Hash Cracking Fundamentals Every Junior Pentester Should Understand
Author: Ahmed Abdelaziz Eldkrory (EDGAR) Junior Penetration Tester 📧 ahmed.a.eldkrory@gmail.com 🔗 linkedin.com/in/ahmed-eldkrory
Room Link: https://tryhackme.com/room/crackthehash

Password hashing is one of the most widely used credential protection mechanisms in modern systems — yet it is also one of the most frequently misunderstood and misimplemented. Understanding how hashes work, how they fail, and how security professionals analyze them is a foundational skill for anyone entering the field of penetration testing. This article documents my learning journey through the Crack the Hash room on TryHackMe, focusing on conceptual depth, security-oriented reasoning, and practical technique — not just answers.
Overview
This room introduces the core concepts of password hashing and hash cracking from a practical cybersecurity perspective. Rather than treating hashing as an abstract topic, it places the learner directly in scenarios that mirror real-world conditions — analyzing unfamiliar hashes, selecting the right tools, and recovering plaintext values from progressively more complex formats.
The room is structured across two levels, each demanding a different set of skills and tools. Level 1 builds confidence by using online lookup services and basic identification techniques. Level 2 pushes further by requiring dedicated cracking software, making it an ideal bridge between beginner and intermediate security knowledge.
Room Introduction
The central question this room answers is: what happens after an attacker or penetration tester obtains a password hash?
In most authentication systems, passwords are not stored in plaintext. Instead, they are passed through a hashing function — a mathematical operation that produces a fixed-length output known as a hash. During login, the system hashes the entered password and compares it to the stored value. This design means that even if a database is compromised, the raw passwords are not immediately exposed.
However, this protection is only as strong as the algorithm used and the password itself. Older algorithms like MD5 and SHA-1 were designed for speed — a property that makes them efficient but catastrophically weak for password storage, since speed also benefits attackers running millions of guesses per second.
This room teaches you to think from both sides: understanding why systems use hashing, and understanding exactly how that protection breaks down when the wrong choices are made.
Why This Topic Matters in Cybersecurity
Hashing appears everywhere in security work. For penetration testers, encountering hashes is almost inevitable — whether pulled from a compromised database, extracted from a backup file, or dumped from a system during post-exploitation. Knowing how to analyze and crack them is not optional knowledge; it is core to the job.
But the value goes beyond offense. Defenders who understand how hashing can be defeated are far better equipped to recommend secure configurations, enforce proper password policies, and design systems that remain resilient even if credentials are exposed. A finding like "all user passwords are stored as unsalted MD5 hashes" carries very different weight when you can demonstrate exactly how quickly those hashes can be reversed.
For junior pentesters, this room also reinforces a broader mindset: tools are multipliers, not substitutes for understanding. Knowing which tool to run is less important than understanding why it works — and that comes from mastering the fundamentals first.
Core Concept: Hashing
Before diving into the tasks, it helps to revisit what hashing actually is and what makes a hash "cryptographic."
A hashing function takes input of any size and produces a fixed-length output. The key properties that define a strong cryptographic hash are:
- Deterministic — the same input always produces the same output
- One-way — you cannot reverse the output to recover the input
- Fixed-length — regardless of input size, the output length is constant
- Collision-resistant — it should be computationally infeasible for two different inputs to produce the same hash
A useful mental model is a one-way door: data goes in, a hash comes out, but you cannot walk back through it. This is why hashing is used for password storage rather than encryption — you never need to retrieve the original password, only verify it.
The problem is that not all hashing algorithms are built equal. MD5 and SHA-1 are fast by design, which was never a problem when they were created for data integrity checks. But in password security, speed is the enemy. A modern GPU can compute billions of MD5 hashes per second, meaning that with a large enough wordlist or enough computing power, weak passwords stored as MD5 can be recovered in moments.
Room Structure
The room is divided into two levels, each building on the skills of the last.
Level 1 focuses on recognizing hash formats and recovering weak passwords using publicly available online tools and lookup databases. Many commonly used passwords have already been cracked and catalogued — searching for their hashes can yield instant results.
