Introduction
Hi everyone, my name is Sachin Aneja, and I work as a Senior Cyber Security Technical Analyst. I also pursue bug bounty hunting part-time, and this is my first blog post — so please excuse any mistakes.
In this post, I'll walk you through a Stored XSS vulnerability caused by iframe injection discovered in a program's Privacy Notice Management module, along with its impact and recommended mitigation strategies.
Vulnerability Overview
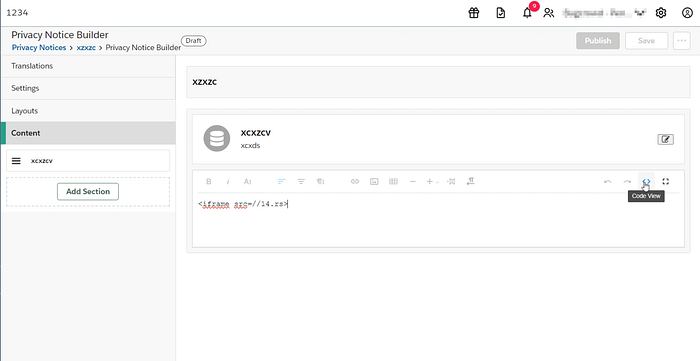
The application provides a Privacy Notice Builder feature that allows privileged users to create and manage privacy notices. This builder includes a code view option, enabling users to directly insert HTML content.
Due to improper input sanitization, this feature is vulnerable to Stored XSS, allowing arbitrary HTML (including <iframe>) to be injected and executed.
Steps to Reproduce:
The issue can be reproduced by logging into the application using a privileged user account and navigating to the Privacy Notice Management section at the specified URL. After creating a new privacy notice, the user proceeds to the builder and adds a new section. Within the section editor, switching to the code view allows insertion of a malicious payload such as an iframe.
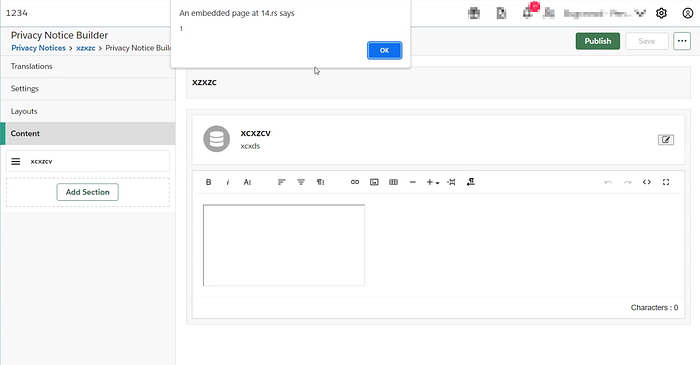
Once the changes are saved, the payload gets stored and is automatically executed whenever the affected section is rendered, confirming the presence of a stored XSS vulnerability.
💥 Impact
This vulnerability allows attackers to inject malicious content that executes in the context of other users viewing the privacy notice.
Potential impacts include:
- 🔓 Session Hijacking
- 🎭 Phishing Attacks via Embedded Content
- 🧠 Credential Theft
- 🛠 Defacement of Application Content
- 🔗 Loading External Malicious Resources
Because this is a stored XSS, the payload persists and affects all users who access the affected content, making it more dangerous than reflected XSS.
Root Cause
The vulnerability exists due to:
- Lack of input sanitization in code view editor
- Allowing unsafe HTML tags like
<iframe> - Missing Content Security Policy (CSP) restrictions
- Improper output encoding
Key Takeaways
- Rich text editors are high-risk components if not properly secured
- "Trusted users" can still become attack vectors
- Stored XSS can have wide-reaching impact across users and sessions
Conclusion
This vulnerability highlights how seemingly useful features like code editors can introduce severe security risks if not properly controlled. Organizations must enforce strict validation, sanitization, and browser-level protections to prevent such attacks.
Proactively testing these features during security assessments can help uncover hidden vulnerabilities before attackers do.