ow I Discovered and Exploited Business Logic Flaws in Modern Web Applications
👨💻 About Me
Hi, I'm Montaser — a security researcher and bug bounty hunter passionate about discovering real-world vulnerabilities in modern web applications.
I focus primarily on business logic flaws, race conditions, and access control issues, as they often lead to impactful vulnerabilities that are overlooked by traditional security testing.
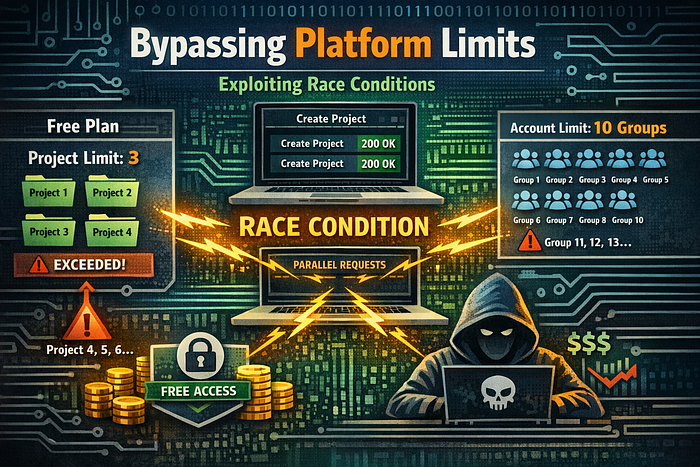
In this article, I'll walk you through two real-world vulnerabilities I discovered, both involving race conditions that allowed me to bypass platform-enforced limits.
⚡ Understanding Race Conditions
A race condition occurs when multiple requests are processed at the same time, and the system fails to properly synchronize them.
This can lead to unexpected behavior — especially when the application relies on checks like:
- Limits (e.g., number of projects or groups)
- Balances
- Permissions
If these checks are not atomic, they can be bypassed.
🧩 Vulnerability #1: Bypassing Project Limits
📍 Overview
In this case, a platform restricted free-tier users to a maximum of 3 projects per organization.
However, I discovered that this limit could be bypassed using concurrent requests.
🔍 Root Cause
The backend performed a quota check like:
"Does the user have less than 3 projects?"
But the issue was:
- The check was not atomic
- Multiple requests were validated at the same time
- Each request passed before the database was updated
🛠️ Exploitation Steps
Here's how I exploited it:
- Created an organization with fewer than 3 projects
- Intercepted the project creation request
- Sent it to a repeater tool
- Duplicated the request 20–50 times
- Used a parallel request tool to send them simultaneously
💥 Result
- All requests returned 200 OK
- The organization ended up with 11 projects instead of 3
🚨 Impact
This vulnerability allowed:
- Bypassing subscription limits
- Using paid features for free
- Breaking billing logic
- Potential large-scale abuse
This is a serious business logic flaw affecting platform integrity.
🧩 Vulnerability #2: Group Limit Bypass
📍 Overview
In another platform, users were limited to 10 groups per account.
But using the same race condition technique, I was able to exceed this limit.
🔍 Root Cause
Similar to the first case:
- The system checked the number of groups
- But did not enforce the check atomically
- Concurrent requests bypassed the restriction
🛠️ Exploitation Steps
- Logged into a normal user account
- Ensured I had fewer than 10 groups
- Intercepted the group creation request
- Sent it to a repeater/intruder
- Fired 20–25 parallel requests
💥 Result
- All requests succeeded
- The account ended up with 24 groups instead of 10
🚨 Impact
This issue could lead to:
- Abuse of platform resources
- Circumvention of product limitations
- Performance degradation
- Exploitation of group-based features at scale
🧠 Why These Bugs Matter
Race conditions are often underestimated because:
- They don't rely on complex payloads
- They don't require special access
- They are easy to automate
Yet, they can directly impact:
- 💰 Revenue (bypassing paid plans)
- ⚙️ System stability
- 📊 Business logic integrity
🛡️ How to Fix These Issues
To prevent such vulnerabilities, developers should:
- Use atomic operations for quota checks
- Implement database transactions
- Apply row-level locking
- Re-validate constraints after insertion
- Add rate limiting for sensitive endpoint
Thanks for reading 🙏 I'll keep sharing more from my bug bounty journey.
Feel free to connect or share your thoughts
Facebook: https://facebook.com/montasermohsen98 Twitter (X): https://x.com/Montaser_M98 LinkedIn: https://linkedin.com/in/montasermohsen98