Level 2 removes that convenience and introduces dedicated cracking tools. When a hash does not appear in any public database, you need to generate candidate hashes yourself and compare them. This is where tools like Hashcat and John the Ripper become essential.
Identifying Hashing Algorithms
Before attempting to crack a hash, you need to know what you are dealing with. Different algorithms produce outputs of different lengths and formats, and cracking tools require you to specify the correct mode.
A 32-character hexadecimal string is likely MD5. A 40-character string points toward SHA-1. A 64-character string suggests SHA-256. Hashes beginning with $2y$ or $2a$ indicate bcrypt, and the prefix $6$ signals SHA-512crypt — a Unix-style format with built-in salting.
Useful identification tools include:
- hashid — a command-line utility that analyzes hash format and suggests likely algorithms
- hash-identifier — similar functionality with a different interface
- TunnelsUp Hash Analyzer — a web-based tool at tunnelsup.com/hash-analyzer
- dCode Cipher Identifier — useful for ambiguous or less common formats at dcode.fr
Getting the algorithm right is essential. Running Hashcat with the wrong mode flag will produce no results — not because the password is strong, but because the tool is working with incorrect assumptions.
Level 1 — Basic Hash Cracking
Context
Level 1 presents a series of hashes that represent common password patterns. The goal is to identify each algorithm and recover the plaintext value using online tools and lookup services.
Many weak or commonly used passwords have been cracked before and stored in public rainbow table databases. Services like CrackStation maintain enormous databases of precomputed hashes, allowing instant lookups for matches. This works well for passwords that are short, common, or previously exposed — but offers nothing for strong, unique passwords or properly salted hashes.
Security Perspective
During real engagements, penetration testers frequently encounter credential material from sources like misconfigured backup files, compromised databases, or credential dumps obtained during post-exploitation. The ability to quickly assess and crack those hashes demonstrates the real-world impact of weak password storage and helps clients understand exactly what an attacker with database access could achieve.
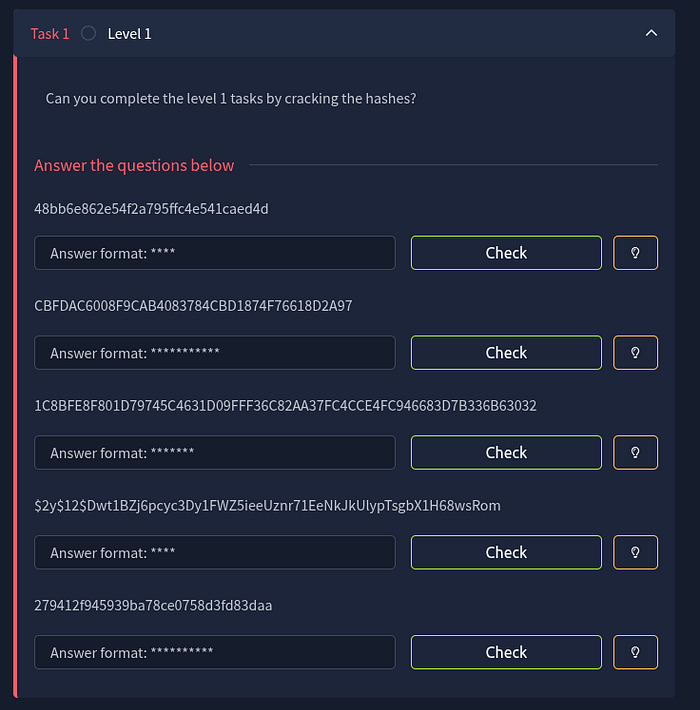
Q&A — Task 1
Question 1
Hash: 48bb6e862e54f2a795ffc4e541caed4d
Method
Using dCode's Cipher Identifier, the hash was quickly recognized as MD5 — a 32-character hexadecimal string consistent with that algorithm. The MD5 Decoder on the same platform was used to look up the corresponding plaintext.
