Introduction: The Graveyard of Almost-Pro Hunters
A beginner discovers the field. They get excited — genuinely, deeply excited. The idea that you can get paid to find security flaws in real systems, that ethical hacking is a legitimate professional path, that the technical skills they've been building have direct market value — it's compelling on every level. They start learning. They work hard. They make real progress.
And then, somewhere between beginner and professional, they stop. Not dramatically. Not with a clear decision point. They just quietly fade — still technically in the game, still occasionally browsing programs, still telling people they're "working on bug bounty" — but never actually crossing the threshold into consistent, professional-level results.
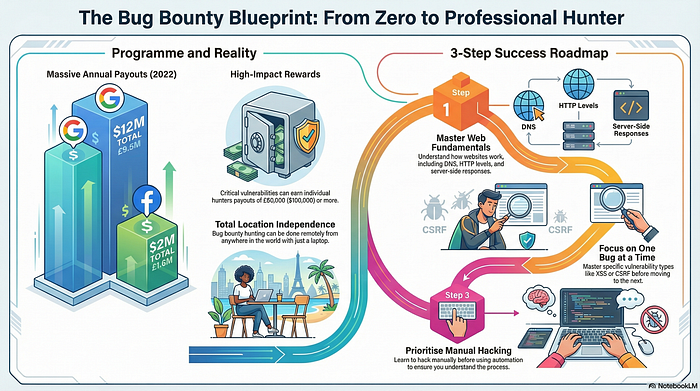
This is the problem that the Bug Bounty Blueprint 2026 is built to solve.
Here's the myth that creates this graveyard of almost-pro hunters: "Turning professional is a natural progression — if you keep learning and keep trying, you'll eventually get there." It sounds encouraging. It's actually paralyzing, because it frames pro-level performance as an inevitable destination rather than a deliberate construction.
The real issue isn't patience or persistence. It's validation — specifically, the absence of a structured framework that tells you exactly what phase you're in, what skills matter in that phase, and what the specific transition criteria are to the next one. Without that framework, effort becomes circular. This complete beginner-to-advanced roadmap is that framework.
The Bug Bounty Blueprint 2026: What This Roadmap Is Actually Built to Solve
Most bug bounty roadmaps are organized around content categories — here's what to learn about web vulnerabilities, here's a list of tools, here's a general methodology. They're useful as reference material. They fail as progression guides because they describe a landscape without telling you where you are in it or where to walk next.
This blueprint is organized around phases — distinct stages of development with specific characteristics, common failure modes, and clear transition signals. The four phases are beginner, intermediate, advanced, and professional. Each phase demands different things from you. Treating an intermediate challenge with a beginner's approach, or expecting beginner-phase comfort in the advanced phase, produces the stagnation that sends so many hunters to the almost-pro graveyard.
Understanding which phase you're in isn't about ego or self-assessment. It's about resource allocation — knowing where to invest your time, attention, and energy for maximum forward movement.
The Real Reason Beginners Stall — And It's Not What They Think
Ask a stalled hunter why they haven't progressed, and they'll almost always identify a technical gap. They need to learn more about a specific vulnerability class. They need to get better at recon. They need to understand a technology they haven't mastered yet. The technical gap is real, but it's rarely the primary blocker.
The primary blocker is almost always a process gap — the absence of a repeatable approach to selecting targets, conducting research, managing hunting sessions, and submitting quality reports. Without process, technical skill has no structure to operate within. The hunter who knows everything about SQL injection but has no systematic approach to identifying where injection points might exist in a real application will consistently underperform a technically average hunter with a clear, repeatable testing methodology.
The intellectual insight here is sharp: technical knowledge is the raw material; process is the manufacturing system. Raw material without a manufacturing system sits in a pile and produces nothing. This blueprint is about building the system.
What "Turning Pro" Actually Means in 2026
Before committing to a roadmap, it's worth being precise about the destination. "Turning pro" in bug bounty doesn't necessarily mean full-time income replacement on day one. In 2026, it means operating with professional standards — consistent methodology, high-quality reports, strategic program selection, and reliable enough output that earnings are predictable rather than random.
Some hunters reach this level while maintaining other professional commitments. Others eventually transition to full-time hunting. The professional standard is the same regardless of the time investment. What varies is how quickly that standard can be reached and what earning level it produces. This blueprint applies to both paths.
Chapter One — The Beginner Phase: Building the Foundation That Doesn't Break
The beginner phase has one primary objective: build a foundation that supports everything that comes after it without requiring reconstruction. This sounds obvious. It's frequently violated, because the most natural beginner instinct is to build fast rather than build well.
