اللهم اعز الاسلام والمسلمين
🔻اللهم انصر اخوننا المستضعفين في كل مكان

Hi, I'm Kareem, a Security Researcher.
Introduction
During testing, I discovered a vulnerability that allows Stored Cross-Site Scripting (XSS) through an image upload functionality.
This issue is caused by improper file validation combined with MIME-type confusion.
Reproduction Steps
- Upload a profile picture using the image upload feature.
- The application accepts files with a
.gifextension. - Intercept the upload request and modify the header:
4.Change Content-Type from image/jpeg to text/html
5. Embed a JavaScript payload inside the file content (not simply appended).
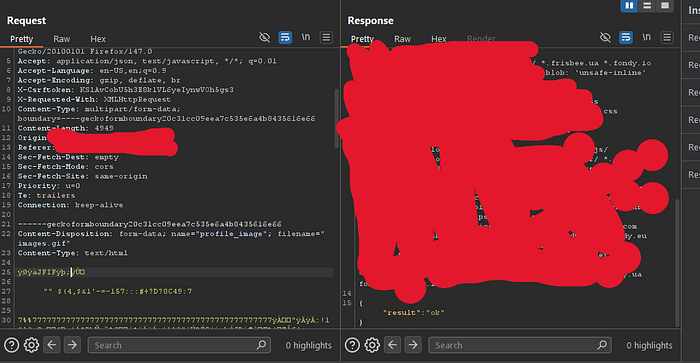
Example payload:
<img src="x" onerror="alert('hack')">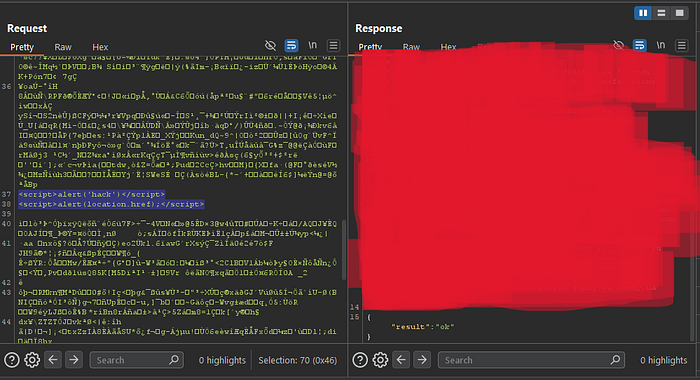
- Complete the upload process.
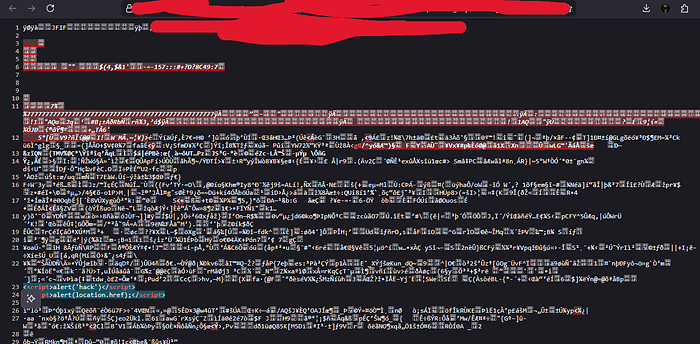
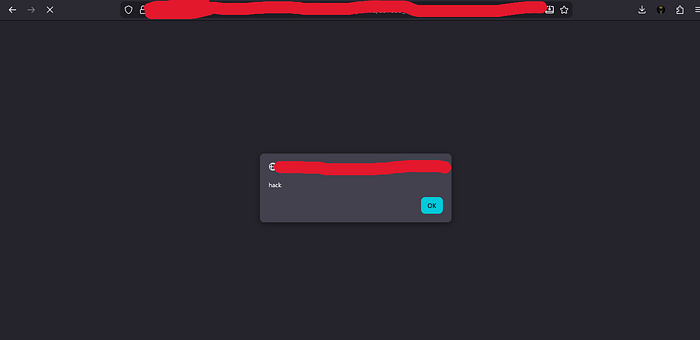
- Open the uploaded file via its public URL.
Result
- The browser interprets the file as HTML instead of an image.
- The injected JavaScript executes successfully.
Impact
This vulnerability may allow:
- Stored XSS attacks
- Session hijacking (depending on protections)
- Malicious redirection
- Data exfiltration
Root Cause
- Lack of proper file content validation
- Trusting file extensions instead of actual content
- Allowing user-controlled MIME types
- Rendering uploaded files directly in the browser