"IPv4 addresses finished, so IPv6 came." 🫠
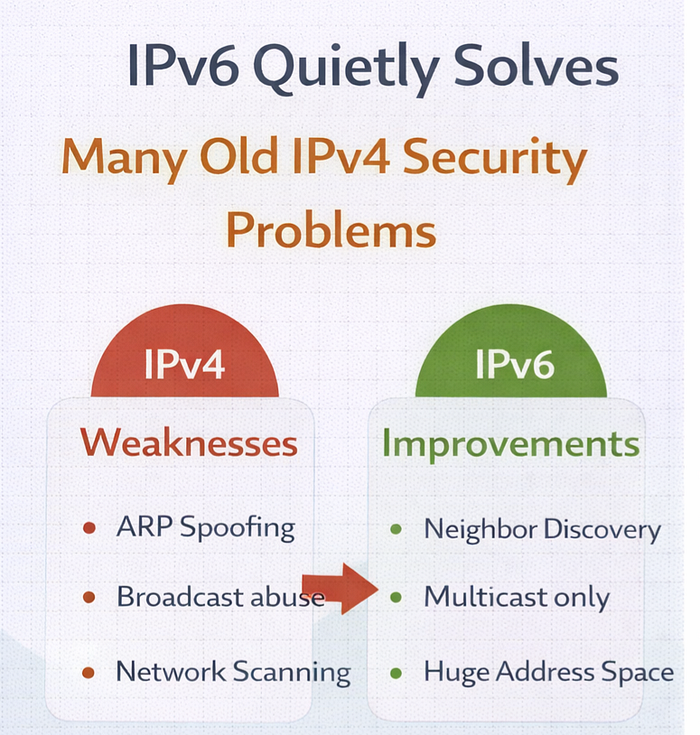
That is only half the story. The real story is more interesting. For 40+ years, attackers abused design weaknesses in IPv4 — weaknesses that were never meant to face today's internet scale. Protocols like ARP, Broadcast, NAT tricks, DHCP dependence, header manipulation — all became favorite playgrounds for attackers. IPv6 was not just created to give more IPs. It was designed to remove these old weak points from the network itself. So, IPv6 does not magically make a network secure. But it removes many insecure design shortcuts that IPv4 depended on. Let's see now together what real security problems IPv6 reduces or completely eliminates.
1. Death of ARP Spoofing (Man-in-the-Middle)
In IPv4 networks, devices use ARP (Address Resolution Protocol) to find the MAC address of an IP. ARP has no authentication. Any attacker inside the LAN can say: "I am the gateway" — And all devices believe it.
This is how tools like arpspoof, ettercap, and dsniff perform Man-in-the-Middle attacks. IPv6 completely removes ARP. Instead, it uses Neighbor Discovery Protocol (NDP),😌 which runs over ICMPv6 and supports SEND (Secure Neighbor Discovery) — cryptographic verification of neighbor messages. The entire class of ARP poisoning attacks becomes extremely difficult.
2. No Broadcast = No Broadcast Abuse
IPv4 heavily uses broadcast messages like: "Who has this IP? Tell everyone!"
This leads to: Broadcast storms, Easy network mapping, Smurf attacks, Amplification attacks
IPv6 removes broadcast completely. It uses multicast and anycast, meaning devices only listen to relevant traffic. Many network abuse techniques die automatically.
3. Network Scanning Becomes Practically Impossible
In IPv4, an attacker can scan an entire subnet in seconds:
nmap 192.168.1.0/24
But in IPv6, a normal subnet is /64, which contains: 18,446,744,073,709,551,616 addresses. You cannot scan this. It's mathematically impractical. Attackers can no longer "discover" hosts easily. They must depend on DNS leaks, logs, or other intelligence. This is a huge defensive advantage.
4. NAT Problems and UPnP Risks Are Gone
Because IPv4 ran out of addresses, NAT was introduced. NAT broke end-to-end connectivity. What is UPnP read here -> https://www.upguard.com/blog/what-is-upnp
Applications started using ugly workarounds: UPnP opening ports automatically, Port forwarding, STUN/TURN hacks. Many users never knew their router was exposing ports. IPv6 removes NAT requirement. Every device gets a global IP. Firewall rules become clear and controlled. No more accidental exposure through UPnP.
5. Built-in IPsec Support
In IPv4, IPsec is optional and rarely implemented properly. IPv6 was designed with IPsec support as part of the protocol architecture.
This allows:
- Packet authentication
- Encryption at network layer
- Anti-spoofing mechanisms
Even if not always enabled, the protocol natively supports secure communication.
6. DHCP Spoofing Risks Reduced with SLAAC
In IPv4, attackers can run fake DHCP servers and assign:
- Wrong gateway
- Wrong DNS
- Their system as MITM
IPv6 allows devices to self-generate IP using SLAAC (Stateless Address Auto Configuration). Less dependence on DHCP reduces this attack surface.
7. Simplified Header = Easier Firewall Inspection
IPv4 headers contain many fields attackers abuse using fragmentation, checksum tricks, and TTL manipulation. IPv6 simplifies the header and moves optional data into extension headers. Firewalls can inspect traffic more cleanly. Packet manipulation becomes harder.
8. Smurf and Broadcast Amplification Attacks Become Impossible
Read about these attacks here — https://www.cloudflare.com/learning/ddos/smurf-ddos-attack/
These attacks depended entirely on IPv4 broadcast behavior. Since IPv6 has no broadcast, these attack types simply cannot exist.
9. Better Logging and Traceability
In IPv4, hundreds of users sit behind one NAT IP. Tracking becomes messy. In IPv6, every device has a unique global IP. Logging, auditing, and forensic tracking becomes more accurate.
10. Security Monitoring Tools Gain Better Visibility
Security tools can monitor NDP messages and detect:
- Rogue router advertisements
- Fake neighbors
- Suspicious devices
This visibility was very weak in ARP-based IPv4 networks.
Buttttttt please remember an important Reality Check 😅 IPv6 is not automatically secure If firewalls are not configured properly, IPv6 can expose devices directly to the internet because NAT is gone.
But from a protocol design perspective, IPv6 removes many weaknesses attackers exploited for decades.
Conclusion
IPv4 was designed for a small academic network.
IPv6 is designed for a hostile, global internet.
IPv4 needed patches like NAT, ARP protection, DHCP snooping, broadcast control. IPv6 removes the need for many of these patches by fixing the design itself.
Because IPv6 is not just the future of addressing.
It is the future of network security design.