Context
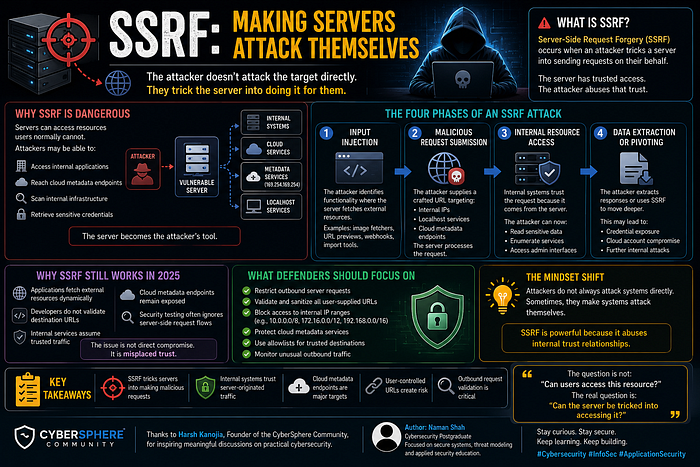
During a recent technical discussion within the CyberSphere Community, we explored a dangerous and often misunderstood vulnerability: Server-Side Request Forgery (SSRF).
The focus was not direct exploitation.
It was trust inside infrastructure.
Not because servers are intentionally insecure.
But because applications often trust requests made from their own environment.
The session was designed for beginners and cybersecurity learners who want to understand how attackers manipulate servers into making unintended requests to internal or external systems.
Session Objective
The discussion focused on:
Understanding how SSRF vulnerabilities occur Breaking down how attackers abuse server-side requests Explaining why SSRF is dangerous in cloud environments Understanding how defenders can prevent SSRF attacks
What SSRF Really Means
Server-Side Request Forgery (SSRF) occurs when an attacker tricks a server into sending requests on their behalf.
Instead of communicating directly with the target:
The attacker uses the vulnerable server as the requester.
This is dangerous because servers often have:
Internal network access Trusted permissions Access to cloud metadata services Visibility into restricted systems
The attacker abuses that trust.
Why SSRF Is Dangerous
Servers can access resources users normally cannot.
If attackers control server-side requests, they may:
Access internal applications Reach cloud metadata endpoints Scan internal infrastructure Retrieve sensitive credentials
The server becomes the attack tool.
The Four Phases of an SSRF Attack
1. Input Injection
The attacker identifies functionality where the server fetches external resources.
Examples include:
Image fetchers URL previews Webhook integrations Import tools
The application accepts user-controlled URLs.
2. Malicious Request Submission
The attacker supplies a crafted URL.
Instead of a normal external site, the request targets:
Internal IP addresses Localhost services Cloud metadata endpoints
The server processes the request.
3. Internal Resource Access
Because the request comes from the server itself:
Internal systems trust it.
The attacker may now:
Read sensitive data Enumerate internal services Access administrative interfaces
The attack bypasses external network restrictions.
4. Data Extraction or Pivoting
The attacker extracts responses or uses SSRF to move deeper into the environment.
This may lead to:
Credential exposure Cloud account compromise Further internal attacks
The server becomes a bridge into protected infrastructure.
Why SSRF Still Works in 2025
Despite growing awareness, SSRF vulnerabilities still exist because:
Applications fetch external resources dynamically Developers do not validate destination URLs Internal services assume trusted traffic Cloud metadata endpoints remain exposed Security testing often ignores server-side request flows
The issue is not direct compromise.
It is misplaced trust.
What Defenders Should Actually Focus On
To prevent SSRF attacks, organizations should:
Restrict outbound server requests Validate and sanitize all user-supplied URLs Block access to internal IP ranges Protect cloud metadata services Use allowlists for trusted destinations Monitor unusual outbound traffic
Servers should not trust arbitrary destinations.
The Beginner Mindset Shift
If you are learning cybersecurity, understand this:
Attackers do not always attack systems directly.
Sometimes, they make systems attack themselves.
SSRF is powerful because it abuses internal trust relationships.
Key Takeaways
SSRF tricks servers into making malicious requests Internal systems often trust server-originated traffic Cloud metadata endpoints are major targets User-controlled URLs create risk Outbound request validation is critical
The attacker may never touch the target directly.
The server does it for them.
Closing Thought
The question is not:
"Can users access this resource?"
The real question is:
"Can the server be tricked into accessing it?"
Because in SSRF attacks, trust inside infrastructure becomes the vulnerability.
Acknowledgement
Thanks to Harsh Kanojia, Founder of the CyberSphere Community, for encouraging discussions focused on modern application security and real-world infrastructure attacks.
Author
Naman Shah Cybersecurity postgraduate focusing on secure systems, threat modeling, and applied security education.