﴿ وَقَالُوا أَإِذَا كُنَّا عِظَامًا وَرُفَاتًا أَإِنَّا لَمَبْعُوثُونَ خَلْقًا جَدِيدًا﴾ [ الإسراء: 49]
Over View :
This is a classic horizontal privilege escalation via IDOR.

Let's start simple port scan recon with nmap

Oh, We have open Apache server on port 80 Let's check it out :
http://10.112.171.234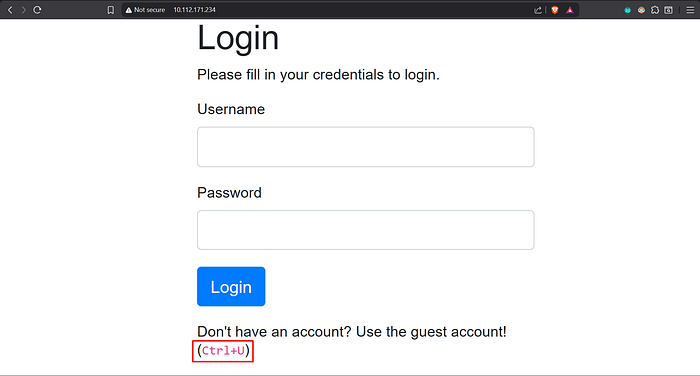
Let's press "CTRL + U" to see the source code of this page.
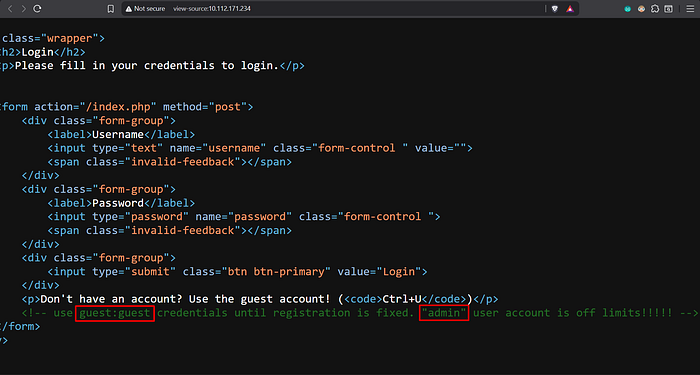
Now We Know 2 information :
1- Username: guest / Password: guest 2- There are another username called "admin"
Let's login with our credentials :
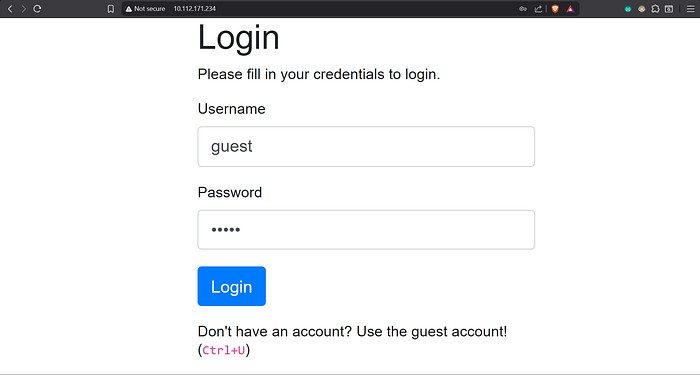
Then press "Login"

As we can see … we get initial access with our guest:guest credentials and we are currently in :
http://10.112.171.234/profile.php?user=guestWe can notice that our username passed to the parameter "user"
So, What if we change it to :
http://10.112.171.234/profile.php?user=admin
📊 Track Your Progress
If you're learning on TryHackMe and want to stay organized, I created this sheet to track Easy Machines (free + paid) 👇
https://docs.google.com/spreadsheets/d/15V-qZEig58Tr6Cp0Q_KQsFfD-U_37P7huv118T70qUk/edit?usp=sharing
You can use it to:
- Track your progress step by step
- Add your own notes
- Stay consistent while learning
Feel free to take a copy and edit on it 🙌