Authentication is everywhere, from logging into your email to accessing APIs. One of the most popular modern methods is JWT (JSON Web Token).
But what actually happens behind the scenes?
Let's break it down in the simplest way possible.
What is JWT?
JWT (JSON Web Token) is a compact, secure way to transmit information between two parties — usually a client (frontend) and a server (backend).
It is:
- Stateless (no session stored on server)
- Compact (easy to send in headers)
- Secure (digitally signed)
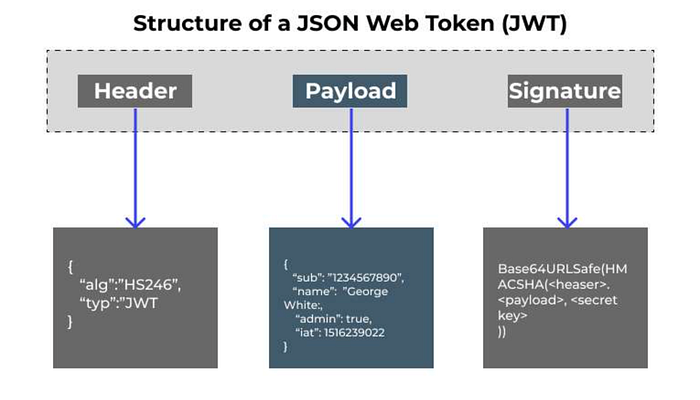
Structure of a JWT
A JWT consists of 3 parts, separated by dots:
xxxxx.yyyyy.zzzzzHeader
Contains metadata about the token.
{
"alg": "HS256",
"typ": "JWT"
}Payload
Contains the actual data (claims).
{
"userId": "123",
"email": "user@example.com",
"role": "admin"
}Important: This is not encrypted, only encoded.
Signature
Ensures the token is not tampered with.
HMACSHA256(
base64UrlEncode(header) + "." + base64UrlEncode(payload),
secret
)How JWT Authentication Works (Step-by-Step)
Step 1: User Logs In
User sends credentials (email/password) to the server.
Step 2: Server Validates User
Server checks:
- Is the user valid?
- Is the password correct?
Step 3: JWT is Created
If valid, the server generates a JWT:
- Includes user data (payload)
- Signs it using a secret key
Step 4: Token Sent to Client
Server sends the JWT back to the frontend.
Step 5: Client Stores Token
Stored in:
- LocalStorage (common)
- Cookies (more secure)
Step 6: Client Sends Token with Requests
Every request includes:
Authorization: Bearer <token>Step 7: Server Verifies Token
Server:
- Verifies signature
- Checks expiry
- Extracts user info
If valid → request allowed
Common Misconceptions
JWT is encrypted
No, it is encoded, not encrypted.
JWT is always secure
Only if:
- You use HTTPS
- You store it safely
- You use short expiry
Best Practices for JWT
- Use short expiration time
- Implement refresh tokens
- Never store sensitive data in payload
- Use HTTP-only cookies (for better security)
- Always use HTTPS
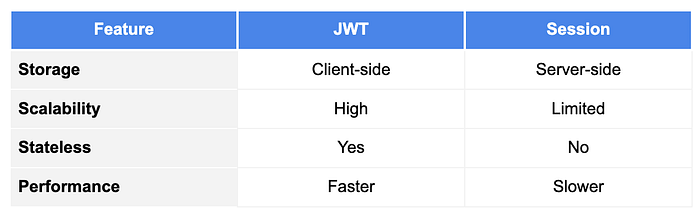
JWT vs Session-Based Authentication
When Should You Use JWT?
Use JWT when:
- Building REST APIs
- Working with microservices
- Need stateless authentication
Avoid JWT when:
- You need immediate logout control
- Security requirements are very strict
Real-World Example
Imagine logging into an app:
- You log in → server gives JWT
- You browse pages → token sent automatically
- Server verifies → gives access
No need to log in again
Conclusion
JWT makes authentication:
- Fast
- Scalable
- Stateless
But it must be used carefully to avoid security risks.
If you understand JWT, you understand how modern authentication works.

