Introduction
In digital design, unexpected behavior is common.
Sometimes it is a design flaw. Sometimes it is something far more deliberate.
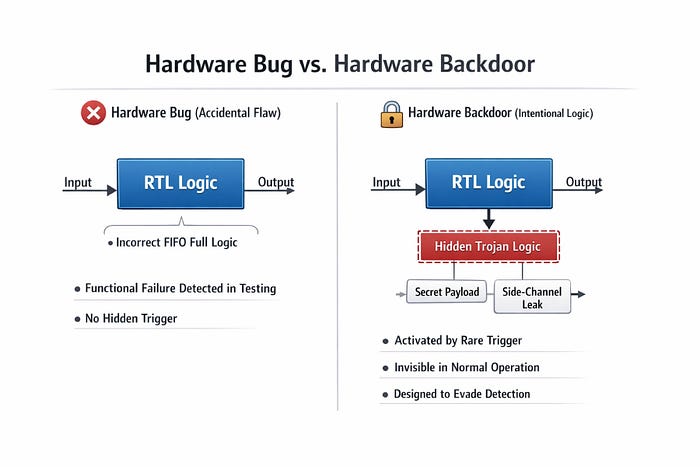
Understanding the distinction between a hardware bug and a hardware backdoor is critical for engineers building secure silicon.
1. What Is a Hardware Bug?
A hardware bug is an unintended defect in the design.
It may arise from:
- Incorrect RTL logic
- Timing violations
- Metastability or CDC errors
- Reset sequencing issues
- Misinterpreted specifications
These issues emerge naturally in complex systems.
Example: FIFO Pointer Error
Consider a synchronous FIFO using MSB-based full detection:
full = (wr_ptr[MSB] != rd_ptr[MSB]) && (wr_ptr[MSB-1:0] == rd_ptr[MSB-1:0])If pointer rollover is mishandled, the FIFO may falsely assert full or empty. The design behaves incorrectly. But there was no intent.
A bug is a reliability issue.
2. What Is a Hardware Backdoor?
A hardware backdoor (often categorized under hardware Trojans) is intentionally inserted logic that:
- Remains dormant under normal operation
- Activates under rare conditions
- Produces behavior not specified in the design
Unlike bugs, backdoors are engineered to evade detection. They have small footprint, hidden side-channel effects, minimal impact on functional tests and is activated by a hidden trigger.
Example patterns include:
- Extra combinational logic gated by a rare key sequence
- Ring oscillators inserted to modulate dynamic power
- Hidden state machines that activate after N cycles
The design passes simulation and regression tests. But under specific conditions, hidden logic activates.
3. Why Detection Is Hard
Both bugs and backdoors may manifest as unexpected power variation, or with timing anomalies, or have rare incorrect outputs
Distinguishing bug and backdoor requires:
- Structural analysis
- Formal verification
- Side-channel inspection
- Supply chain integrity
4. Why This Is a Silicon-Level Problem
In silicon, once fabricated, malicious logic becomes physically embedded in the chip. In globally distributed fabrication models, ensuring silicon integrity becomes as important as ensuring RTL correctness.
Conclusion
In the end, the difference between a hardware bug and a hardware backdoor is not just technical, it is philosophical. A bug is an accident born from complexity, an error we work to find, understand, and fix. A backdoor is intentional, designed to hide, to bypass trust, and to exploit the very systems meant to be secure.
As systems grow more complex and globally built, understanding this distinction becomes essential for anyone designing, verifying, or relying on modern hardware.
About the Author
Surabhi Misra is an ASIC Design Engineer based in San Jose, working on high-performance digital hardware. She has hands-on experience with RTL design, verification, and building silicon used in networking and cloud-scale systems. Surabhi developed an interest in hardware security during her graduate research at USC, where she worked on logic locking and hardware Trojan exploration. She enjoys breaking down complex chip security concepts into simple explanations for students and beginners. When she is not designing hardware, she writes about VLSI, hardware security, ASIC careers, and engineering growth.