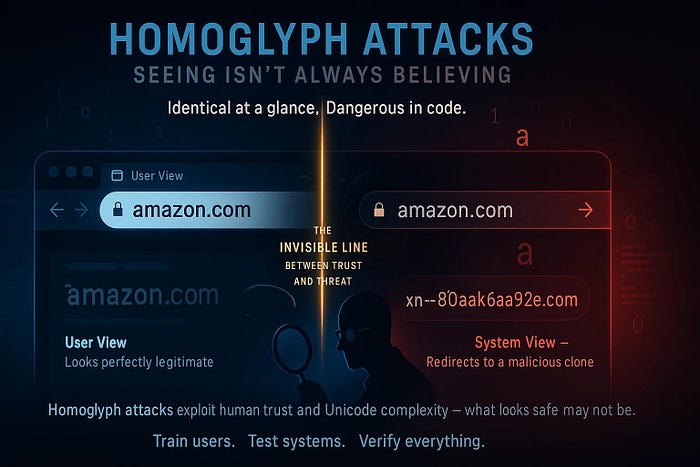
In the world of cybersecurity, we often tell users to "trust the URL." We teach them to look for the green lock (SSL) and verify the domain name. However, a sophisticated exploit known as a Homograph Attack (or Script Spoofing) proves that even our eyes can be deceived by the very protocols meant to protect us.

At its core, a Homograph Attack exploits the Internationalized Domain Names (IDN) system. To support non-Latin scripts (like Cyrillic, Greek, or Arabic), the internet uses Unicode.
The vulnerability arises because many characters in these scripts are homoglyphs — they are graphically identical to Latin letters but possess entirely different digital identities.
- Latin "a" (U+0061) vs. Cyrillic "а" (U+0430)
- Latin "p" (U+0070) vs. Cyrillic "р" (U+0440)
To a human, apple.com and аpple.com are indistinguishable. To a DNS resolver, they are two unrelated destinations.
2. Case Studies: Exploiting Trust at Scale
This is not a theoretical threat; it has been weaponized against the world's most trusted brands:
- The 2017 Apple Incident: A security researcher demonstrated that by registering an IDN, he could force browsers to display a perfectly spoofed
apple.com. Because he owned the domain, he was able to obtain a Valid SSL Certificate, adding a false layer of "HTTPS security" to a fraudulent site. - The ɢoogle.com Analytics Scam: By using the "Latin Small Letter Capital ɢ" (U+0262), attackers successfully bypassed spam filters to appear in Google Analytics reports, leading unsuspecting webmasters to malicious landing pages.
- Widespread Phishing: Platforms like WhatsApp, Adobe, and Facebook have all faced variants of these attacks, where the goal is typically credential harvesting or malware distribution.
3. Punycode: The Digital "True Face"
To maintain compatibility with the older ASCII-only DNS infrastructure, the internet uses Punycode. This system translates Unicode domains into an ASCII-compatible format starting with the prefix xn--.
Visual URL:
gоdaddy.com(using a Cyrillic 'o') Punycode Reality:xn--gdaddy-qof.com
Modern browsers have implemented "IDN Display Policies" to mitigate this. If a domain contains characters from multiple different scripts (e.g., mixing Latin and Cyrillic), the browser should automatically revert to displaying the Punycode version to alert the user.
4. Mitigation Strategies for the Modern SOC
As security professionals, we cannot rely solely on user education. Defending against homograph attacks requires a multi-layered approach:
- Browser Standardization: Ensure all corporate assets use browsers with strict IDN policies that force Punycode display for mixed-script domains.
- Credential Management: Deploy Enterprise Password Managers. These tools compare the digital string of the domain, not the visual appearance, and will refuse to auto-fill credentials on a spoofed site.
- Egress Filtering & Threat Intel: Use DNS-layer security (like Cisco Umbrella or Quad9) that flags and blocks known malicious Punycode domains before the connection is even established.
- FIDO2/WebAuthn: Move toward Passwordless Authentication. Since these methods bind the authentication to the specific origin/domain, they are mathematically immune to homograph-based phishing.
The Homograph Attack is a reminder that in cybersecurity, identity is not always what it appears to be. As we build more complex systems, the gap between human perception and machine logic becomes a playground for attackers.