FOOTPRINTING AND RECONNAISSANCE
RECONNAISSANCE
Footprinting is a part of a larger process known as reconnaissance. Reconnaissance is the information-gathering stage of ethical hacking, where you collect data about the target system. This data can include anything from network infrastructure to employee contact details.
FOOTPRINTING
Footprinting in ethical hacking is a common technique used by security professionals to assess an organisation's security posture. It can be used as part of a more extensive assessment or in isolation and can provide valuable information about the organisation's cybersecurity vulnerabilities.
Types of Footprinting
- Active footprinting: Interact directly with the machines on the target network in order to collect the data that may not be available by other means. Ex: Ping, Tracert
- Passive footprinting: Never interacts directly with the target network. Take advantage of unmentioned or unintentional data leaks from an organisation to provide the hacker with insight into the internals of the organisation's network. Ex: Whois tool
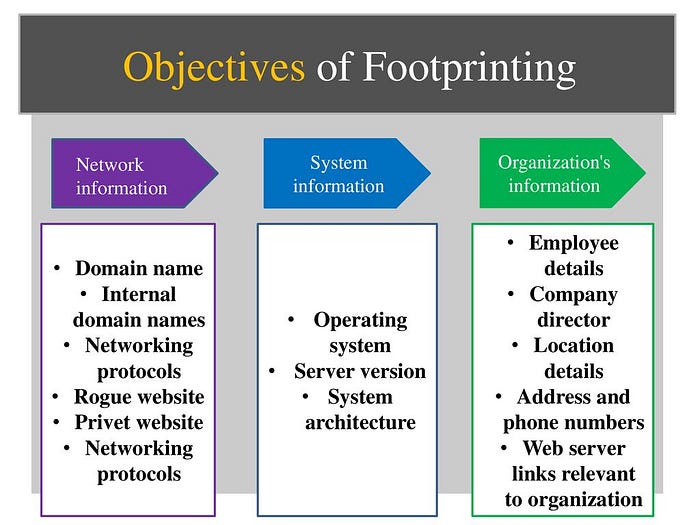
Information obtained in Footprinting
1. Organisation Information.
2. Network Information.
3. System Information.
Footprinting Methodology
● Footprinting through search engines
● Footprinting through web services
● Footprinting through social networking sites
● Website Footprinting
● Network Footprinting
● DNS Footprinting
● Whois Footprinting
● Email Footprinting
● Footprinting through social engineering
Footprinting through search engines
Attackers often use search engines to gather useful information about a target. By simply searching online, they can find details like the technologies a company uses, employee information, login pages, and even internal portals. This kind of information can later be used to carry out social engineering or more advanced attacks.
Major search engines used:
- Bing
- Yahoo
- DuckDuckGo
Footprinting through web services
During footprinting using web services, we can gather several useful details about a target.
● Target company's top-level subdomains
● Geographical Location
● Performing a Google search
● Determine the OS
● Gathering information from job sites
Footprinting through social networking sites
Social networking sites are one of the easiest ways to gather information about a target. Platforms like LinkedIn, Facebook, and Instagram contain a lot of personal and professional details shared by users.
● Photos shared online can sometimes expose office locations, ID cards, or system screens without realising it.
● Sometimes, users reuse the same username across platforms, which helps in tracking more accounts and gathering extra data.
● Attackers can look at a person's interests, habits, and online behaviour to better understand them.
Website Footprinting
Website footprinting is the process of observing and analysing a target company's website to gather useful information. By simply browsing through the website, a lot of details can be discovered without directly interacting with the system.
While exploring the site, you might find information such as:
● The software being used and its version
● The operating system and scripting platform
● Different sub-directories and URL parameters
● Details like file names, paths, database field names, or queries
● The technologies used to build the website
● Attackers use Burp Suite, Zaproxy, Wappalyzer, and Website Informer. etc.
Network Footprinting
Network footprinting is the process of collecting information about a target's network to understand how it is structured and how different systems are connected. It helps in identifying possible entry points into the network.
During network footprinting, information such as IP addresses, domain names, DNS records, network ranges, and open ports can be gathered. This gives a clearer picture of how the network is organised and what systems are accessible.
By analysing this data, it becomes easier to identify active hosts, running services, and potential weak points in the network.
A key technique used here is traceroute analysis. Traceroute shows the exact path data takes to reach the target, including all the intermediate routers.
DNS Footprinting
DNS: Domain Name System
● DNS footprinting is all about gathering information related to a target's Domain Name System.
During DNS footprinting, the following data is gathered:
● DNS Domain Names
● Computer Names
● IP Addresses
● Subdomains and Hidden Domains
● DNS Records
● DNS Zone Data
● Network-Related Information
● Server Locations and Types
● Hosts within the Network
Whois Footprinting
WHOIS footprinting is simply a way of looking up details about a domain to understand who owns it and how it's registered. It uses publicly available databases, so anyone can access this basic information.
● You can find the name of the domain owner
● You can get contact details like email or phone number
● It shows when the domain was registered
● It shows when the domain will expire
● You can see the name servers being used
● Some details may be hidden for privacy, but useful clues are still available
● It helps you understand how long the domain has been active
● It gives a clear idea of who owns and manages the domain
Email Footprinting
Email footprinting is the process of gathering information about a person or organisation using an email address.
You might find:
● Their name or identity
● Social media profiles linked to that email
● The company or organisation they belong to
● Whether their email was part of any data leaks
● Small clues about their location or activity
Email tracking tools :
● Recipient's system IP Address
● Geolocation
● Email received and read
● Read duration
● Proxy detection
● OS and Browser Information.
Footprinting through Social Engineering
Footprinting through social engineering means collecting information by interacting directly with people instead of using technical tools.
Social engineers try to collect important details like:
● Credit card details and personal identification numbers
● Usernames and passwords
● Information about security tools being used
● Operating system and software versions
● Network structure/layout
● IP addresses and server names
Footprinting Tools
● Nmap → Finds open ports and services on a target
● theHarvester → Collects emails, domains, and subdomains
● Maltego → Shows connections between people, emails, and domains
● Shodan → Finds devices and servers on the internet
● Recon-ng → Automates information gathering
Footprinting Countermeasure
Footprinting countermeasures are the steps taken to protect information from being collected by attackers during the reconnaissance phase.
Common countermeasures:
● They hide domain owner details using WHOIS privacy, so personal info isn't visible publicly
● They avoid sharing employee emails and phone numbers openly on websites
● They properly configure servers so they don't leak extra or sensitive information
● They remove hidden details from files and web pages, like metadata that can reveal system info
● They use tools like firewalls and intrusion detection systems to block suspicious activity
● They watch for and stop unauthorised scanning or probing attempts
● They also train employees to avoid falling for social engineering tricks
