A Secure by Design architecture assumes that any single security layer might fail. If your code scanner misses a bug, your container scanner should catch the vulnerable library. If the container scanner misses it, your Admission Controller should block the unsigned image. 🛑
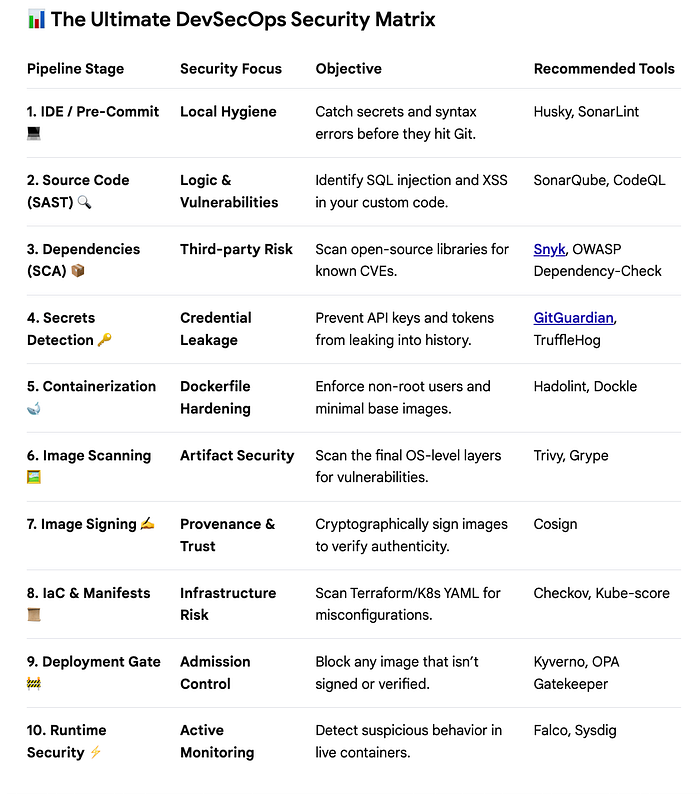
Here is the blueprint for a hardened, end-to-end DevSecOps pipeline.
🌟 The Three Pillars of a Hardened Production Environment
While the tools above cover the "how," these three strategies define the "why":
1. Image Provenance (The "Identity Card") 🆔
In high-security environments, you cannot trust an image just because it exists in your registry. By using Cosign, you create a digital signature during the build process. Your Kubernetes cluster can then be configured to refuse to run any container that doesn't carry your organization's unique signature.
2. Software Bill of Materials (SBOM) 📑
If a new zero-day vulnerability like Log4j is discovered tomorrow, do you know which of your 500 microservices are at risk? Tools like Syft generate an SBOM (a nutritional label for your software). This allows security teams to query their entire infrastructure instantly to find affected versions.
3. Policy as Code (The "Automatic Guardrail") 🛣️
Human error is the leading cause of cloud breaches. By using Checkov or Kyverno, you turn security policies into code. For example, you can write a policy that says: "No container can ever run as root." If a developer tries to deploy one, the pipeline simply fails, providing immediate feedback.
🏁 Final Thoughts
Security is not a checkbox at the end of a sprint; it is an ongoing, automated process. By embedding these tools into your CI/CD pipeline, you empower your developers to move fast without breaking your security posture. 🛡️✨
Which of these stages is your team currently missing? Start small — perhaps with a secrets scanner — and build your way to a fully hardened pipeline. 🛠️🦾