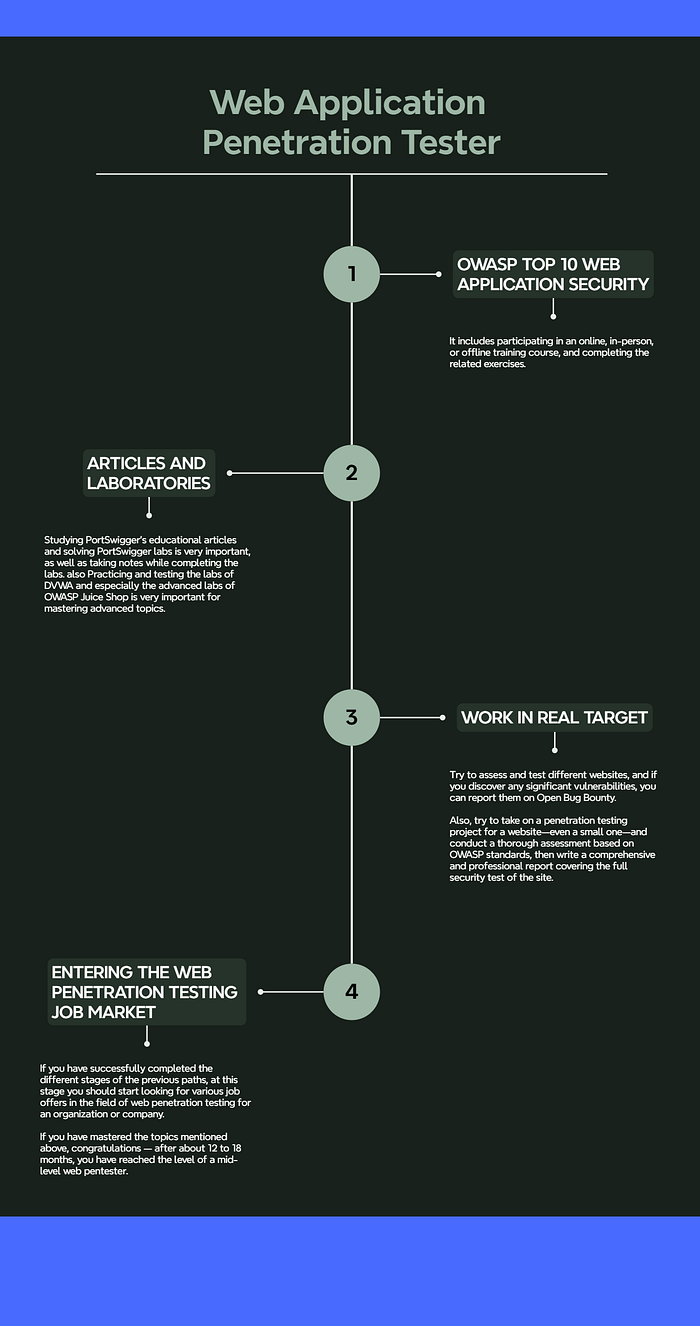
Entering the Real World (After 12–18 Months)
After approximately one year of serious, consistent practice (including foundational courses and advanced web penetration testing topics), you should begin testing your skills in real-world environments.
🟢 OpenBugBounty
OpenBugBounty
A global vulnerability disclosure platform (VDP) that does not offer monetary rewards.

Why It's Valuable:
Builds a strong public portfolio Familiarizes you with vulnerability triage processes Teaches you how patch validation works Strengthens vulnerability validation and reporting skills
Although there are no cash rewards, the experience and public track record are extremely valuable for your resume.
Advanced Competitive Platforms (Later Stage)
HackerOne Bugcrowd
These platforms host Bug Bounty Programs (BBP) that offer financial rewards.
⚠️ However, an important recommendation:
Due to intense competition, beginners may become discouraged if they fail to find valid vulnerabilities. For this reason, I strongly recommend avoiding these platforms during your first two years. Focus instead on structured labs, OpenBugBounty, and real client projects before entering high-competition bounty environments.
Progressing to Professional Levels
Mid-Level Web Pentester
If you consistently follow this roadmap with discipline and serious effort:
Within 12–18 months, you can realistically reach a mid-level web penetration testing skill set and confidently apply for relevant job positions.
Senior Web Pentester
To reach senior level, you will need:
1–2 years of real-world professional experience Knowledge beyond OWASP Top 10
An important advanced reference is:
OWASP Web Security Testing Guide
Additionally, gaining expertise in enterprise technologies is highly valuable. For example:
Active Directory
Learning both attack and defense techniques in enterprise environments can significantly strengthen your profile for senior or Red Team positions.
✅ Final Roadmap Summary
In Part 3 of this series, we will explore the Mobile Penetration Testing Roadmap, which can be pursued alongside web penetration testing for faster career growth.
