Day 14 : Cybersecurity Mastery series
Welcome to Day 14 of our 30-Day Cybersecurity Mastery series. We are continuing our deep dive into Phase 3: Offensive Security & Vulnerability Exploitation.
Yesterday, we explored how attackers exploit human psychology through Social Engineering to bypass cryptographic defenses. But what happens when the workforce is highly trained, and no one clicks the phishing link? The attacker must return to the technical battlefield.
If they cannot trick the user into handing over the password, they will attempt to silently pluck that password out of the air as it travels from the user's laptop to the corporate server. Today, we dissect the mechanics of network interception: Packet Sniffing, Wireshark, and Man-in-the-Middle (MitM) Attacks.
1. The Mechanics of Eavesdropping: Promiscuous Mode
To understand how an attacker intercepts traffic, you must first understand how a Network Interface Card (NIC) normally operates.
By default, the network card in your laptop is polite. It ignores the billions of data packets flying across the corporate Wi-Fi network, only capturing and reading the packets that are specifically addressed to its unique MAC (Media Access Control) address.
Packet Sniffing changes this fundamental behavior.
- The Exploit: An attacker configures their NIC to enter Promiscuous Mode (or Monitor Mode on wireless networks). In this state, the network card stops being polite. It captures, copies, and reads every single packet traversing the local network segment, regardless of who it is addressed to.
2. The Tool of the Trade: Wireshark and Protocol Analysis
Packet sniffing is not inherently illegal; it is a vital diagnostic capability. When a network engineer needs to figure out why a database connection is failing, they use a protocol analyzer to capture the traffic.
The undisputed industry standard for this is Wireshark.
- What it does: Wireshark captures raw network traffic and decodes it, translating binary data into human-readable formats organized by the OSI Model (Day 3). It saves these captures as
.pcap(Packet Capture) files. - The Attacker's Objective: A malicious actor uses Wireshark to filter the massive stream of corporate data, searching specifically for unencrypted protocols. If an administrator logs into an old legacy switch using Telnet (Port 23) or HTTP (Port 80), Wireshark will display their username and password in absolute, crystal-clear plaintext.
3. The Active Interception: Man-in-the-Middle (MitM)
Passive sniffing only works if the attacker happens to be on the exact same network segment as the target. To actively force traffic to flow through their machine, the attacker executes a Man-in-the-Middle (MitM) attack.
A MitM attack is the digital equivalent of intercepting the mail carrier, opening a letter, reading the contents, resealing it, and sending it to the final destination without the sender or receiver ever knowing.
In enterprise environments, the most common technical method for achieving this is ARP Spoofing (or ARP Poisoning) at Layer 2 of the OSI model.
The ARP Spoofing Kill Chain:
- The Normal State: The Address Resolution Protocol (ARP) maps logical IP addresses to physical MAC addresses. When a CEO's laptop wants to send an email, it asks the network, "Who has the IP address of the Router (192.168.1.1)?" The Router replies, "I do, here is my MAC address."
- The Poisoning: ARP is a legacy protocol with zero built-in authentication. The attacker's machine blasts the network with forged (spoofed) ARP replies. It continuously tells the CEO's laptop, "I am the Router," and simultaneously tells the Router, "I am the CEO's laptop."
- The Interception: The CEO's laptop updates its internal ARP cache with the attacker's fake information. Now, when the CEO sends a secure document, it goes directly to the attacker's machine first. The attacker's Wireshark captures the data, and then the attacker silently forwards the document to the real Router so the CEO never realizes there was a delay.
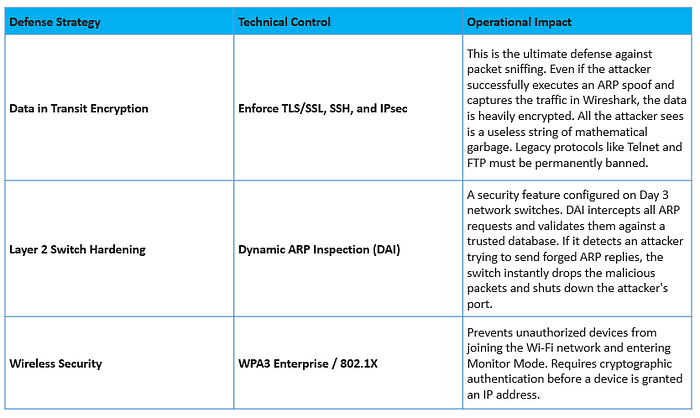
4. Architecting the Defense: Encryption and Switch Configuration
Defending against network interception requires a two-pronged architectural approach: rendering the data useless, and blocking the spoofing mechanics.
The Architect's Summary
The network wire is an inherently hostile environment. As an enterprise architect, you must operate under the assumption that an attacker is already listening to your traffic. By understanding how packet sniffing and ARP spoofing manipulate the foundational protocols of the internet, you realize that network segmentation (VLANs) and mandatory end-to-end encryption are not just compliance checkboxes — they are the only mathematical guarantees of confidentiality in transit.
Looking Ahead
Today, we learned how attackers intercept data moving across the network. But what happens if the target isn't a human or a network router, but rather the very application the business is built on?
Tomorrow, in Day 15, we will explore the devastating world of Web Application Attacks, diving into SQL Injection (SQLi) and Cross-Site Scripting (XSS).

