A cloud security case study in unauthenticated deployment, auth bypass logic bugs, and what it teaches every bug bounty hunter about where real vulnerabilities hide
Imagine this. A security researcher is exploring a cloud deployment platform — the kind developers use daily to push live applications to production. The interface is polished. The documentation is thorough. The authentication flow looks exactly as it should: login required, session validated, access controlled.
But the researcher doesn't test the front door. They test the side entrance.
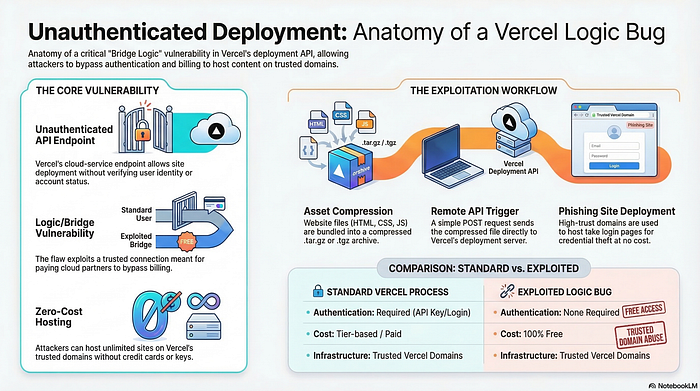
Specifically, they begin probing the deployment pipeline itself — not the dashboard, not the login form, but the underlying API endpoints responsible for actually triggering a deployment. And somewhere in the logic that connects "authenticated user" to "authorized action," they find a gap. A request that should require a verified identity. Doesn't.
This is the anatomy of an unauthenticated deployment vulnerability — a class of cloud security flaw that sits at the intersection of auth bypass and business logic failure. And it's more common than the industry admits.
The myth most developers and even junior security researchers believe is that authentication and authorization are the same layer. They're not. That confusion is exactly where this category of bug bounty finding lives.
The Myth: If Authentication Exists, Authorization Is Covered
This is the foundational misunderstanding that makes logic bugs in cloud platforms so persistently exploitable.
When a platform is built, authentication — verifying who you are — is usually implemented early and carefully. Login flows get security reviews. Password handling gets scrutinized. Multi-factor mechanisms get layered in. The front door gets a deadbolt.
What gets less attention is authorization — verifying what you're allowed to do after identity is established. And in complex cloud platforms with multiple services, internal APIs, webhook endpoints, and CI/CD integrations, the authorization layer isn't a single gate. It's a mesh of individual checks scattered across dozens of components.
Each of those components was probably built by a different team, at a different time, under different assumptions about what the calling service had already verified.
Intellectual insight: Authentication is a door. Authorization is every room inside the building. Builders spend most of their time on the door — and leave room-level locks inconsistent, assumed, or missing entirely.
How Unauthenticated Deployment Becomes Possible
To understand how a deployment can be triggered without valid authentication, you need to understand how modern cloud deployment pipelines are structured.
A typical flow works something like this: a developer pushes code, a webhook fires, a build service receives the signal, validates the payload, and initiates a deployment to the appropriate environment. Each handoff in that chain involves a trust assumption — that the previous step already verified what needed to be verified.
Now consider a realistic scenario. A cloud platform exposes an internal API endpoint designed to accept deployment trigger requests from its own build infrastructure. Because this endpoint was originally intended for internal service-to-service communication, it was built with the assumption that only trusted internal callers would ever reach it. Authentication was considered unnecessary — or was deferred.
At some point, the architecture evolves. The platform adds external integrations. The endpoint becomes reachable from outside its original network boundary. The team that built the integration layer assumes the endpoint has its own auth. The team that owns the endpoint assumes the integration layer enforces auth before passing requests through.
Neither team is wrong about their own component. But the gap between them is now externally exploitable.
A researcher who sends a correctly structured deployment request to that endpoint — with a valid project identifier that can be enumerated or guessed — triggers a real deployment. No session token. No API key. No authentication challenge of any kind.
Intellectual insight: The most dangerous assumption in distributed system security isn't "this is secure" — it's "someone else already checked." Responsibility diffusion is a vulnerability class, not just an organizational problem.
