Context
During a recent technical discussion within the CyberSphere Community, we explored one of the most overlooked attack surfaces in modern applications: password reset functionality.
The focus was not login.
It was recovery.
Not because authentication systems are always weak.
But because recovery mechanisms are often trusted more than they should be.
The session was designed for beginners and cybersecurity learners who want to understand how attackers abuse weak password reset flows to take over accounts without knowing the original password.
Session Objective
The discussion focused on:
Understanding how password reset systems work Breaking down common reset flow vulnerabilities Explaining how attackers abuse weak recovery mechanisms Understanding how defenders can secure account recovery processes
What Password Reset Flaws Really Mean
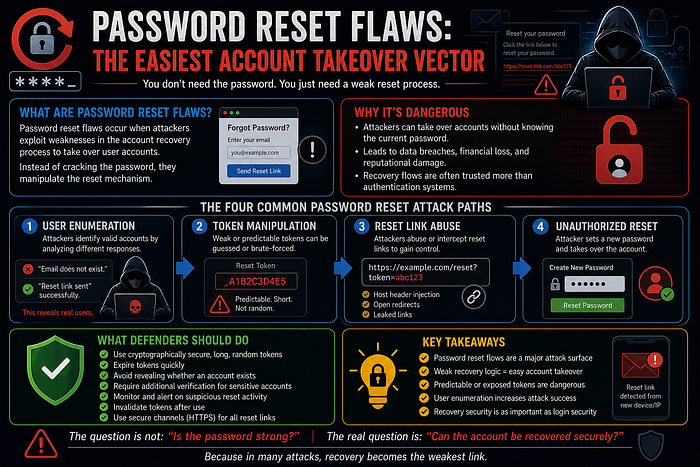
Password reset flaws occur when attackers manipulate the account recovery process to gain unauthorized access.
Instead of attacking the password directly:
They target the reset mechanism.
Modern applications often prioritize convenience during recovery.
That convenience creates risk.
Why Password Reset Systems Become Targets
Password reset flows are trusted because they are designed to help legitimate users regain access.
But attackers abuse weaknesses such as:
Predictable reset tokens Weak verification mechanisms Improper token expiration User enumeration Insecure reset links
The login system may be secure.
The recovery flow may not be.
The Four Common Password Reset Attack Paths
1. User Enumeration
Attackers first identify valid accounts.
This often happens when applications reveal different responses like:
"Email does not exist" "Reset link sent successfully"
This allows attackers to identify real users.
2. Token Manipulation
The attacker targets the reset token itself.
Weak implementations may use:
Predictable tokens Short numeric codes Improper randomness
If the token can be guessed, the account can be reset.
3. Reset Link Abuse
Attackers manipulate reset URLs.
This may include:
Host header injection Open redirects Leaked reset links
If the reset link is intercepted or redirected, account takeover becomes possible.
4. Unauthorized Password Reset
Once the attacker controls the reset process:
They create a new password.
The legitimate user is locked out.
The attacker now owns the account.
Why Password Reset Flaws Still Exist in 2025
Despite stronger authentication systems, reset vulnerabilities remain common because:
Recovery flows receive less security testing Developers prioritize usability over security Reset mechanisms are implemented inconsistently Monitoring focuses mainly on login activity Legacy systems use outdated recovery logic
The issue is not authentication.
It is weak recovery design.
What Defenders Should Actually Focus On
To secure password reset systems, organizations should:
Use cryptographically secure reset tokens Expire tokens quickly Avoid revealing valid accounts Require additional verification for sensitive accounts Monitor abnormal reset activity Invalidate reset tokens after use Use secure communication channels only
Recovery systems must be treated as authentication systems.
The Beginner Mindset Shift
If you are learning cybersecurity, understand this:
Attackers do not always attack the front door.
Sometimes, they target the recovery process beside it.
Strong passwords mean nothing if recovery is weak.
Key Takeaways
Password reset flows are major attack surfaces Weak recovery logic enables account takeover Predictable or exposed reset tokens are dangerous User enumeration increases attack success Recovery security is as important as login security
Attackers often target what defenders overlook.
Closing Thought
The question is not:
"Is the password strong?"
The real question is:
"Can the account be recovered securely?"
Because in many attacks, recovery becomes the weakest link.
Acknowledgement
Thanks to Harsh Kanojia, Founder of the CyberSphere Community, for encouraging discussions focused on practical application security and real-world attack understanding.
Author
Naman Shah Cybersecurity postgraduate focusing on secure systems, threat modeling, and applied security education.