Introduction: The MFA Security Paradox
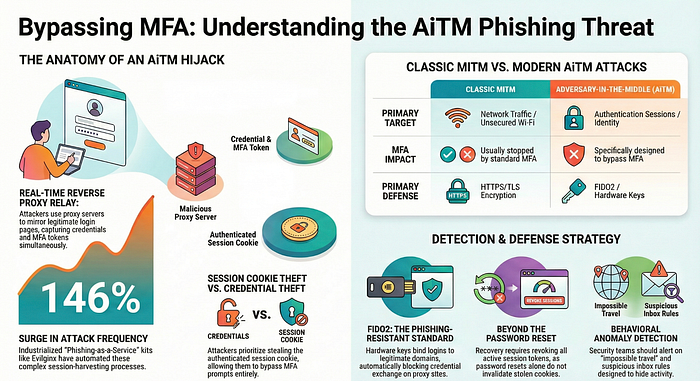
For too long, Multi-Factor Authentication (MFA) has been lauded as the enterprise "silver bullet," the final gate that would end the era of credential phishing. This belief has cultivated a dangerous false sense of security across modern organizations. Intelligence telemetry reveals a grim reality: Adversary-in-the-Middle (AiTM) attacks have seen a staggering 146% surge, with current detections averaging approximately 39,000 incidents every single day.
The sophisticated adversary no longer needs to "break" your MFA. They don't need to brute-force a hardware token or social engineer a help desk. Instead, they simply "borrow" the result of a successful authentication. By positioning themselves between the user and the legitimate service, attackers hijack the verified session in real-time. In this new paradigm, the "Access Granted" screen is not the end of the attack — it is the beginning.
1. The "Middleman" is a High-Speed Proxy, Not an Eavesdropper
To defend against modern identity threats, we must distinguish AiTM from "Classic" Man-in-the-Middle (MitM) attacks. Older MitM tactics exploited network-layer weaknesses, like unsecured Wi-Fi or ARP spoofing, to eavesdrop on unencrypted data. The universal adoption of HTTPS and TLS encryption rendered these eavesdropping techniques largely obsolete. In response, attackers shifted from the network layer to the authentication layer.
Modern toolkits like Evilginx2 and Modlishka function as high-speed reverse proxies, acting as a bridge that relays traffic between the victim and the legitimate identity provider (IdP) like Microsoft Entra ID or Okta. However, we are now seeing the rise of the Indirect Proxy — a method pioneered by threat actors like Storm-1167. Unlike a reverse proxy that simply passes packets, an indirect proxy presents a mimicked page to the victim while simultaneously initiating a separate, automated backend session with the IdP. This gives the adversary total control over the phishing interface, allowing them to bypass security headers and modify content dynamically to evade detection.
2. Session Cookies Are the New "Crown Jewels"
In an AiTM campaign, the password is a secondary prize. The primary objective is the session cookie — the post-authentication token that represents a "verified" status. By capturing this token, an attacker inherits the user's digital identity and can bypass MFA challenges entirely for the duration of the token's life.
Technical analysis of modern phishing kits reveals the use of client-side credential stealers like inject.js. This script is injected into the proxied session to monitor the DOM and exfiltrate what the industry calls CRITICAL_COOKIES. Specifically, actors are harvesting tokens such as idx, JSESSIONID, proximity_, DT, sid, and proximity_. Once these are captured, the attacker can import them into a specialized browser and walk into the environment as a "fully verified" user. This is why traditional password resets are a dangerously insufficient remediation tactic; if the session cookie remains active, the attacker maintains access regardless of the new password.
3. The Industrialization of Phishing (PhaaS)
The complexity of executing a real-time relay attack used to be a barrier to entry, limited to advanced persistent threats. That barrier has vanished with the commoditization of "Phishing-as-a-Service" (PhaaS). This industrialization has fueled a 46% surge in sophisticated phishing kits in 2025 alone.
Lower-skilled actors can now rent ready-made kits like Mamba 2FA and Tycoon 2FA for a monthly subscription. These kits provide high-fidelity templates that mimic legitimate services with pixel-perfect accuracy. They automate the proxying of traffic, the harvesting of MFA codes, and the exfiltration of cookies, making "high-fidelity" phishing accessible to any actor with a credit card. The threat is no longer a lone genius; it is a scalable, automated industry.
