Your organisation likely needs offensive security testing. Regulators increasingly expect it: NDPR in Nigeria, POPIA in South Africa, and sector-specific requirements from banking and telecommunications authorities across the continent. Boards and auditors increasingly expect evidence of such testing. But knowing you need penetration testing is not the same as knowing how to buy it well.
Too many enterprises face a capability gap: they lack in-house offensive security expertise, which means they also lack the knowledge to evaluate vendors, scope engagements correctly, or translate technical findings into business action. The consequences are predictable. Organisations overpay for generic assessments that miss context-specific risks. Reports arrive dense with technical jargon, then gather dust because no one owns remediation. Compliance boxes get ticked while actual vulnerabilities persist. In Sub-Saharan Africa alone, organisations experience an average of 3,325 cyberattacks per week, 72% above the global average, highlighting the need for proactive, well-managed security programmes
The offensive security market can be confusing. Vendors range from internationally certified specialists to operators with impressive websites but little substance behind them. Pricing varies widely for ostensibly similar services. Proposals use terminology that sounds authoritative but obscures whether the work actually matches your risk profile.
Our Recently Published Offensive Security Policy Guide is Designed to Help You Bridge This Gap

It is not a technical manual for conducting penetration tests per se, although it does provide guidance on that. Most critically, it is a procurement and management guide for organisations that need to buy offensive security services intelligently, oversee engagements effectively, and convert findings into measurable security improvements.
We cover how to evaluate vendors and identify genuine capability versus marketing. How to scope engagements so you test what matters without wasting budget on what does not. How to manage testing engagements from rules of engagement through to final reporting. How to build remediation workflows that ensure findings translate into fixes. And critically, how all of this intersects with African regulatory requirements that international frameworks rarely address.
As part of Spurt!'s work building operational infrastructure for scaling businesses in emerging markets, this guide helps organisations implement offensive security programmes that are systematic, context-aware, and effective.
The goal is not to make you an offensive security practitioner. It is to make you an informed buyer; someone who knows what questions to ask, what answers to expect, and what outcomes to demand. Here is a brief teaser:
1. Evaluating vendors: Not all certifications carry equal weight. The guide explains which credentials matter — OSCP, CREST, CHECK and which are marketing noise. It provides questions to ask during procurement, red flags to watch for in proposals, and a framework for checking references. Trade-offs between regional vendors who understand local context and international firms with deeper technical specialisation are also addressed.
2. Scoping engagements correctly: Most scoping failures fall into predictable patterns: too broad (wasting budget on low-value targets), too narrow (missing critical assets), or wrong test type entirely. The guide helps you match test types to your actual risk profile, understand what "black box" versus "white box" means for your budget and outcomes, and make informed decisions about testing in production versus staging environments.
3. Managing the engagement: Once testing begins, clear protocols prevent confusion and minimise operational risk. Templates for rules of engagement, communication and escalation protocols, access provisioning and revocation procedures, and guidance on responding to critical findings mid-engagement are included.
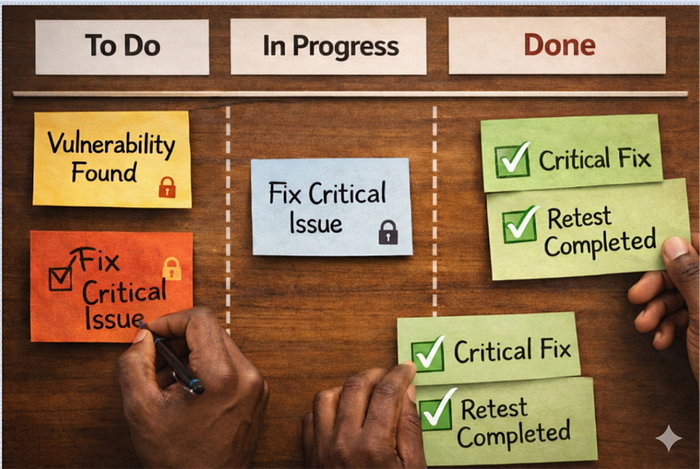
4. Moving from report to remediation: This is where most programmes fail. Pentest reports arrive, get filed, and nothing changes. The guide addresses why this happens and how to prevent it: translating technical findings into prioritised action plans, assigning ownership, tracking remediation progress, and planning verification retests.
5. Building an ongoing programme: Security testing is not a one-off exercise. Guidance is provided on determining testing cadence based on asset criticality, planning budgets across financial years, considering vendor rotation, and integrating testing with your compliance calendar.
6. Navigating African regulatory requirements: International frameworks rarely address local nuances. The guide explains what NDPR requires in Nigeria, POPIA's implications in South Africa, sector-specific mandates from banking and telecommunications regulators, and how data localisation rules affect where testing can be performed and by whom
Okay You've Made It This Far, How Do You Get Started?
Download the full guide to begin building or strengthening your offensive security programme. If you need support scoping your next assessment, evaluating vendor proposals, or turning existing findings into remediation plans, our team can help.
Download the Offensive Security Policy Guide
Contact us at security@spurt.solutions


