The Context: Security vs. Infrastructure Constraints
In the world of enterprise architecture, we rarely start with a blank canvas. More often than not, we're faced with the 'Innovation vs. Compliance' Paradox: the business requires modern, high-grade security, but the existing infrastructure is "locked-down," legacy, or heavily restricted.
The Common Hurdles:
- Locked-Down Clusters: Environmentally isolated pods with strict ingress and egress controls.
- Persistence Gaps: Lack of access to managed database services (like RDS or Cloud SQL) and a "No Local Persistence" policy on compute nodes.
- The Goal: Integrating a high-traffic Single Page Application (SPA) with a corporate Identity Provider (IdP) without ever exposing sensitive tokens to the browser.
The Strategy: Architectural Decisions (ADR)
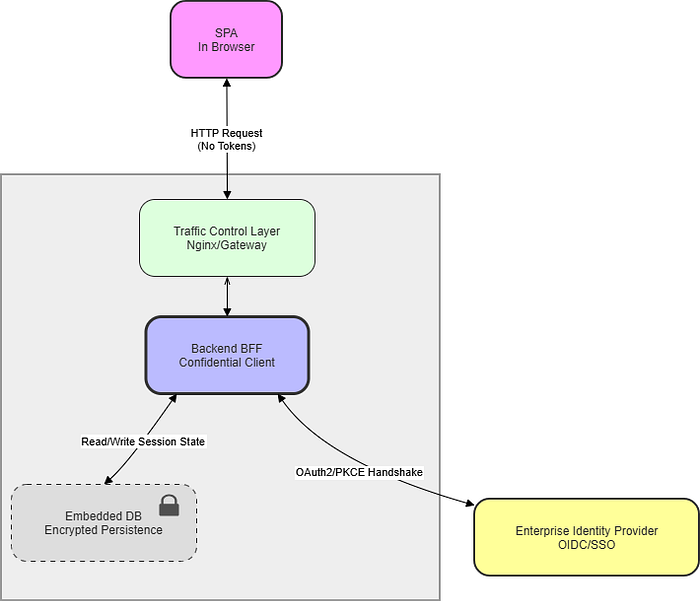
1. Decoupling the Handshake: The BFF Pattern
To mitigate the risk of XSS (Cross-Site Scripting), the architecture eliminates token storage (Access/Refresh) from the browser's LocalStorage entirely.
- The Shift: System design moved the complexity to a Backend-for-Frontend (BFF) component. The server acts as the "Confidential Client," keeping secrets and tokens safely within the network boundary.
2. Abstracted Persistence: From Embedded to Distributed
In environments where a managed database isn't a "day-one" option, the architecture must be flexible.
- The Approach: the architecture utilized a serverless-friendly, embedded storage engine for initial state management.
- The Security Layer: To satisfy "Encryption at Rest" audits, Application-Layer Encryption is implemented. Session data is encrypted using a symmetric pattern (like AES-256) before it ever touches the disk.
- Scalability: This pattern is intentionally storage-agnostic. As concurrency increases, the persistence layer can be swapped for a distributed cluster (like PostgreSQL or Redis) with zero changes to the core auth logic.
3. Hardening the Session: Secure-First Cookies
The architecture moved away from Bearer tokens in the header, opting instead for HttpOnly, Secure, and SameSite=Lax cookies.
- The Result: This configuration prevents client-side scripts from accessing session identifiers while ensuring the reverse proxy handles session affinity seamlessly across the cluster.
The Workflow: The "Pull" Authentication Pattern
Traditional authentication often "pushes" state to the frontend. Instead, the architecture implemented a decoupled "Pull" pattern to keep the UI agnostic of the identity provider.
- Auth Discovery: On load, the UI hits a
AUTH_STATUS_ENDPOINTendpoint. A401 Unauthorizedresponse triggers the redirect logic. - The PKCE Handshake: The backend initiates the redirect to the IdP using a PKCE (Proof Key for Code Exchange) challenge.
- Secure Exchange: Upon return, the backend uses its Client Secret plus the PKCE Verifier to swap the code for tokens.
- State Finalization: The backend encrypts the session, writes it to the abstracted storage, sets the secure cookie, and sends the user back to the app root.
- The Result: The UI simply "pulls" the authenticated profile from the endpoint. It doesn't need to know how the user logged in, only that they are logged in.
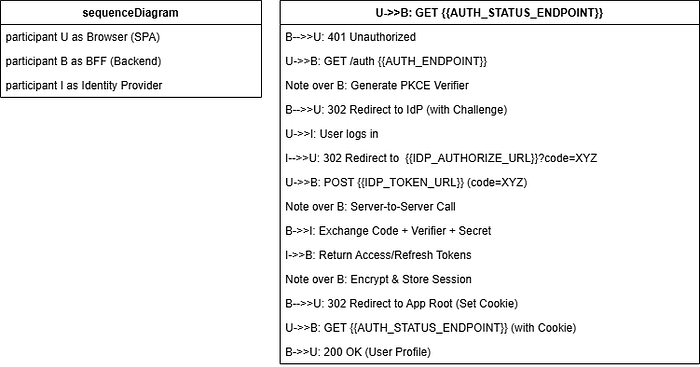
Deep Dive: Why PKCE in a Server-Side Flow?
There's a common myth that if you have a "Confidential Client" (a backend with a secret), you don't need PKCE. In high-security environments, the architecture use PKCE to defend against Authorization Code Interception.
Even if an attacker intercepts the redirect code, they cannot use it without the code_verifier held in the backend's memory for that specific session. It ensures that the browser that started the login is the only one that can finish it.
Future-Proofing and Operations
- Observability: End-to-end request tracing ensures visibility from the entry gateway through to the encrypted storage layer, allowing for high-granularity debugging without logging sensitive data.
- Rate Limiting: To prevent session brute-forcing, one can implement a sliding-window rate limiter at the middleware level.
- Cost & Footprint: This architecture proves that "Zero-Trust" doesn't require a massive infrastructure bill. By leveraging embedded state management and smart encryption, the operational footprint stays lean.
For a Deeper Dive:
- Microsoft: The Backend-for-Frontend (BFF) Pattern
- IETF: OAuth 2.0 for Browser-Based Apps (BFF Guidance)
- Auth0: Why you should use PKCE even for Confidential Clients
- Microsoft identity platform and OAuth 2.0 authorization code flow
Final Thoughts
Architecture is the art of the possible. By combining the BFF pattern with Stateless Encrypted Cookies, you can provide a production-grade SSO experience even when the infrastructure feels like it's fighting you.
The core principle remains simple: Keep the secrets on the server and the view in the browser.
I'd love to hear your thoughts: Have you navigated similar infrastructure "locked-down" scenarios? How did you handle session state? Let's discuss in the comments!
#SoftwareArchitecture #CyberSecurity #BFFPattern #ZeroTrust #CloudNative #WebSecurity #ProductEngineering