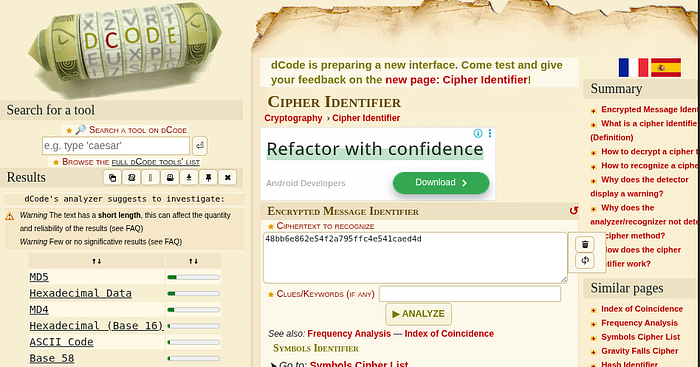

Answer: easy
Explanation
The password "easy" is extremely common and exists in virtually every hash database. When fast, unsalted algorithms like MD5 are used to store passwords, even single-word passwords like this can be reversed in seconds. This is a textbook example of why algorithm selection matters enormously in password storage design.
Question 2
Hash: CBFDAC6008F9CAB4083784CBD1874F76618D2A97
Method
Running the hash through hashid on Kali Linux returned SHA-1 as the most likely algorithm, consistent with the 40-character hexadecimal output. The hash was then submitted to CrackStation, which confirmed a match in its database.
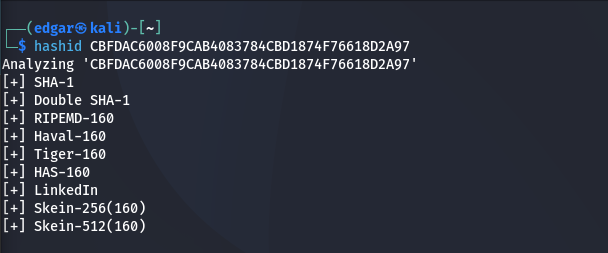
Answer: password123
Explanation
"password123" is one of the most commonly used passwords in the world, which means its SHA-1 hash has been in public rainbow tables for years. Despite SHA-1 being a more modern algorithm than MD5, the weakness here is not the algorithm — it is the password. Even a cryptographically stronger hash cannot protect an inherently predictable input.
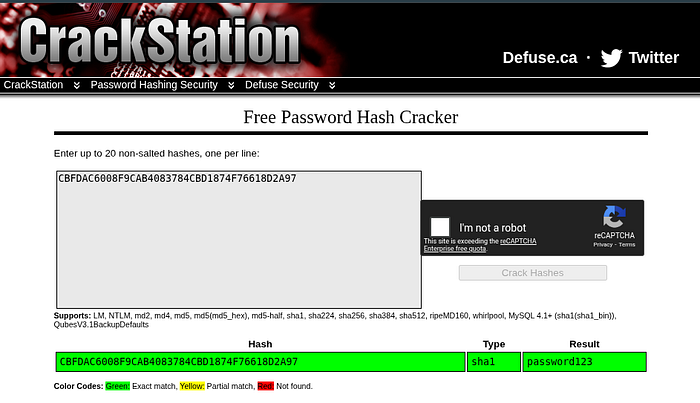
Question 3
Hash: 1C8BFE8F801D79745C4631D09FFF36C82AA37FC4CCE4FC946683D7B336B63032
Method
Running hashid suggested SHA-256 as the most likely algorithm, consistent with the 64-character hexadecimal format. CrackStation was used to look up the plaintext.

Answer: letmein
Explanation
"letmein" is another password that appears near the top of every common password list. SHA-256 is a significantly stronger algorithm than MD5 or SHA-1, but that strength is irrelevant here. If the password itself is weak and widely used, its hash will already be stored in public databases. The algorithm only matters when the password is not already known.
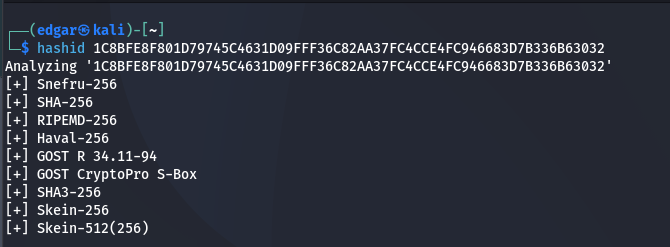
Question 4
Hash: $2y$12$Dwt1BZj6pcyc3Dy1FWZ5ieeUznr71EeNkJkUlypTsgbX1H68wsRom
Method
The $2y$ prefix immediately identifies this as a bcrypt hash. TunnelsUp Hash Analyzer confirmed the format, also revealing the embedded salt and cost factor. Because bcrypt is deliberately slow, online lookup services are ineffective — this one requires local cracking.