4. "Impossible Travel" is Moving Inside the Session
Most Security Operations Centers (SOCs) are flying blind because their SIEM logic is centered on the login event. To a standard monitoring tool, an AiTM login looks like a successful, legitimate authentication. Detection must shift from the login event to behavior inside the authenticated session.
The primary indicator of a hijack is a variation of "Impossible Travel," but it must be viewed through the lens of infrastructure shifts rather than just geography. Analysis reveals that a "verified" session frequently appears first at a legitimate residential IP address and then, within minutes, performs actions from an entirely different ASN or ISP — often a VPS provider like DigitalOcean or Vultr. As noted by ThreatHunter.ai, most security teams have "zero visibility" into the session once the user is logged in. Identifying when a single Session ID suddenly switches from a residential Comcast line in New York to a DigitalOcean droplet in Tokyo is the only way to catch a session hijacker in the act.
5. Persistence via "Rogue Authenticators" and Hidden Rules
The initial "hook" is often a sophisticated lure hosted on legitimate, trusted platforms like Canva or SharePoint to bypass email filters. Attackers favor high-urgency themes such as "Salary & Bonus Information" or "Fax document preview." Once access is gained, the adversary moves to secure persistence through "Rogue Authenticators."
A common tactic involves adding a new MFA method — specifically "OneWaySMS" — using a phone number with an Iranian (+98) country code. This allows the attacker to generate their own MFA challenges if the original session expires. To hide their tracks, they implement "Inbox Rules" that redirect incoming mail to the "RSS Subscriptions" or "Archive" folders.
This is where the psychological warfare begins. The attacker monitors the inbox in real-time, deleting "undelivered" notices and even replying to colleagues who question the legitimacy of the phishing link. By confirming to a coworker that "the link is safe," the attacker leverages the victim's internal trust to expand the breach.
6. The Only Real Defense is "Phishing-Resistant" MFA
Standard MFA — SMS codes, voice calls, and simple push notifications — is no longer sufficient. These methods are "shared secrets" that can be intercepted and proxied by the kits mentioned above. The only robust defense is a transition to phishing-resistant MFA built on FIDO2/WebAuthn hardware keys.
FIDO2 keys use public-key cryptography to "bind" the authentication to the specific, legitimate domain of the service. If a user is tricked into visiting a malicious proxy site, the hardware key detects the domain mismatch and automatically blocks the exchange of credentials. Beyond hardware, organizations must implement Continuous Access Evaluation (CAE), which allows the IdP to revoke active tokens in real-time if a session is deemed risky, rather than waiting for the token to expire.
The 30-Day Readiness Roadmap
To transition from legacy defenses to a Zero Trust architecture capable of defeating AiTM, organizations should adopt the following 30-day plan:
- Week 1: Audit
- Map all privileged accounts (Admins, Finance, C-Suite) and identify those relying on non-phishing-resistant MFA (SMS/Push).
- Review all OAuth grants for suspicious third-party applications with broad scopes like
Mail.ReadWrite.
- Week 2: Visibility
- Deploy infrastructure monitoring for "typosquatting" domains. Enforce a 72-hour rule: quarantine any email containing links to domains registered within the last three days.
- Tune SIEM logic to alert on session IP/ASN mismatches (e.g., residential ISP to hosting provider) within a single session lifecycle.
- Weeks 3–4: Hardening
- Pilot FIDO2/WebAuthn hardware keys or passkeys for high-risk groups.
- Enable Continuous Access Evaluation (CAE) and establish a "Revoke All Active Sessions" workflow as the primary response to identity alerts.
- Enforce device compliance policies that block login attempts from unmanaged or non-compliant devices, ensuring stolen tokens are useless on attacker machines.
Conclusion: Beyond the Perimeter
The rise of AiTM signifies a fundamental shift in the threat landscape. We have moved beyond "perimeter-based defense" into an era where identity and trust are the primary attack surfaces. The traditional security model assumes that a successful login equals a safe user. In the age of the session hijacker, that assumption is a liability.
In an era where your login looks legitimate but your session is stolen, do you have the visibility to see what happens after the "Access Granted" screen?