What the Bug Actually Looks Like From a Hunter's Perspective
This is where the case study becomes instructive for anyone building their bug bounty skillset.
The vulnerability isn't visible from the application's user interface. The dashboard is fully authenticated. Every visible workflow requires a logged-in session. A surface-level review — the kind that checks login forms and session cookies — would find nothing unusual.
The finding only becomes possible through a specific research behavior: mapping the platform's full API surface rather than testing only what the authenticated UI exposes.
In practice, this means intercepting requests made during normal authenticated use, identifying the underlying API calls the frontend makes on behalf of the user, and then systematically testing those endpoints in isolation — without the session context the frontend normally provides.
When a researcher strips the authentication headers from a deployment trigger request and the server processes it anyway, that's the moment the bug becomes visible. The server's response changes from an error to a success. A deployment actually initiates.
What makes this category particularly impactful from a security perspective is the blast radius. An unauthenticated deployment capability doesn't just affect the researcher's own account. Depending on how project identifiers are structured, it could potentially allow any external actor to push arbitrary deployments to any project — overwriting production environments, injecting malicious code into live applications, or disrupting services at scale.
Intellectual insight: High-severity logic bugs rarely announce themselves. They look like normal traffic until you remove one layer of context and notice the server doesn't care. The habit of testing endpoints in isolation — not just in authenticated flow — is what separates surface hunters from deep finders.
Why Cloud Platforms Are Uniquely Exposed to This Vulnerability Class
Cloud deployment platforms occupy an unusual position in the security landscape. They are simultaneously developer tools, infrastructure providers, and trust brokers between code repositories and live production environments.
This combination creates an attack surface that is broader, more layered, and more assumption-dependent than most web applications.
Traditional web applications have a relatively contained request lifecycle. A user interacts with a UI, a server processes the request, a response returns. Cloud platforms add CI/CD pipelines, webhook receivers, build runners, deployment orchestrators, environment managers, and API gateways — each with its own request handling, each making assumptions about what upstream components have already validated.
The more components in a system, the more seams exist. The more seams, the more opportunities for the kind of trust gap that makes unauthenticated deployment possible.
For a bug bounty hunter, this is actionable intelligence. When scoping a cloud platform target, the highest-value areas to investigate aren't the obvious authenticated surfaces — those receive the most internal scrutiny. The highest-value areas are the integration points: webhook endpoints, build trigger APIs, deployment status callbacks, environment provisioning flows, and any endpoint that appears to be designed for service-to-service communication rather than direct user interaction.
These endpoints were built for convenience and speed. Security was often secondary. And in bug bounty programs, secondary security is frequently synonymous with first discovery.
Intellectual insight: The attack surface of a cloud platform isn't the product you see — it's the infrastructure underneath the product. Hunt the plumbing, not the facade.
What This Case Study Teaches About Cloud Security Thinking
The researchers who find bugs like this aren't necessarily more technically advanced than those who don't. They think differently about where problems are likely to exist.
They start from the assumption that complex systems contain trust gaps. They look for seams between components. They test not just "can I access this?" but "does this component assume I've already been checked by something else?" They remove authentication context deliberately and observe whether behavior changes.
This is cloud security thinking applied as a research methodology — and it's learnable.
For defenders, the lesson is equally clear. Every API endpoint in a cloud platform needs its own authorization check, independent of what the calling service claims to have already verified. Trust between internal services should be explicit and cryptographically enforced, not assumed based on network position or request structure.
The deployment door that nobody checked wasn't left open out of negligence. It was left open because everyone assumed someone else had the key.
In distributed systems, assumptions are the vulnerability. Verification is the patch.
In 48 hours, I'll reveal a simple bug-prioritization checklist most hunters skip — the one that tells you which endpoints on a cloud platform are statistically most likely to have an authorization gap before you spend a single minute testing them.
Found this useful? Follow for deep-dive breakdowns of real-world cloud security logic flaws, auth bypass patterns, and the bug bounty methodology that surfaces high-severity findings on modern platforms. Share this with a developer or security researcher who needs to see where the real risk lives.
💬 Comment Magnet