A foundation that doesn't break isn't the most comprehensive foundation. It's the most structurally sound one — built around the specific knowledge areas that every subsequent phase of development depends on, understood deeply enough to apply flexibly rather than mechanically.
The Minimum Viable Knowledge Stack
The beginner phase requires mastery of a deliberately limited set of concepts before expanding. For a hunter focusing on web application security — the most accessible and most rewarding starting point in 2026 — that minimum viable knowledge stack includes a functional understanding of HTTP architecture, how authentication and session management work, how browsers process and render responses, how user input travels from client to server and back, and what the most common categories of web vulnerabilities look like in practice.
This is not an exhaustive list of everything worth knowing. It's the specific set of concepts that makes genuine hunting possible. With this stack in place, a beginner can engage meaningfully with a real target, recognize potentially interesting behavior, and form testable hypotheses about where vulnerabilities might exist. Without it, every target looks like an incomprehensible wall of complexity.
Build this stack deliberately, verify it through hands-on practice in legal lab environments, and resist the urge to expand it prematurely. The beginner phase is about depth in a small area, not breadth across many.
Why Your First Target Should Be Boring on Purpose
There's a powerful temptation in the beginner phase to target something exciting — a well-known platform, a large-scope program with impressive payout ceilings, a technology you find personally interesting. Resist it.
Your first real target should be chosen for learning value, not excitement value. Look for a program with a clear, well-documented scope, a history of transparent communication with researchers, and an attack surface that matches your current knowledge stack without overwhelming it. The goal of your first several hunts isn't to find a critical vulnerability. It's to develop your process — to practice the full cycle of recon, hypothesis formation, testing, and report writing against a real target with real feedback.
An original example worth considering: a beginner who spends their first three months hunting exclusively on small-scope programs in a single industry vertical — say, software-as-a-service tools for small businesses — develops a specific understanding of how that category of application is typically built, what its common architectural patterns are, and where its characteristic weaknesses tend to appear. That focused experience produces more usable knowledge than three months of scattered hunting across dozens of unrelated targets.
The Dangerous Comfort of Endless Lab Practice
Labs are valuable. They're controlled, legal, and designed to teach specific concepts through deliberate practice. They're also a hiding place — a comfortable simulation that lets beginners feel productive without exposing themselves to the uncertainty and feedback of real-world hunting.
The beginner phase should include lab practice. It should not be dominated by it. Real targets behave in ways that labs don't simulate. Real triage feedback teaches things that completing a lab module never will. The transition from lab to real target should happen early — uncomfortably early, before the beginner feels fully ready — because the learning acceleration that comes from real-world feedback is the most valuable educational resource available at this phase.
Chapter Two — The Intermediate Phase: Where Most Hunters Get Permanently Stuck
The intermediate phase is where the bug bounty graveyard fills up. Hunters who made it through the beginner phase with real skills and real momentum arrive here and encounter a problem that their beginner-phase approach is completely unsuited to solve.
In the beginner phase, progress is visible and relatively predictable. You learn a concept, you practice it, you improve. The feedback loop is tight and legible. In the intermediate phase, progress becomes invisible for long stretches. You're hunting on real programs, submitting real reports, but the results feel random and the path forward is unclear. Most hunters conclude they've hit a ceiling. They haven't. They've hit a transition point that requires a fundamentally different approach.
The Plateau Problem and Its Hidden Cause
The intermediate plateau has a specific, identifiable cause: hunters are applying beginner-phase processes to intermediate-phase challenges. They're still hunting the way they hunted when they started — running the same recon tools, testing the same vulnerability classes in the same sequence, writing reports the same way — and expecting different results because their technical knowledge has grown.
Technical knowledge growth without process evolution produces diminishing returns. The intermediate phase demands a more sophisticated approach to target selection, a more creative approach to vulnerability identification, and a substantially more polished approach to report quality. Hunters who recognize this and deliberately evolve their process break through the plateau. Those who don't stay there indefinitely.
Developing Target Intuition: The Skill That Separates Intermediate From Advanced
Target intuition is the ability to look at an application and quickly develop a sense of where interesting vulnerabilities are most likely to live — which workflows to examine first, which parameter patterns are worth investigating, which architectural choices suggest potential weaknesses. It's not a mystical skill. It's the accumulated pattern recognition that comes from deep, repeated exposure to real targets.
Developing target intuition requires deliberately building a library of mental models — specific, concrete examples of how vulnerabilities present in real applications — through active hunting and careful study of disclosed vulnerability reports. Every public disclosure is a case study. Hunters who read them analytically, asking not just "what was the vulnerability" but "what made this application vulnerable to this, and how would I recognize similar conditions elsewhere," accelerate their intuition development significantly.