The hash was saved to a file, and the rockyou wordlist was filtered down to only four-letter passwords using grep. John the Ripper was then run against the hash in bcrypt mode with this custom wordlist.
echo '$2y$12$Dwt1BZj6pcyc3Dy1FWZ5ieeUznr71EeNkJkUlypTsgbX1H68wsRom' > by.txt
grep -x '.\{4\}' /usr/share/wordlists/rockyou.txt > short.txt
john --format=bcrypt by.txt --wordlist=short.txt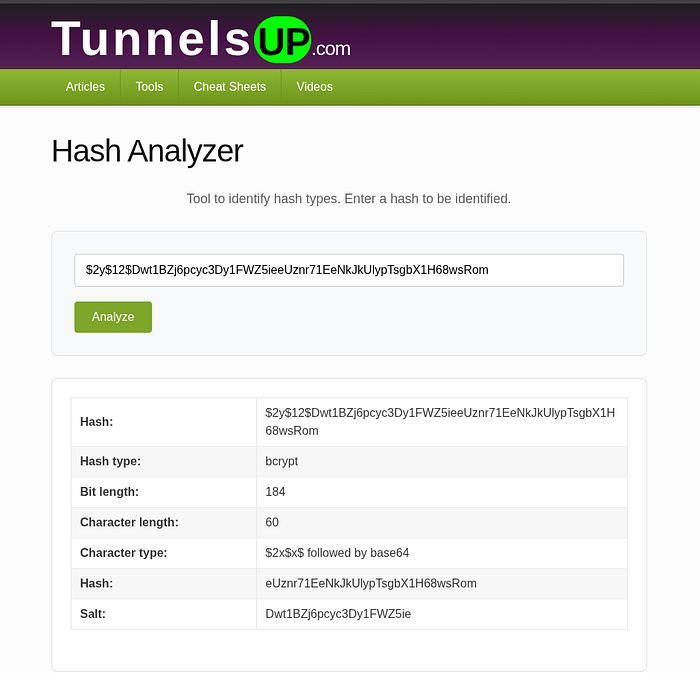
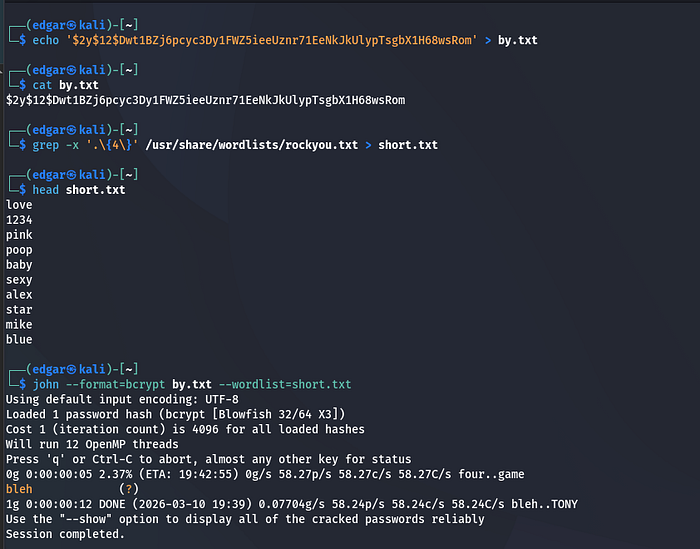
Answer: bleh
Explanation
bcrypt is one of the strongest commonly used password hashing algorithms — it is slow by design, with a tunable cost factor that makes brute-force attacks expensive. However, it still cannot protect a password that exists in a wordlist. By narrowing the candidate list to four-letter passwords and matching the answer format hint, John the Ripper recovered the password in seconds. The lesson: even a strong algorithm cannot compensate for a weak password.
