The counter-intuitive truth about Bug Bounty 2026 that most beginners discover too late — and how to find your first valid bug without years of preparation
Picture this. A beginner spends six months deep in tutorials. They've watched hundreds of hours of web hacking content, taken multiple courses, bookmarked every resource they can find, and built what feels like a solid foundation. Then they finally open a real bug bounty program — and freeze.
The scope feels overwhelming. Every endpoint looks either already tested or impossibly complex. After two hours of aimless clicking, they close the tab and go back to studying.
Three months later, they're still studying.
This is the story of almost every beginner who enters the Bug Bounty space in 2026. And the myth driving this pattern is seductive: "I just need to learn a little more before I start hunting."
The tension here isn't a skill gap. It's a validation problem. Beginners aren't failing because they lack knowledge — they're failing because they've never been taught how to apply imperfect knowledge in a real environment. More courses aren't the answer. A different approach entirely is.
The Myth That Keeps Beginners Studying Forever
The most damaging belief in the bug bounty beginner community is that expertise is a prerequisite for participation.
This belief feels logical. Web hacking sounds advanced. Terms like SQL injection, server-side request forgery, and broken access control carry a weight that makes newcomers feel like outsiders. So they study longer, stack more certifications, and keep delaying the moment they actually open a live program and start testing.
Most beginners study broadly when they should be studying deeply and specifically. A working understanding of one vulnerability class — how it occurs, where to look for it, and how to test it manually — is more valuable for finding that first payout than a shallow familiarity with twenty different attack types.
Consider a realistic example. A beginner spends three focused weeks learning only how web applications handle user-supplied input in search fields and URL parameters. They understand the concept well enough to recognize when input is being reflected without proper encoding. They open a program with a broad scope, filter for older or less glamorous targets that other hunters might overlook, and find a basic reflected cross-site scripting issue on a forgotten subdomain. It gets triaged. It gets paid.
That beginner didn't know everything. They knew one thing well enough to act on it.
Intellectual insight: Depth of application beats breadth of awareness. Your first valid bug will almost never come from your widest knowledge — it will come from your deepest.
Why "Harder Targets" Is a Beginner's Trap
There's a cultural pull in the bug bounty community toward prestige targets — the programs run by large, well-known technology companies with high payout tables and competitive hunters.
Beginners see the big numbers and assume that's where the opportunity lives. In reality, those programs are saturated with experienced hunters who have been testing those same assets for years. The low-hanging fruit has been picked, re-picked, and documented thoroughly.
The counter-intuitive move for a beginner in 2026 is to go where experienced hunters aren't.
This means looking at programs that have recently expanded their scope, applications that are less visually polished and more likely to have legacy code underneath, or targets in industries that don't attract as much attention as fintech or social media platforms. Less glamorous doesn't mean less vulnerable — it often means the opposite.
A beginner who tests a mid-sized e-commerce application's recently added affiliate portal has a fundamentally different experience than one who attempts to find bugs in a hardened, heavily audited core product. The affiliate portal might have been built quickly, tested internally only, and never seen a serious outside security review. That's where access control gaps, insecure direct object references, and logic flaws quietly live.
Intellectual insight: Prestige and opportunity are inversely correlated for beginners. The target that excites you the most is probably the one that will teach you the least and pay you nothing. The boring target might be your first paycheck.
The Skill You Actually Need First: Reading Applications, Not Breaking Them
Most web hacking education focuses on attack techniques. Inject this. Bypass that. Intercept here. This creates hunters who know how to execute attacks but don't know how to read an application well enough to know where attacks might land.
The foundational skill for any beginner in bug bounty is application mapping — the practice of understanding what an application does before deciding how to test it.
Before touching a single parameter, walk through the target as an ordinary user. Create an account. Use every feature. Notice what changes in the URL. Observe where the application takes your input and reflects it back. Look at how different user roles interact with the same resources. Ask the question: "What is this feature supposed to do — and what would happen if it did something slightly different?"
This mindset shift — from attacker to observer first — changes what you notice. Logic flaws, broken access controls, and privilege escalation issues become visible not through technical exploitation frameworks but through careful functional observation.
A beginner who spends forty-five minutes mapping a web application before testing it will find more than one who spends three hours throwing automated tools at endpoints without understanding what those endpoints are supposed to do.
Intellectual insight: The best bug bounty hunters are exceptional readers of software behavior. Technical exploitation is the last step, not the first. Learn to read before you learn to break.
Reporting Is a Skill — And Most Beginners Ignore It Until It's Too Late
Finding a potential vulnerability is only half the work. Getting it triaged, validated, and paid requires a report that communicates the issue clearly and demonstrates its real-world impact.
This is where many beginners lose money they technically earned.
A vague report — "I found an XSS on this page, here's the URL" — often gets downgraded or rejected not because the bug is invalid, but because the triage team can't quickly understand the severity or reproduce the issue from the description provided.
A strong beginner report answers four questions without making the reader search for them: What is the vulnerability? Where exactly does it exist? How can it be reproduced step by step? And what could an attacker realistically do with it?
Writing this clearly takes practice, and the only way to build that practice is to write reports — even for bugs you find on practice labs and intentionally vulnerable applications. The habit of structured documentation, built early, separates hunters who get consistent payouts from those who find valid bugs and watch them get closed as informational.
Intellectual insight: Triage teams are busy. A report that respects their time by being precise and complete will consistently outperform a technically superior finding buried in a confusing wall of text. Communication is a technical skill in bug bounty.
Where to Actually Start in 2026
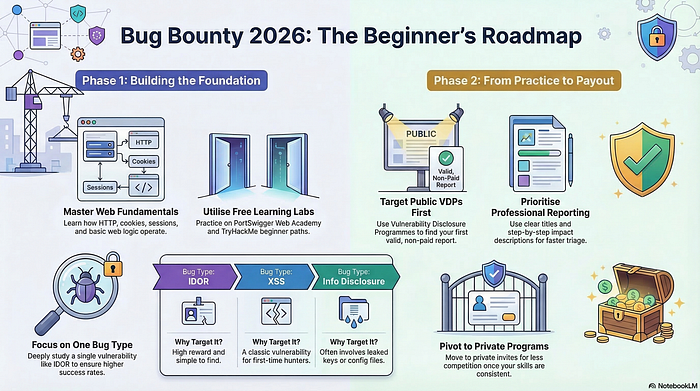
The roadmap is simpler than the industry makes it sound.
Pick one vulnerability class. Understand it conceptually and mechanically. Practice finding it in legal, intentional environments built specifically for this purpose — there are several freely available platforms designed for exactly this kind of skill development. Then take that single skill to a real program with a manageable scope.
Write your first report, even if it gets rejected. Read the feedback. Adjust. Try again.
The hunters earning consistent income from bug bounty in 2026 are not the ones who know the most — they're the ones who started the earliest, failed the fastest, and built systems around their learning. They stopped waiting to feel ready and started letting real programs teach them what no course ever could.
The knowledge you need exists. The programs are waiting. The only variable still under your control is when you decide to stop preparing and start hunting.
In 48 hours, I'll reveal a simple vulnerability-scoring checklist most beginners skip — the one that tells you whether a target is worth your time before you spend a single hour testing it.
Found this useful? Follow for weekly breakdowns of the bug bounty mindset, web hacking fundamentals, and the beginner strategies that actually translate into real results. Share this with someone stuck in the endless learning loop — this might be the nudge they need.
💬 Comment Magnet