If a hacker gets past your password, what stops them next? If your answer is "nothing," you're in trouble! In GRC, we never rely on just one "shield." Instead, we use a strategy called Defense in Depth. 🛡️
Think of your business like a medieval castle protecting its crown jewels (your data). You wouldn't just lock the front door and go to sleep, right? You'd want a moat, high walls, guards on the towers, and a vault inside the keep.
In the digital world, we build three specific "walls" to protect the CIA Triad (Confidentiality, Integrity, and Availability) at the center.
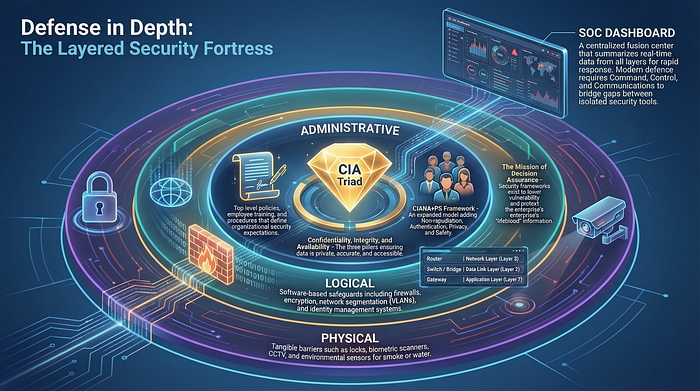
1. Administrative Controls (The Brain) 🧠: These are the people-facing rules. Think of this as the "law of the land" within your castle. If your people don't know the rules, the strongest gate in the world won't save you.
Examples: Clear security policies, thorough background checks for new hires, and regular "don't click that link" awareness training.
It builds a "human firewall." When employees are savvy, they become your first line of defense rather than your weakest link.
2. Logical/Technical Controls (The Digital Gate) 💻: This is the high-tech wizardry. These are safeguards built directly into your software and network to block digital intruders.
Examples: Firewalls, Encryption, Multi-Factor Authentication (MFA), and Intrusion Detection Systems (IDS).
These are the automated "traps" that catch hackers in the act, even if they've managed to sneak past the outer walls.
3. Physical Controls (The Outer Wall) 🧱: These protect the actual hardware and the ground you stand on. You can have the best encryption in the world, but it doesn't matter if someone can just walk into your server room and carry the computer away 😂 !
Examples: Locked doors, CCTV cameras, security guards, and even smoke detectors to protect against environmental risks.
It ensures that only authorized "knights" can get close to the kingdom's machinery.
It's All About Integration 🤝
Modern Defense in Depth isn't just about stacking layers and hoping for the best. It's about Integration.
These layers must "talk" to each other. Ideally, they are monitored by a Security Operations Center (SOC). When a Physical Control (like a door sensor) is triggered at 2 AM, the Logical Controls (the network) should immediately tighten up and alert the team.
When your walls work together, you don't just have a business, you have a fortress. 🏰✨
#GRC #CyberSecurity #DefenseInDepth #InfoSec #RiskManagement #SecurityCulture #Compliance #ISO27001 #DataProtection #BusinessResilience #TechSafety #CyberAwareness #InternalControls #SecurityArchitecture #SOC #FortressBusiness #RiskMitigation #Governance #CyberStrategy #ProtectYourData
