👋 Hey Everyone!
I'm Ch4ndan Das First of all, thank you very much for the support on my previous articles. I am genuinely trying to share my bug hunting experiences to help others — especially beginners. Please ignore any small mistakes and focus on the value.
Lets start !
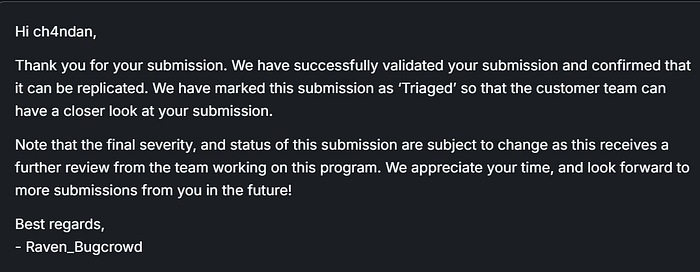
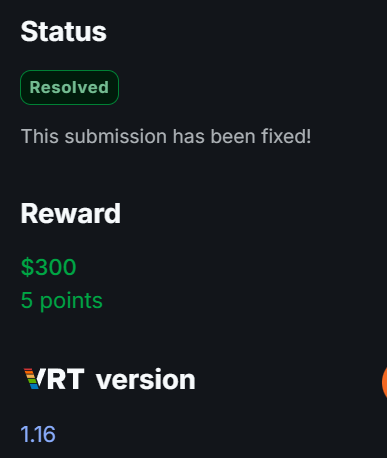
I selected a target on Bugcrowd — let's call it target.com — and started testing the registration functionality. If you also want to find this type of bug, you first need to understand the application's logic.
Summary:
The mobile application does not properly validate the OTP (One-Time Password) during the registration or login process. An attacker can bypass the OTP verification step and gain unauthorized access to an account without entering a valid OTP.
Steps to Reproduce
- Go to https://target.com/en/home
- Enter a mobile number and request the OTP.
- Enter an incorrect OTP.
- Capture the request using Burp Suite.
- Change
"method":"verify"to"method":"login"in the request.

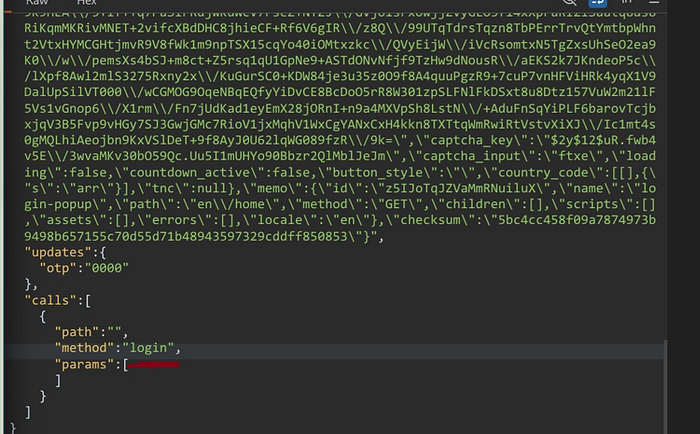
6. Send the request and observe that the OTP verification is bypassed.