1. The Authentication Landscape: More Than Just Synonyms
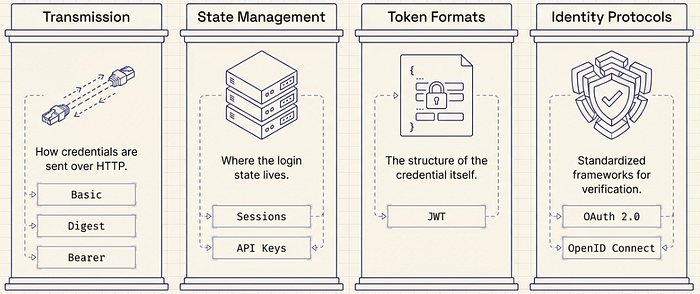
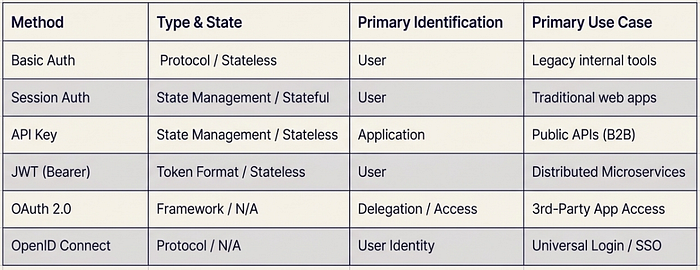
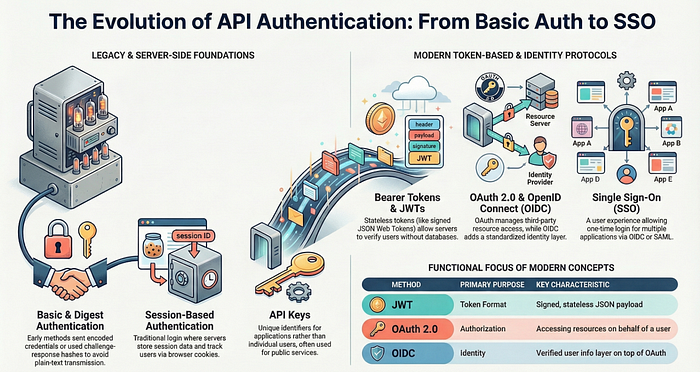
Architectural failure in modern systems often stems from the conflation of distinct security concepts. API keys, JWTs, and OAuth are not interchangeable; they serve different roles within a security stack. Distinguishing between credential transmission, state management, and identity protocols is required to build secure, horizontal-scaling systems. The landscape is defined by four categories:
- Credential Transmission: The mechanism used to send data over HTTP (e.g., headers).
- Login State Management: The logic determining how a system maintains an authenticated session.
- Token Formats: The data structure used to carry information (e.g., JSON).
- Identity Protocols: The frameworks governing authentication and authorization (e.g., OIDC).
Understanding these distinctions requires a look at the legacy foundations of authentication.
2. The Early Foundations: Basic and Digest Authentication
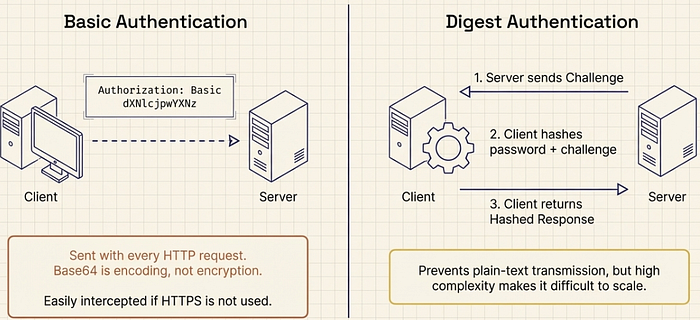
Legacy authentication relied on request-level credentials. These methods were designed for internal systems and early web architectures where simple headers provided sufficient access control.
Basic Authentication transmits a username and password in the HTTP authorization header, encoded in Base64. Because Base64 is an encoding format rather than encryption, the credentials are functionally plain-text unless wrapped in TLS.
Digest Authentication introduced a challenge-response mechanism to mitigate the risks of plain-text transmission. The server provides a "nonce" (a unique challenge value), and the client returns a hashed response combining the password and the challenge. This ensures the raw password never traverses the network.
The "So What?" Layer Basic Auth remains a high-risk method for production environments due to the constant re-transmission of sensitive credentials. While Digest Auth improved security through hashing, it failed to scale. The emergence of TLS (HTTPS) rendered the "password-over-the-wire" problem moot for many internal use cases, while the rise of modern tokens provided a more flexible alternative to complex challenge-response handshakes.
3. State vs. Identity: Session Authentication and API Keys
Modern application development introduced a strategic trade-off: managing state on the server versus identifying clients through static keys.
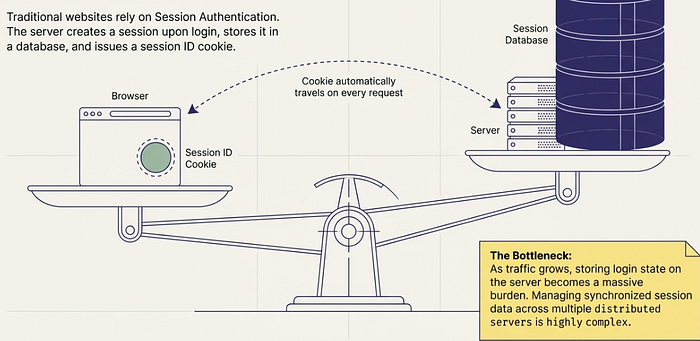
Session Authentication is stateful and cookie-based. Upon login, the server generates a session stored in memory or a database and passes a session ID to the client via a cookie. The server must validate this ID against its store for every request.
