The scariest vulnerabilities in software are not the dramatic ones. They are the ones hiding inside features that appear to be working perfectly. Imagine you walk into a hospital, collect your patient file from the front desk, and notice your file is labeled number 1043. Out of curiosity, you ask for file 1042. The receptionist hands it to you without checking whether you have any right to it. No questions asked. That is exactly what Insecure Direct Object Reference (IDOR) is, and it happens in software every single day.
Insecure Direct Object Reference means your application exposes internal identifiers, transaction IDs, user IDs, account numbers, document references, and does not verify whether the person requesting them actually owns or has rights to them. The door is open. Anyone who knows the number gets in.
This is not limited to fintech. It shows up in healthcare platforms handing out other patients' records, HR systems exposing other employees' payslips, e-commerce apps revealing other customers' order histories, and legal platforms leaking confidential case files. Any application that stores data per user and retrieves it by a predictable reference is a candidate.
In fintech specifically, the stakes are higher because the data is financial. A payment app exposing /api/transactions/8842 without confirming the requesting user owns that transaction is vulnerable. A digital wallet returning account balances based on a user ID passed in the request body, without cross-checking the authenticated session, is vulnerable. Loan platforms, investment dashboards, and insurance apps built on sequential record IDs with no ownership validation all carry the same silent flaw.
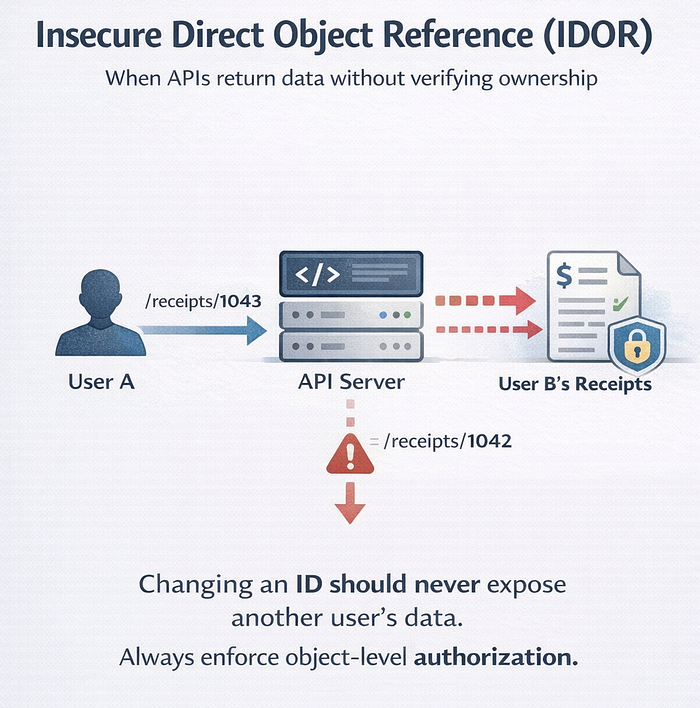
Technically, the failure is this: the server trusts the client to declare what resource it wants, then fetches it without asking whether the authenticated user has the right to that specific object. Sequential integers make guessing trivial. Even switching to UUIDs does not solve it if the authorization logic is missing entirely.
A realistic attack looks like this: someone signs up, completes a transaction, and notices their receipt URL ends in /receipts/1043. They changed it to 1042. The server returns a stranger's receipt: full name, transaction amount, and account details. They write a simple script. Within an hour, they have pulled thousands of records. No alarm fired. The logs show nothing unusual, just authenticated requests coming in.
The fix is not complicated, but it requires discipline at every endpoint, not just at login or the route level. 1. Enforce object-level authorization server-side on every single request. 2. Confirm that the authenticated session maps to the requested resource before returning any data. 3. Where possible, use indirect references; session-scoped tokens instead of raw database keys exposed to the client. 4. Log per-user access patterns so abnormal behavior surfaces before it becomes a breach.
IDOR holds the number one spot on the OWASP API Security Top 10 for a reason. It is not a tooling problem. It is an engineering habit problem. Authorization is not a layer you add after the product ships. It is a promise you make to every person who trusts your platform with their data.
#CyberSecurity #FintechSecurity #IDOR #APISecurity #BrokenAccessControl #WebSecurity #ApplicationSecurity #SecureByDesign #OWASP #Fintech #SoftwareEngineering #DevSecOps #SecurityEngineering #30DaysOfSecurity #CTOInsights