1. Project Overview
This project demonstrates a vulnerability assessment conducted using Nessus from a Kali Linux machine against a Metasploitable target system in a controlled lab environment.
2. Ethical Consideration
This assessment was conducted in a controlled lab environment using intentionally vulnerable systems. No unauthorized systems were scanned.
3. Tools Used
- OS (Attacker Machine): Kali Linux • Vulnerability Scanner: Nessus Essentials • Target Machine: Metasploitable 2 • Virtualization Platform: VMware
4. Network Setup and Connectivity Verification
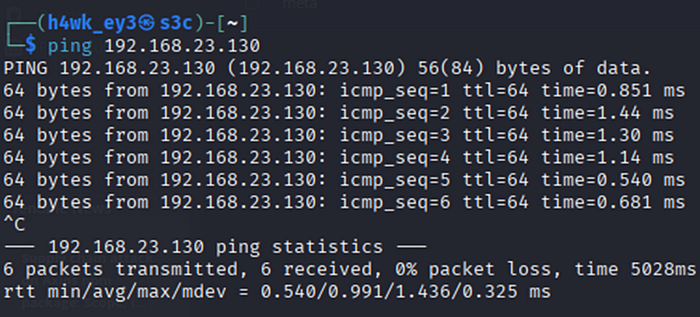
Before initiating the scan, network connectivity between the Kali Linux machine and the Metasploitable target was confirmed. The target IP address was identified using ifconfig on the Metasploitable machine, and a ping test from Kali Linux was used to verify that both systems could communicate.
Target IP Address
The ifconfig command was run on the Metasploitable machine. The target was found at 192.168.23.130.

Ping Test from Kali Linux
A ping test to 192.168.23.130 was run from Kali Linux. All 6 packets were received with 0% packet loss, confirming successful communication between the two machines.
5. Scan Configuration
- Scan Type: Advanced Scan • Target: 192.168.23.130 • Credentials: SSH • Severity Base: CVSS v3.0 • Scan Start: Today at 10:08 AM • Scan End: Today at 10:26 AM • Elapsed Time: 19 minutes
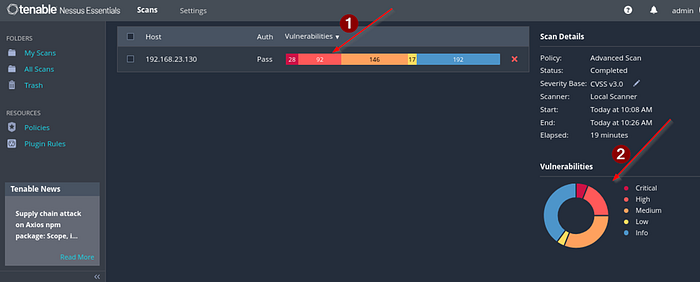
6. Summary Scan Results
The scan completed successfully with authentication passed. A total of 475 vulnerabilities were identified across all severity levels as shown in the table below.
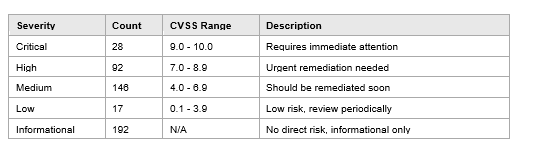
Completed Scan Overview
The screenshot below shows the Nessus dashboard after the scan was completed. Arrow (1) points to the vulnerability severity bar for the scanned host, showing the count per severity level. Arrow (2) points to the donut chart on the right, which gives a proportional breakdown of vulnerabilities by severity category.
7. Critical Vulnerabilities Identified
The scan returned 28 critical vulnerabilities. The screenshot below lists the top critical findings sorted by severity, spanning vulnerability categories including Backdoors, Gain a Shell Remotely, and Service Detection.

Notable Critical Findings
• Backdoors (CVSS 10.0): A backdoor was found in the UnrealIRCd IRC server, allowing an attacker to execute arbitrary code remotely without authentication.
• Gain a Shell Remotely (CVSS 10.0 / 9.8): Multiple vulnerabilities allow full remote shell access to the system.
• Service Detection (CVSS 9.8): Dangerous services were found running on open ports, leaving the system exposed to known exploits.
8. Investigation of One of the Critical Vulnerabilities Found
One of the critical vulnerabilities was investigated further. The finding is the UnrealIRCd Backdoor Detection (Plugin ID: 46882), rated Critical with a CVSS v2.0 Base Score of 10.0. It is classified under the Backdoors family and is a remote type of vulnerability.
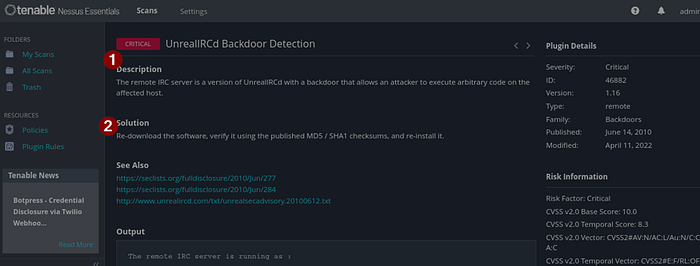
Description (1)
The remote IRC server is running a version of UnrealIRCd that contains a backdoor. The backdoor was deliberately inserted into the source code and allowed any remote attacker to execute arbitrary commands on the affected system without needing any credentials.
Impact
An attacker who exploits these backdoor gains full remote code execution on the target. This can result in complete system compromise, data theft, and the ability to move laterally across the network.
Solution (2)
The affected version of UnrealIRCd should be removed immediately. The software should be re-downloaded from the official source and its integrity verified using the published MD5 or SHA1 checksums before reinstalling.
9. Relevance to SOC Operations
This exercise reflects practical tasks that a SOC analyst carries out as part of a vulnerability management program. Scanning systems with Nessus, reviewing severity ratings, and investigating specific findings are all core blue team activities. Understanding what a backdoor means in terms of risk helps analysts prioritize alerts and respond appropriately. Working through a finding like UnrealIRCd also builds awareness of how attackers use compromised software to gain access, which is useful when reviewing logs or responding to incidents.
10. Conclusion
This assessment covered the full process from network verification to vulnerability scanning and investigation. The Metasploitable 2 target produced 475 vulnerabilities in total, with 28 rated Critical. The UnrealIRCd backdoor stood out as the most severe finding, with a CVSS score of 10.0. Exercises like this help build the practical skills needed for vulnerability management and strengthen an overall security posture.
The ifconfig command was run on the Metasploitable machine. The target was found at 192.168.23.130.