275 Million Students and Teachers Exposed. ShinyHunters Just Hit the Largest Educational Data Breach on Record.
8,809 universities worldwide. 3.65 terabytes of data stolen. Private messages between students and teachers. Harvard, Toronto, UBC, Virginia Tech — all hit during finals week. Here is everything we know.
Students trying to access their coursework during finals week were greeted with a message instead of their learning platform. Not a maintenance notice. A ransom note. "ShinyHunters rooting your systems since ཏ." That was the message that appeared on Canvas — the learning management system used by 41% of higher education institutions in North America — when students logged in on May 7, 2026.
The breach had actually begun on April 30, 2026, when ShinyHunters exploited a vulnerability in Instructure's cloud environment to gain unauthorised access. Instructure — the Utah-based company that owns Canvas — confirmed the incident on May 1. But the full scale only became public on May 7 when ShinyHunters defaced the Canvas login page, redirecting every user to their ransom demand and causing the platform to go offline globally.
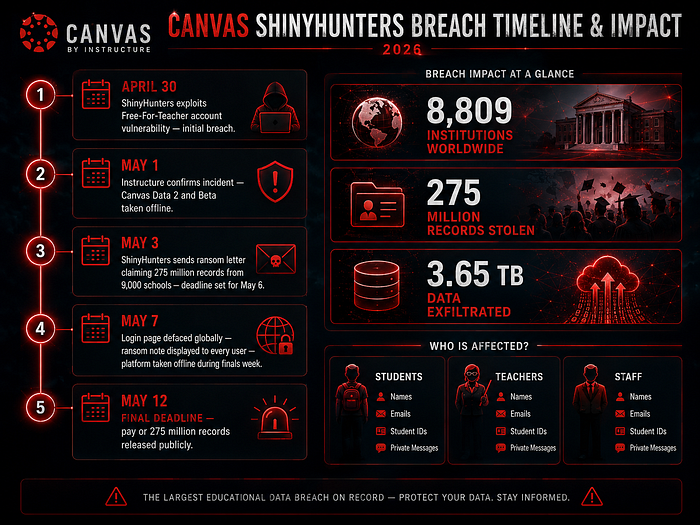
This is now confirmed as the largest educational security breach on record. 8,809 institutions worldwide. 275 million records stolen. 3.65 terabytes of data exfiltrated. And a deadline — May 12, 2026 — before ShinyHunters threatens to release everything publicly.
What Was Actually Stolen
Instructure has confirmed that the data accessed includes full names, email addresses, student ID numbers, and private messages exchanged between students and teachers. Canvas is used not just for sharing course materials — it is a communication platform where students and instructors discuss assignments, grades, personal circumstances, and sensitive academic matters. The private message dimension of this breach is what makes it significantly more serious than a typical credential leak.
Instructure has stated that there is no current evidence that passwords, financial information, government-issued identification, or dates of birth were compromised. However, the investigation is ongoing — and ShinyHunters claims to have 275 million records. The gap between what Instructure has confirmed and what ShinyHunters claims to hold is significant and will likely only narrow as forensic investigation continues.
How ShinyHunters Got In
The attack exploited a vulnerability in Instructure's Free-For-Teacher account system. Instructure confirmed in its statement that "the unauthorised actor exploited an issue related to our Free-For-Teacher accounts." The company revoked access after detecting the initial breach on April 30 — but additional activity was detected on May 7, prompting the full platform takedown.
ShinyHunters' own message to Canvas — published by Ransomware.live on May 3 — accused Instructure of attempting security patches after being contacted rather than negotiating. "ShinyHunters has breached Instructure again. Instead of contacting us to resolve it they ignored us and did some security patches." This language suggests prior contact and at least one earlier compromise attempt — consistent with the attack timeline beginning April 30.
The specific technical vulnerability in the Free-For-Teacher account system has not been publicly disclosed. Instructure has engaged law enforcement and external cybersecurity experts, implemented patches, rotated credentials, and increased monitoring. Canvas Data 2 and Canvas Beta remained in maintenance mode as of May 9.
Who Is ShinyHunters
ShinyHunters is not a new threat actor. The group — described by threat intelligence analyst Luke Connolly as a loose affiliation of teenagers and young adults based in the US and UK — has been active since 2019 and has a well-documented history of high-profile breaches. Previous targets include Ticketmaster, Google's Salesforce database, and Vimeo — the latter also targeted in the same May 2026 campaign, with ShinyHunters setting a May 30 deadline for Vimeo's ransom payment.