Question 5
Hash: 279412f945939ba78ce0758d3fd83daa
Method
The 32-character hexadecimal format suggested MD4 or MD5. CrackStation was used to look up the hash, which returned a match immediately.
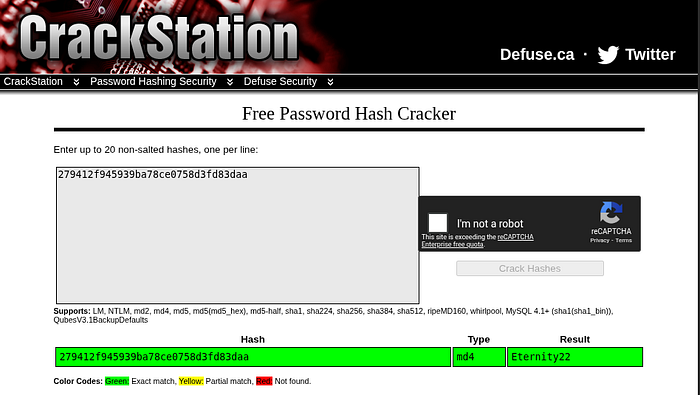
Answer: Eternity22
Explanation
CrackStation identified this as an MD4 hash. "Eternity22" is less obviously weak than "easy" or "password123," but it had appeared in previous data breaches and was therefore already catalogued. This reinforces an important point: a password does not need to be simple to be at risk. Passwords from previous leaks are permanently vulnerable to lookup-based attacks, regardless of their apparent complexity.
Key Learning Insight
Level 1 demonstrates a clear pattern: the moment a password is stored using a fast, unsalted algorithm, its protection becomes entirely dependent on the obscurity of the password itself. Online databases have already done the work of cracking millions of common passwords. If your password is in those databases, your hash will be cracked instantly — no matter the algorithm.
This is why modern authentication systems use slow algorithms like bcrypt, scrypt, or Argon2, combined with unique per-user salts, to make each hash resistant to precomputed attacks and slow to brute-force.
Level 2 — Advanced Hash Cracking with Hashcat
Context
Level 2 increases the difficulty considerably. Online lookup services alone are no longer sufficient — the hashes here represent passwords that may not exist in public databases, requiring active cracking with dedicated tools.
The primary wordlist used throughout this level is rockyou.txt, a file containing millions of real passwords collected from historical data breaches. It has become a standard resource in penetration testing training because it mirrors the kinds of passwords real users actually choose.
Security Perspective
When hash databases come up empty, penetration testers turn to tools like Hashcat and John the Ripper. These tools do not look up precomputed hashes — they generate them live, hashing each candidate from a wordlist and comparing it to the target. This approach is slower but works for passwords that have never been publicly cracked before.
Knowing how to configure these tools correctly — selecting the right hash mode, structuring the input file, and interpreting the output — is a practical skill that separates testers who understand their tools from those who simply run them.
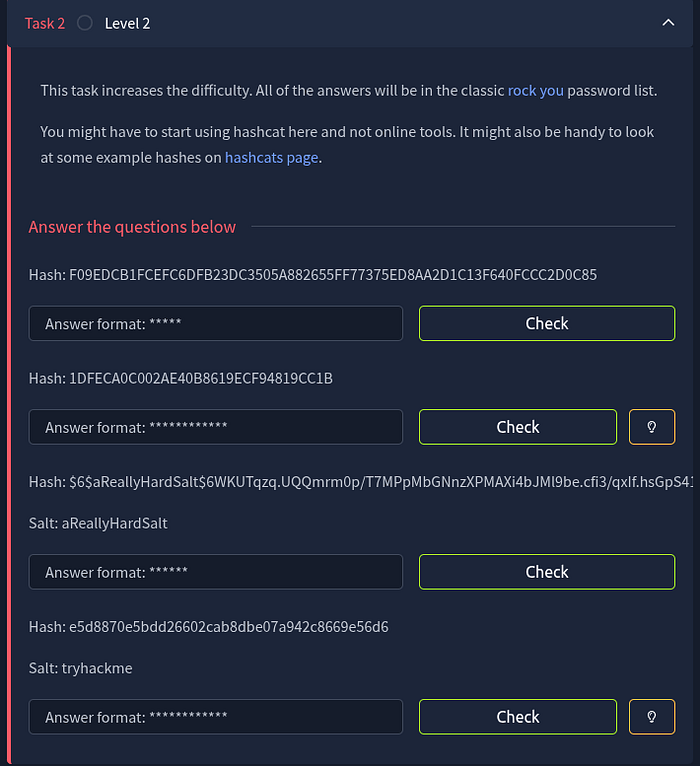
Q&A — Task 2
Question 1
Hash: F09EDCB1FCEFC6DFB23DC3505A882655FF77375ED8AA2D1C13F640FCCC2D0C85
Method
TunnelsUp Hash Analyzer identified this 64-character hexadecimal string as SHA-256. The hash was then submitted to CrackStation to check for a match in its database.