How to Use AI Without Letting It Stunt Your Growth
AI-assisted tools have become genuinely useful in the intermediate phase, particularly for accelerating the analysis of large codebases, generating comprehensive test case lists, and summarizing complex technical documentation. Used well, they compress the time required for certain types of analysis significantly.
The risk at the intermediate phase is specific. Hunters who rely on AI to do their analytical thinking — outsourcing the reasoning process rather than just the mechanical work — fail to develop the cognitive muscles that advanced hunting requires. AI can tell you that a parameter pattern resembles something associated with a certain vulnerability class. It cannot tell you whether the business context of this specific application makes that vulnerability exploitable or impactful in a meaningful way. That judgment is the skill. Don't outsource it.
Use AI to handle the mechanical, repetitive work. Protect the reasoning process jealously, because it's the skill that no tool can replicate and no automation can replace.
Chapter Three — The Advanced Phase: Thinking Like a Professional Hunter
The advanced phase represents a qualitative shift in how hunting works — not just more sophisticated technique applied to the same process, but a fundamentally different relationship with the work itself. Advanced hunters don't just find vulnerabilities. They develop deep models of how specific types of targets work, where their characteristic weaknesses tend to emerge, and how to navigate the competitive and interpersonal dynamics of the programs they work with.
This phase is where the transition to professional performance becomes possible. It's also where the intellectual demands of the work become most visible — and most rewarding.
The Professional Mindset Shift That Changes Everything
The single most important transition in the advanced phase is a shift from thinking about vulnerabilities to thinking about systems. A beginner asks: "Is this parameter vulnerable to injection?" An advanced hunter asks: "How does this entire authentication system handle trust decisions, and where are the places where those trust decisions could be manipulated?"
The system-level question produces fundamentally different hunting. It leads to vulnerability chains — combinations of individually minor issues that together produce critical impact. It leads to business logic findings that scanners can never surface. It leads to the kind of deeply contextual, target-specific discoveries that triage teams respond to with immediate recognition of their value.
Developing this mindset requires practice and patience. It also requires deliberately slowing down — spending more time in the analysis phase before moving to active testing. Advanced hunters often spend a larger proportion of their hunting time reading, studying, and modeling than beginners or intermediates do. That investment in understanding pays compound returns in finding quality.
Building Specialization That Programs Actively Seek Out
Advanced hunters who develop genuine, recognized specialization in a specific vulnerability category, technology stack, or industry vertical create a form of professional identity that has real market value in the bug bounty ecosystem.
A hunter known for consistently finding sophisticated authentication vulnerabilities in financial services applications, or for deep expertise in a specific API framework's characteristic weaknesses, becomes someone that programs in those domains want to invite, want to prioritize, and want to develop relationships with. That recognition doesn't happen by accident. It's built through deliberate focus over time — choosing targets that deepen existing expertise rather than constantly exploring new territory.
Specialization feels counterintuitive to many hunters because it seems to limit opportunity. In practice, it expands it. Depth of expertise creates access that breadth of knowledge never does.
Chapter Four — The Pro Layer: Consistency, Reputation, and the Private Program Economy
Reaching professional-level performance in bug bounty isn't the end of the journey. It's the entrance to a different economy — one where the most valuable opportunities are hidden from public view, access is earned rather than applied for, and the competitive dynamics are fundamentally different from public programs.
This is the private program economy, and understanding how it works is essential to the complete beginner-to-advanced roadmap.
What Separates Occasional Earners From Consistent Professionals
Occasional earners find good bugs sometimes. Consistent professionals find good bugs reliably — not because they're luckier, but because they've built systems that produce reliable output. The difference is almost entirely structural.
Consistent professionals maintain active hunting pipelines across multiple programs simultaneously, with clear processes for when to invest more deeply in a target and when to move on. They track their findings, their submissions, their triage outcomes, and their earnings with enough granularity to identify patterns — what's working, what isn't, and where to adjust. They treat hunting as a professional practice with performance metrics rather than a creative pursuit measured only by occasional wins.
Building this structure feels unglamorous. It is unglamorous. It's also the single most reliable predictor of whether a technically capable hunter earns consistently or earns occasionally. Structure is the bridge between skill and income.
The Private Program Flywheel and How to Enter It
Private programs operate on invitation. Invitations come from platforms that track hunter performance metrics — factors like report validity rate, severity distribution of findings, quality of written communication, and responsiveness to triage follow-up questions. These metrics are accumulated across every public program submission you make.