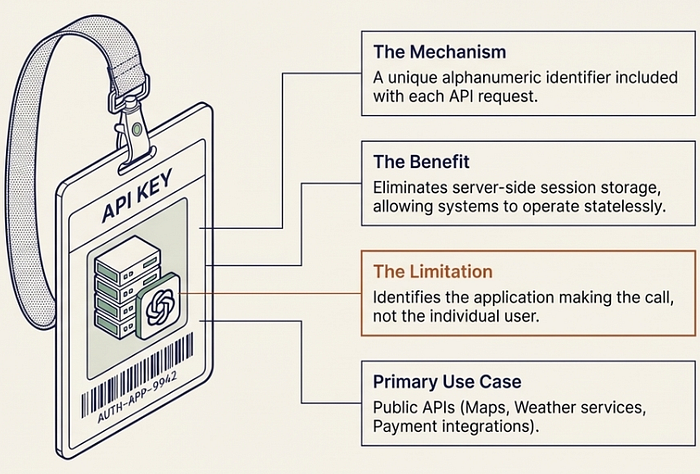
API Keys are unique identifiers assigned to an application or developer. They are transmitted with each request to identify which application (e.g., a payment gateway, weather service, or map provider) is accessing the API, rather than which individual user.
The "So What?" Layer Session authentication creates a significant scaling bottleneck. In distributed environments, stateful sessions require sticky sessions (directing users to the same server) or a centralized session store like Redis, both of which introduce architectural complexity and latency. Conversely, API keys identify the software calling the service, making them insufficient for user-level identity without being paired with other mechanisms.
4. The Stateless Revolution: Bearer Tokens and JWTs
In microservices architectures, statelessness is a primary design goal. Shifting from "asking the database" to "holding the token" allows services to verify requests independently.
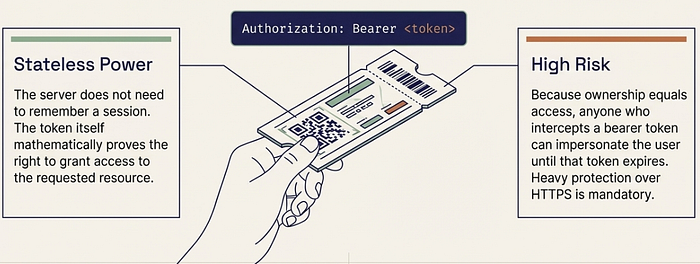
Bearer Authentication grants access to whoever "bears" the token. While often used interchangeably with JSON Web Tokens (JWTs), Bearer is the transmission mechanism and JWT is the format. A JWT is a digitally signed, self-contained JSON object. Because the signature confirms the token's integrity, the recipient can trust the data without a database lookup.
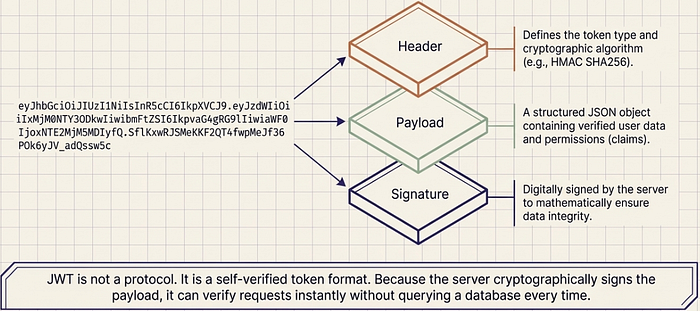
The "So What?" Layer The self-contained nature of JWTs eliminates the database bottleneck in distributed systems. However, because bearer tokens are sensitive, they require a strict lifecycle managed through access and refresh tokens.

5. Delegated Authority and Identity: OAuth 2.0, OIDC, and SAML
Security has shifted from simple logins to delegated authority — permitting applications to act on a user's behalf without accessing their password.
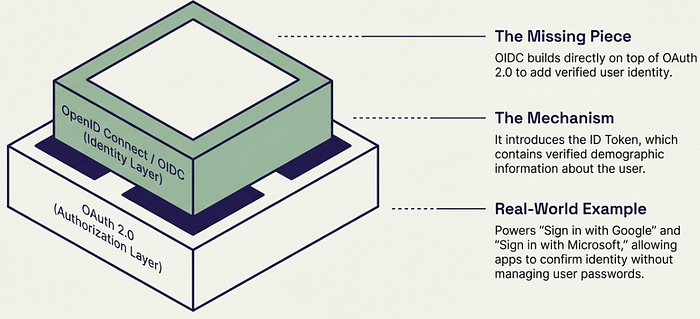
OAuth 2.0 is an authorization framework designed for this delegation. It manages what an application can do (e.g., read a Google Drive file). However, OAuth 2.0 is not an identity protocol.
OpenID Connect (OIDC) builds on top of OAuth 2.0 to provide an identity layer. It introduces the ID Token, which contains verified user information. This framework, alongside SAML (Security Assertion Markup Language), enables Single Sign-On (SSO). SSO is a user experience (UX) that allows a single authentication event to grant access across a suite of independent applications.
The "So What?" Layer Implementing OIDC or SAML offloads the risk of password management to specialized providers (Google, Microsoft, Okta). This ecosystem allows for "Sign in with…" functionality, providing a seamless identity experience while maintaining strict authorization boundaries via OAuth.
6. Conclusion: Synthesizing the Authentication Stack
Authentication has transitioned from credential transmission to decentralized identity governance. The modern stack is a layered approach where the transmission method (Bearer), the token format (JWT), and the identity protocol (OIDC) work in tandem to ensure security and scalability.