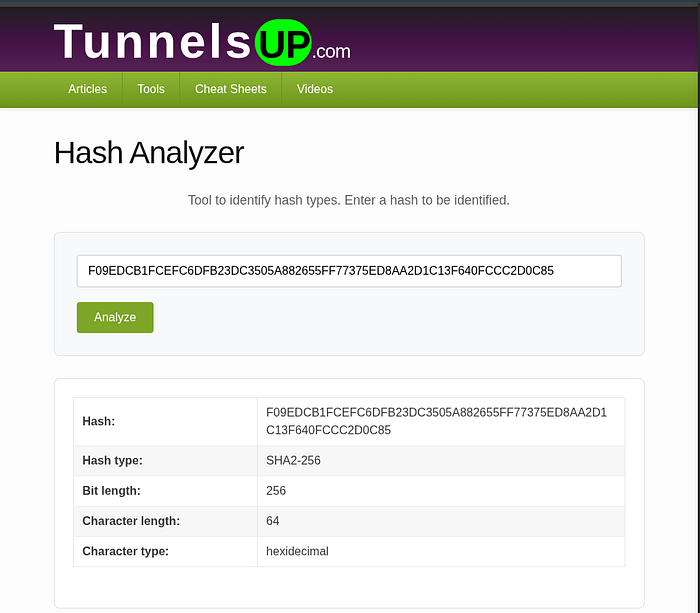
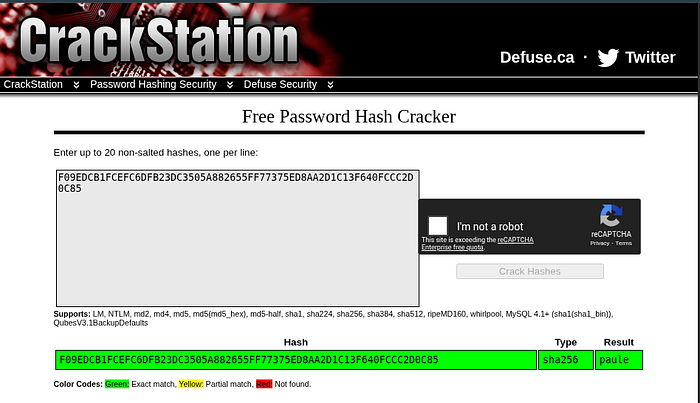
Answer: paule
Explanation
Despite being listed under Level 2, this hash was found in CrackStation's database — a reminder that tool selection should always start with the fastest approach. "paule" is present in the rockyou wordlist, which is likely why it exists in lookup databases. This reinforces the value of trying the simple approach before committing to computationally expensive local cracking.
Question 2
Hash: 1DFECA0C002AE40B8619ECF94819CC1B
Method
hashid was used to analyze the hash, returning several possible algorithms for the 32-character hexadecimal format — including MD5, MD4, and NTLM. CrackStation was used for a lookup.


Answer: n63umy8lkf4i
Explanation
CrackStation identified the hash type as NTLM and matched it to "n63umy8lkf4i." This is a visually strong-looking password — it contains numbers and lowercase letters in no obvious pattern. Yet it exists in the rockyou wordlist, which means it appeared in a real breach at some point. This is a critical lesson: apparent complexity is not the same as actual strength, especially if the password has been used before and leaked.