The flywheel dynamic is straightforward: quality public program submissions build metrics, metrics earn invitations, private programs offer better conditions, better conditions produce higher-quality findings, higher-quality findings strengthen metrics further. The flywheel accelerates over time for hunters who enter it. For hunters who don't, the public program landscape becomes increasingly competitive as experienced hunters accumulate private program access and less experienced hunters compete for the remaining open slots.
Entering the flywheel requires one thing above all others: consistent, professional-quality report submissions from the very first one. There is no shortcut. There is no catch-up mechanism. Every submission either builds the flywheel or slows it. Start treating it that way on day one.
Frequently Asked Questions
Q1: How long does each phase of this roadmap realistically take to complete? Phase duration varies significantly based on available time, quality of effort, and how deliberately the transition criteria are pursued. The beginner phase typically spans two to four months for someone investing consistent focused time. The intermediate phase — where most hunters stall — can last anywhere from a few months to several years depending on whether process evolution happens. The advanced phase is an ongoing development rather than a fixed duration. Treating each phase as a deliberate project with specific goals, rather than a time period to endure, compresses the timeline meaningfully.
Q2: Can someone follow this blueprint part-time, or does it require full-time commitment? The blueprint applies regardless of time commitment. What changes is the pace of progression. Part-time hunters who apply the framework deliberately and consistently will progress through the phases — more slowly than full-time hunters, but following the same path with the same transitions. The key is quality and consistency of effort during available time, not total volume of hours.
Q3: Is this roadmap applicable to vulnerability types beyond web applications? The structural framework — phases, transition criteria, process evolution, specialization, reputation building — applies across all major bug bounty domains including mobile applications, API security, cloud infrastructure, and AI system vulnerabilities. The specific technical content of each phase varies by domain. Web applications are emphasized here as the most accessible starting point, not as the only valid specialization.
Q4: How important is community engagement at each phase of this roadmap? Increasingly important as you progress. In the beginner phase, community provides learning resources and motivational support. In the intermediate phase, it provides target intelligence, methodology discussion, and the kind of real-world context that accelerates plateau-breaking. In the advanced phase, community relationships contribute directly to reputation and can lead to collaborative opportunities. Engage authentically rather than transactionally at every phase.
Q5: What's the most reliable signal that you've transitioned from intermediate to advanced? The most reliable signal is a qualitative shift in how you approach targets — from testing specific vulnerability classes in sequence to reasoning about system-level trust relationships and business logic flows. Secondary signals include finding vulnerability chains independently, writing impact statements that triage teams respond to with immediate recognition rather than clarifying questions, and receiving positive triage feedback that references the quality of your analysis rather than just the validity of your finding.
Q6: How should hunters handle extended periods without valid findings — the dry spells that affect everyone? Dry spells are a normal feature of professional bug bounty hunting, not an indicator of incompetence. The productive response is diagnostic rather than emotional. Examine your target selection criteria — are the programs you're hunting on appropriate for your current skill level and the competitive conditions? Examine your process — are there phases of your methodology that have become mechanical rather than thoughtful? Examine your report quality — are there patterns in your triage outcomes that suggest a specific communication gap? Dry spells contain information. Extract it.
Conclusion: The Blueprint Has Always Been There — Most People Just Refuse to Follow It
The complete beginner-to-advanced bug bounty roadmap has always had the same structure. Foundation, then process evolution, then system-level thinking, then professional consistency. The phases have always had the same transition criteria. The traps have always been in the same places — the lab comfort zone, the intermediate plateau, the volume myth, the report quality gap.
What's changed in the 2026 edition of this blueprint is the context: AI tooling that creates both accelerating opportunities and new failure modes, an increasingly mature competitive landscape that rewards specialization over generality, and a private program economy that compounds professional reputation into access advantages that weren't as pronounced in earlier years.
The path from zero to professional hunter is genuinely available. It doesn't require exceptional talent. It doesn't require a specific background. It requires a clear framework, deliberate phase-by-phase progression, the discipline to evolve your process rather than just expand your knowledge, and the professional standards applied consistently from your very first submission.
Most hunters never turn pro because they're waiting to feel ready instead of following the blueprint. The blueprint doesn't care about feelings. It rewards execution.
In 48 hours, I'll reveal the exact six-question phase diagnostic that professional hunters use to assess where they genuinely are in this roadmap — and the specific action it prescribes for each answer. Most hunters who take it are surprised by what it tells them.
💬 Comment Magnet: Looking at these four phases honestly — which one are you actually in right now, and what's the one thing that's been keeping you from moving to the next one?
Get Lifetime Access: Download Now