The group is financially motivated — their model is consistent: breach a high-value target, exfiltrate data, demand ransom, threaten public release if unpaid. Their May 2026 campaign represents a significant escalation in both scale and audacity — defacing a platform used by nearly a third of global higher education during finals week is a calculated pressure tactic designed to maximise urgency and force rapid payment decisions.
The Scale of Affected Institutions
The list of affected institutions is global and includes some of the most prominent universities in the world. In Canada: University of Toronto, University of British Columbia, University of Alberta, Western University's Ivey Business School, and Simon Fraser University. In the United States: Harvard University, Virginia Tech, institutions across North Carolina, California, and virtually every state where Canvas is the primary LMS. In the UK and Europe: thousands of additional institutions across Hackread's confirmed list of 15,000 affected organisations globally.
Canvas is the most widely adopted learning management system in North American higher education — used by 41% of institutions and serving approximately 30 million active participants. The breach hit during the worst possible moment: the end of the academic year, during or immediately after final examination periods at many institutions. Virginia Tech acknowledged the impact on end-of-semester activities. The University of Iowa's IT director described it as "a national-level cyber-security incident."
The Ransom Deadline and What Happens Next
ShinyHunters set a deadline of May 12, 2026. Their threat: pay an undisclosed ransom sum or face public release of all 275 million records plus "several annoying digital problems." Cybersecurity experts are unanimous in recommending against payment — not just on principle but on practical grounds. Paying ransom funds the development of new attack techniques, encourages continued targeting of educational institutions, and provides no guarantee that stolen data will not be sold or released regardless.
"It encourages the criminals to continue to look for new victims," said Connolly. "The payments actually fund their development of new techniques to exploit others." The decision ultimately rests with Instructure — students and institutions are, as Beauceron Security CEO David Shipley noted, "in an awful bind" because they depend on the platform to deliver services they could not afford to replicate independently.
What Students and Staff Should Do Right Now
Change your Canvas password immediately — even though Instructure has not confirmed password compromise, credential rotation is prudent given the scale of the breach and the uncertainty about what was fully accessed.
Enable multi-factor authentication on your Canvas account and any other education platform accounts if you have not already. MFA significantly reduces the impact of credential exposure even if passwords were compromised.
Notify your bank if you used your student email for any financial services. The combination of name, email, student ID, and private messages creates a profile usable for identity fraud and synthetic identity creation — particularly dangerous for students at the beginning of their financial lives with clean credit histories.
Sign up for credit monitoring — many breaches of this nature lead to identity theft attempts months or years later, long after the initial incident fades from memory. Early monitoring is the most reliable way to detect misuse before it compounds.
Be vigilant about phishing emails — the University of Toronto explicitly warned: "The university will never ask you to bypass your multi-factor authentication. If you receive an email requesting MFA bypass codes, please report it." Attackers frequently use breach data to craft highly targeted phishing campaigns against victims in the weeks following a major incident.
Reconsider social media information — Robert Falzon of Check Point Software recommends reviewing how much personal information is publicly visible on social media, including courses, location, and daily routines. Combined with the breached Canvas data, this information significantly increases the attack surface for targeted social engineering.
The Structural Problem This Breach Exposes
The Canvas breach is not just a story about one company failing to secure one platform. It is a story about the structural dependency of modern education on a small number of centralised technology vendors — and the catastrophic blast radius when one of those vendors is successfully attacked.
Cybersecurity expert Robert Falzon put it plainly: "It's not enough to have cybersecurity audits every once in a while, with breaches happening on a daily basis now. We need to start thinking very seriously about shortening those cycles." David Shipley went further — calling for stronger federal privacy laws and meaningful financial consequences for companies involved in breaches, similar to the substantial fines available under European data protection law. "Companies that actually face these kinds of sanctions up front will risk manage better. Absent consequences, profit-oriented private companies are going to make money. They are not going to spend on security."
275 million people did not choose to put their data on Canvas. They were required to use it by their institutions, which were required to use it by the economics of educational technology. The accountability for this breach sits with Instructure — but the structural conditions that made it possible sit with an industry that has consistently underinvested in security relative to the sensitivity of the data it holds.
The May 12 deadline is approaching. Whether Instructure pays or not, 275 million people's data is already in the hands of a group that has shown no hesitation in monetising breached information. The immediate priority is mitigation — for the individuals affected, and for every institution still evaluating its dependency on centralised education technology platforms.