Question 3
Hash: $6$aReallyHardSalt$6WKUTqzq.UQQmrm0p/T7MPpMbGNnzXPMAXi4bJMl9be.cfi3/qxIf.hsGpS41BqMhSrHVXgMpdjS6xeKZAs02. Salt: aReallyHardSalt
Method
The $6$ prefix is a reliable identifier for SHA-512crypt — the Unix shadow password format that includes an embedded salt and multiple hash rounds. Online lookup services cannot crack salted hashes, so local cracking with John the Ripper was necessary.
echo '$6$aReallyHardSalt$6WKUTqzq...' > h6.txt
john --format=sha512crypt h6.txt --wordlist=/usr/share/wordlists/rockyou.txt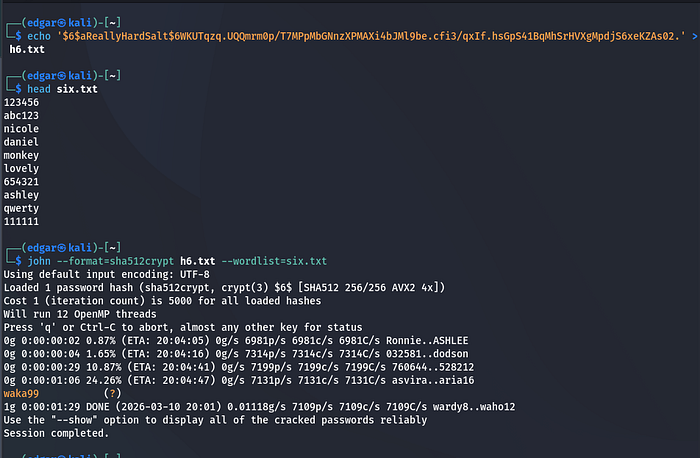
Answer: waka99
Explanation
SHA-512crypt with a unique salt is a genuinely strong hashing scheme — it prevents precomputed attacks and makes each hash computationally expensive to crack. But "waka99" is in the rockyou wordlist, which means a dictionary attack succeeded despite the strong algorithm. Salting and slow hashing protect against scale; they cannot protect against a password that an attacker will simply try anyway. The password itself remains the last line of defense.
Question 4
Hash: e5d8870e5bdd26602cab8dbe07a942c8669e56d6 Salt: tryhackme
Method
TunnelsUp Hash Analyzer identified this 40-character hexadecimal string as SHA-1. Because the hash is salted with a known value ("tryhackme"), it needs to be cracked in the format hash:salt. Hashcat was used with mode 160, which corresponds to HMAC-SHA1 with the key as the salt.
echo 'e5d8870e5bdd26602cab8dbe07a942c8669e56d6:tryhackme' > h7.txt
hashcat -a 0 -m 160 h7.txt /usr/share/wordlists/rockyou.txt --force
hashcat --show -m 160 h7.txt
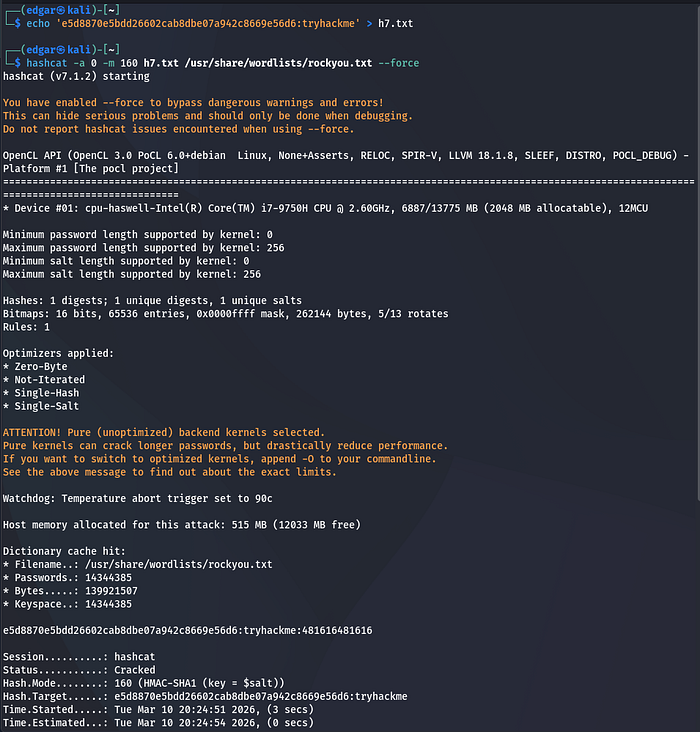

Answer: 481616481616
Explanation
Hashcat successfully matched the salted SHA-1 hash using the rockyou wordlist. "481616481616" is a repetitive numeric string that appears in the wordlist from previous breach data. Even with salting applied, the password was recoverable because it exists in a wordlist. This is one of the clearest demonstrations in the room: salting makes mass cracking harder, but it does not protect individual weak passwords from targeted dictionary attacks.
Common Challenges and Key Insights
Several concepts trip up beginners when approaching this topic for the first time.
The most common source of confusion is conflating hashing with encryption. Encryption is reversible — it is designed to protect data that needs to be retrieved. Hashing is irreversible — it is designed to verify data without storing it. Treating a hash as encrypted data leads to fundamental misunderstandings about both how they work and how they fail.
Another frequent mistake is over-relying on tools without building conceptual foundations. Running Hashcat produces output, but understanding why mode 160 is correct for salted SHA-1, or why bcrypt requires a different cracking approach than MD5, requires knowledge that goes beyond tool usage. The tools amplify your understanding; they do not replace it.
Finally, many beginners underestimate how much the password itself matters. The most important takeaway from this room is that security depends on both the algorithm and the password. A perfectly configured bcrypt hash protecting a password from rockyou.txt offers essentially no real protection. A well-chosen, unique password stored in MD5 is still highly vulnerable. The strongest configuration combines both: a modern adaptive algorithm and a genuinely strong, unique password.
Key Takeaways
- Hashing is a one-way process — it is designed to verify, not to conceal retrievably
- Fast algorithms like MD5 and SHA-1 are unsuitable for password storage due to their speed
- Online databases can instantly reverse hashes for any password that has appeared in a previous breach
- Dedicated tools like Hashcat and John the Ripper enable dictionary and brute-force attacks locally
- Identifying the hash algorithm correctly is always the first step — wrong mode means no results
- Salting prevents precomputed (rainbow table) attacks but does not stop dictionary attacks on weak passwords
- Modern adaptive algorithms like bcrypt, scrypt, and Argon2 are the correct choice for password storage
- Even strong algorithms cannot protect passwords that exist in wordlists
Real-World Relevance
These skills translate directly into professional security work. During penetration tests, hash cracking is used to demonstrate the real-world impact of a credential exposure — not just to report "we found password hashes," but to show exactly how many of those hashes can be reversed, what percentage of users had weak passwords, and what an attacker with the same data could access.
In incident response, the same techniques help analysts understand the scope of a breach. In password auditing engagements, they provide the evidence needed to argue for stronger password policies and algorithm upgrades.
Mastering hash cracking also builds the foundation for more advanced credential-based techniques: NTLM relay attacks, pass-the-hash, Kerberoasting, and credential stuffing all depend on a solid understanding of how credentials are stored and where the weaknesses lie.
Conclusion
The Crack the Hash room delivers exactly what its title promises — practical, hands-on experience with the tools and techniques used to analyze and recover password hashes. But the deeper value is conceptual. Every hash cracked in this room is a demonstration of a real failure mode: a weak password, a fast algorithm, missing salting, or a combination of all three.
From Level 1's instant online lookups to Level 2's local dictionary attacks with Hashcat and John the Ripper, the room builds a complete picture of how hash cracking actually works in practice. More importantly, it builds the mindset that effective security professionals need: understanding how systems fail is the first step toward building systems that hold.
For anyone starting out in penetration testing or cybersecurity, these fundamentals are not optional. They are the foundation everything else is built on.
This write-up is intentionally focused on learning outcomes, conceptual understanding, and ethical cybersecurity practice. It documents reasoning and methodology without exposing platform content or reproducing lab material directly.